Magic Security Dust
Schneier on Security
APRIL 1, 2024
Adam Shostack is selling magic security dust. It’s about time someone is commercializing this essential technology.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 about adam
about adam 
Schneier on Security
APRIL 1, 2024
Adam Shostack is selling magic security dust. It’s about time someone is commercializing this essential technology.
Adam Levin
APRIL 9, 2021
Adam Levin spoke with NPR about the recent data archive of over 500 million Facebook accounts found on a hacking forum. The post Adam Levin Discusses Facebook Data Leak on NPR appeared first on Adam Levin. The post Adam Levin Discusses Facebook Data Leak on NPR appeared first on Adam Levin.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Adam Shostack
JANUARY 28, 2021
For Data Breach Today, I spoke with Anna Delaney about threat modeling for issues that are in the news right now: “Does your organization have a plan in place if one of your employees is accused via Twitter of being an insurrectionist? If your software was being used to spread plans for a riot, could you detect that?

Adam Levin
MARCH 16, 2020
Adam Levin provides tips on how to protect your smartphone and your data from hackers. The post It’s Time to Get Smarter About Our Smartphones – Third Certainty #14 appeared first on Adam Levin.

Schneier on Security
NOVEMBER 10, 2021
In 1999, Adam Shostack and I wrote a paper discussing the security challenges of giving people devices that included embedded secrets that needed to be kept from those people. We were writing about smart cards, but our lessons were general. And they’re no less applicable today.

Adam Levin
FEBRUARY 7, 2020
“To avoid being tricked by criminals, stick to legal streaming platforms and subscriptions to ensure you can enjoy a nice evening in front of the TV without having to worry about any threats,” said Kaspersky malware analyst Anton Ivanov in a press release announcing the company’s findings. .

Adam Levin
MAY 1, 2020
W]e can safely infer that people who get tested are interested in learning more about potential treatments, medicine, medical best practices, and maybe even other patient’s experiences… those spending more time online looking for information about COVID-19 are more likely to fall prey to scams and malware related to Coronavirus,” the report stated.

Adam Levin
OCTOBER 16, 2020
The email also indicated that customer transaction histories may have been compromised, meaning that information about their purchases may be included in the breached data. The post Barnes & Noble Experiences Major Data Breach appeared first on Adam Levin.

Adam Levin
AUGUST 21, 2020
Carnival has declined to provide further details or information about the type of ransomware used to compromise their systems, the severity of the breach, or the nature of the information that was accessed, indicating that it is still “early in the investigation process.”. Read the 8-K filing here.

Adam Levin
OCTOBER 22, 2019
In the seventh episode of Third Certainty, Adam Levin explains the dangers of exposed personally identifiable information and shares some tips about how consumers can protect themselves. The post The DoorDash Data Breach – Third Certainty #7 appeared first on Adam Levin.

Security Boulevard
AUGUST 24, 2022
Chris Pierson recently participated in a webinar on what small businesses get wrong about cybersecurity and how to avoid common mistakes. Adam Gladsden, head of cybersecurity solutions at Swiss Re, a global provider of reinsurance and other protections […].

Adam Levin
MARCH 18, 2019
They’re laundering money,” said CyberScout founder and chairman Adam Levin. “So Find out more about employment scams here. The post Employment Scams Increasingly Targeting Job Seekers appeared first on Adam Levin. So they come up with all these scams to launder the money effectively.”.
Troy Hunt
MARCH 25, 2022
And such a wonderful woman in @charlottelyng 😊 🚁 💍 pic.twitter.com/NEgDxZxNeR — Troy Hunt (@troyhunt) March 24, 2022 I talked a bunch about Okta today and shortly after, jumped in the car and turned on the latest Risky Business podcast. Here's this week's vid, enjoy!

The Security Ledger
OCTOBER 14, 2022
In this episode of the Security Ledger podcast, brought to you by ReversingLabs, we interview Danny Adamitis (@dadamitis) of Black Lotus Labs about the discovery of ZuoRAT, malware that targets SOHO routers – and is outfitted with APT-style tools for attacking the devices connected to home networks. Read the whole entry. »

Adam Levin
SEPTEMBER 11, 2018
Adam Levin spoke with Columbus Business First at BizJournals about the recent cyber attack which hit an Ohio property management group. The post Adam Levin discusses Ohio Cyberattack with BizJournals appeared first on Adam Levin. Read the article here.
Adam Levin
SEPTEMBER 4, 2020
Information about the widespread data collection was initially brought to the public’s attention in 2013 by Edward Snowden, a government whistleblower who fled to Russia after exposing evidence of the program. . The post NSA Mass Surveillance Program Is Ruled Illegal appeared first on Adam Levin. Bush and Barack Obama. .

