NSA issues advice for securing wireless devices
Malwarebytes
AUGUST 4, 2021
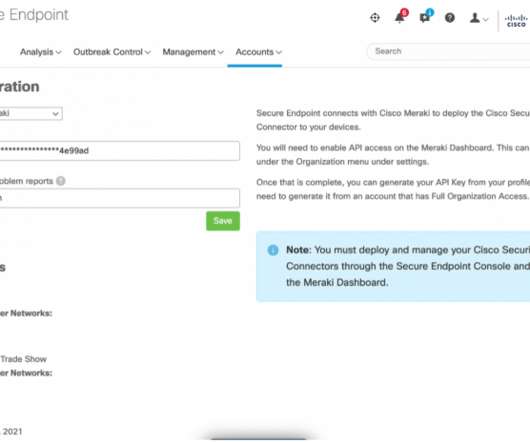
By releasing an information sheet that provides guidance on securing wireless devices while in public (pdf) —for National Security System, Department of Defense, and Defense Industrial Base teleworkers—the NSA has provided useful information on malicious techniques used by cyber actors, and ways to protect against them. Other interfaces.







































Let's personalize your content