How Zero Trust architecture improves the organization’s network security
CyberSecurity Insiders
JUNE 16, 2021
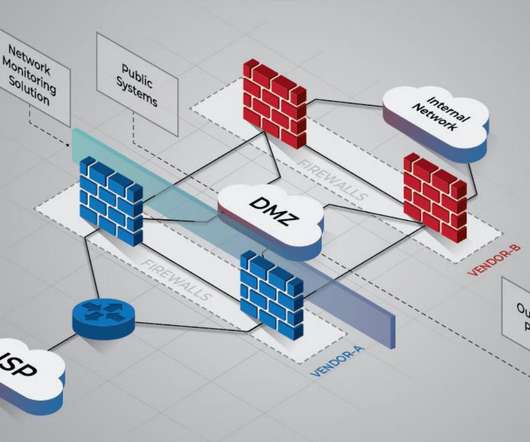
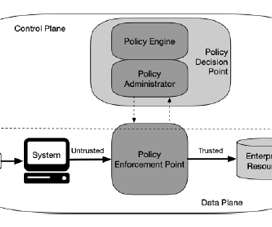
Organizations mandate users to be authentic and validated with the appropriate privacy configuration before accessing apps and information. Zero Trust presupposes there is no traditional network boundary. Networks can be regional, cloud-based, or… Posted by: Irfan Shakeel. Read full post.






































Let's personalize your content