CyberSecurity Insiders
MAY 4, 2023
says Adam Nolen, VP Business Development at Cyberpress, “our offering saves outreach time and effort, making communications for cybersecurity companies easier, simple and under one roof” According to Nolen, “Our goal is to provide a reliable and efficient platform that helps businesses improve their marketing and communications strategy.

CyberSecurity Insiders
MAY 8, 2023
says Adam Nolen, VP Business Development at Cyberpress, “our offering saves outreach time and effort, making communications for cybersecurity companies easier, simple and under one roof” According to Nolen, “Our goal is to provide a reliable and efficient platform that helps businesses improve their marketing and communications strategy.

The Last Watchdog
MARCH 29, 2022
I’ve recently had several deep-dive discussions with cybersecurity experts at Juniper Networks, about this. And the very same mindset persists today, perhaps even more so, as companies increasingly rely on open-source software to keep pace, observes Kate Adam, Juniper Network’s senior director of security product marketing.

Adam Levin
JUNE 12, 2020
Emails with the subject line “Vote anonymous about ‘Black Lives Matter’” have been sending a variant of TrickBot, a trojan-style program designed to steal credentials and data from computers running Windows. The post Hackers Exploit Black Lives Matter to Spread Malware appeared first on Adam Levin.

Adam Shostack
JANUARY 25, 2021
It would be trite writing to say it was fun to be on a podcast with Volko Ruhnke and Hadas Cassorla to talk about using games to teach. Volko Ruhnke, Adam Shostack and Hadas Cassorla – Building Games to Teach Real-World Security. And while it was, it was really educational and inspirational.

SiteLock
AUGUST 27, 2021
Logan Kipp and Adam Warner have taken on this role with a passion, and continue to foster partnerships and ongoing education within the community. If you haven’t already met them, Logan and Adam are the ones attending and speaking on behalf of SiteLock at various WordCamps throughout the year. What’s Next?

Adam Levin
DECEMBER 2, 2020
Of particular concern is the popularity of the Minecraft franchise with children and young adults, who are often less cautious about the apps they choose to install. . The post Malware, Adware Disguised As Minecraft Mods Infect Over 1 Million Android Devices appeared first on Adam Levin.

Adam Levin
AUGUST 5, 2020
The NSA has issued a cybersecurity advisory about the use of location data on personal devices, social media accounts, mobile applications, as well as Internet of Things-enabled devices. The post NSA Issues Cybersecurity Advisory on Protecting Location Data appeared first on Adam Levin.
Adam Shostack
SEPTEMBER 17, 2020
Jim writes in footnote 2: Adam Shostack, who has written extensively on threat modelling and has provided feedback on this guide takes credit for the three question structure. ” I don’t disagree with Adam that we need to reflect and improve on the outcomes of our threat modelling. when someone makes noise about it.
Troy Hunt
FEBRUARY 16, 2021
This tweet from Adam Fowler that I embedded in the IoT blog series linked above perfectly explains the problem: I was looking at doing exactly this with my downlights, but the idea of the wall switch annoyed me - if it's off, I can't then voice turn on the lights. We worked that out back in the 19th century and everything was fine.

The Last Watchdog
MARCH 28, 2023
The founder, Adam Dennis (that’s me!), so that they can get the word out about the project. Feel free to visit AntiguaRecon on LinkedIn , the web , or email me at adam@antiguarecon.com. About the essayist: Adam Dennis the founder of AntiguaRecon. It is not enough to just educate the students.

Adam Levin
MARCH 29, 2019
The database belonged to Verifications.io, an “email validation service” that aggregates and sells information about the validity and associated personal data associated with email lists. The post Nearly One Billion Emails Exposed in Data Breach appeared first on Adam Levin. Verifications.io

Adam Levin
JANUARY 3, 2019
Read more about the story here. The post Suspected Hack Disrupts Major Newspapers appeared first on Adam Levin. The company also announced that they had reported the incident to the FBI, and that no customer information was compromised in the attack.

Adam Levin
NOVEMBER 13, 2018
This is to enhance our thinking about credit as cyber becomes more and more important,” said Derek Valda, head of Moody’s Investors Services Cyber Risk Group. Read more about the story here. The post Moody’s to Include Cyber Risk in Credit Ratings appeared first on Adam Levin.

Adam Levin
OCTOBER 8, 2019
The FBI is warning businesses about a new series of cyberattacks that can circumvent multi-factor authentication (MFA). The post FBI Warns of Cyber Attacks on Multi-Factor Authentication appeared first on Adam Levin. Read the PIN here.

Adam Levin
APRIL 10, 2019
Aite declined to identify the companies behind the apps researched or say whether they had warned the companies about the security holes discovered in their apps. Read more about their report’s findings here. The post Report Shows Major Security Holes in Banking Apps appeared first on Adam Levin.

Adam Levin
OCTOBER 2, 2020
Ads with false or conflicted claims about health risks associated with in-person voting. elections, where widespread activity by Russian “troll farms” and misleading or false claims about candidates were thought to have influenced voter behavior. The post Facebook Tightens Restrictions on Election Ads appeared first on Adam Levin.

Adam Levin
NOVEMBER 5, 2018
FIFA president Gianni Infantino spoke about the breach last week while in Rwanda, saying that he expects private information to be released. Read more about the story here. The post FIFA Hacked Again appeared first on Adam Levin.

Adam Levin
APRIL 22, 2019
While the CIR’s purpose is to eliminate several bottlenecks currently affecting border control and law enforcement, many are concerned about its privacy and security implications. “[U]nlike The post EU To Build Massive Biometric Database appeared first on Adam Levin.

CyberSecurity Insiders
MAY 31, 2022
About 3,000 attacks were launched on the infrastructure between May 11 to May 21, and this includes the attack launched on the voting system of the Eurovision Song Contest that witnessed Ukraine winning the competition on a high note. NOTE -Anonymous has also warned the Chinese government about launching any kind of war on Taiwan.

Adam Levin
JANUARY 27, 2020
According to the Motherboard article, “multiple Avast users… were not aware Avast sold browsing data, raising questions about how informed that consent is.”. The post Avast Subsidiary Sells User Browsing History appeared first on Adam Levin. It’s almost impossible to de-identify data,” said law professor Eric Goldman.

Adam Levin
OCTOBER 10, 2018
Read more about the story here. The post Facebook Patches Major WhatsApp Vulnerability appeared first on Adam Levin. The bug was initially discovered by Google Project Zero, and reported by ZDNet and the Register in late August, but was not fixed until this week, leaving the service’s 1.2 billion users vulnerable for over a month.

Adam Levin
APRIL 5, 2019
The hacking attempt was followed the next day by similar cyberattacks on Toyota’s subsidiaries in Vietnam and Thailand, each of which issued statements about the possibility of breaches without any further details or confirmation regarding the data compromised. Million Customers appeared first on Adam Levin.

Adam Levin
APRIL 17, 2020
Zoom experienced rapid growth in the wake of the Covid-19 pandemic but quickly came under fire for a litany of problems, including questionable claims about its encryption, lax default security settings, and widespread reports of “zoombombing,” where meetings are disrupted with often pornographic and hateful content. Read more here.

Adam Levin
JANUARY 30, 2020
Avast’s sudden about-face regarding the sale of user data came just days after a joint exposé published by Motherboard and PCMag that revealed the depth and scope of its user data tracking. The post Avast Announces Termination of Data Collection Subsidiary appeared first on Adam Levin.

Adam Levin
FEBRUARY 11, 2019
Read more about the story here. The post Phishing Campaign Hits Credit Unions appeared first on Adam Levin. Anti-virus scans showed that the attachments didn’t contain malware, but contained links to sites. Department of Treasury’s Financial Crimes Enforcement Network indicated that it was aware of the campaign.

CyberSecurity Insiders
JULY 29, 2022
Yes, what is being read is true as Wootton Upper School in Bedfordshire-part of Wootton Academy Trust was victimized by the file encrypting malware spreading gang and are adamant in their demand.
Daniel Miessler
DECEMBER 22, 2021
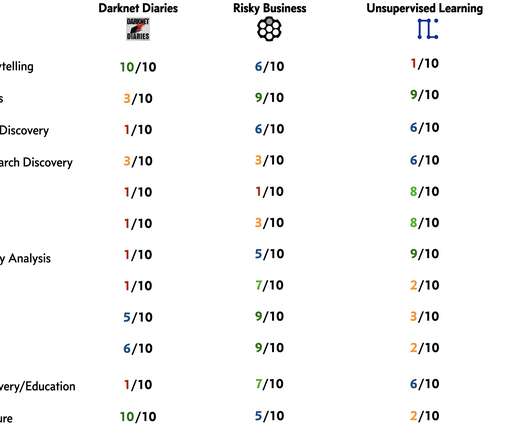
What’s so interesting about these four is how different they are. I did this analysis so I could capture what I cared about and how each of them provides those items in different amounts—which allows me to make better recommendations to people. I open more links in his newsletter than for any other. And it had two of them.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content