CISO workshop slides
Notice Bored
AUGUST 5, 2022
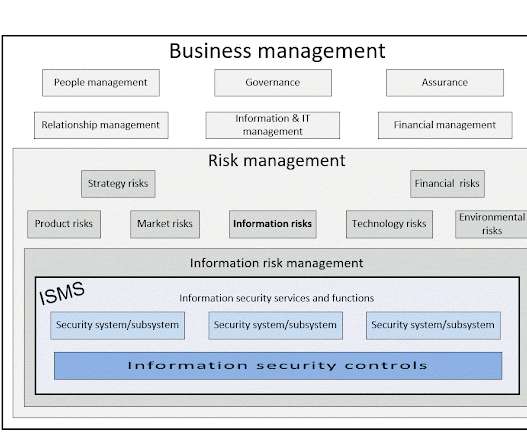
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Notice Bored
AUGUST 5, 2022
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.

Security Boulevard
JULY 18, 2023
Permalink The post BSides Sofia 2023 – Radoslav Gerganov – Hyundai Head Unit Hacking appeared first on Security Boulevard. Our thanks to BSides Sofia for publishing their presenter’s tremendous BSides Sofia 2023 content on the organizations’ YouTube channel.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
JULY 16, 2023
Permalink The post BSides Sofia 2023 – Vasil Velichkov – Hacking Attacks Against Government Institutions appeared first on Security Boulevard. Our thanks to BSides Sofia for publishing their presenter’s tremendous BSides Sofia 2023 content on the organizations’ YouTube channel.

SC Magazine
FEBRUARY 11, 2021
The new partnership with Silicon Valley CISO Investments will include an additional $250,000, but perhaps more importantly, support and guidance from the more than 55 practicing chief information security officers that make up SVCI. At the same time, applications remain the most popular external attack method for malicious hacking groups.

Security Boulevard
SEPTEMBER 9, 2023
Permalink The post BSides Buffalo 2023 – Brent Patterson – Creative Hacking With Blender appeared first on Security Boulevard. Many thanks to BSides Buffalo for publishing their presenter’s outstanding BSides Buffalo security content on the organizations’ YouTube channel.

Security Boulevard
AUGUST 8, 2023
Permalink The post BSides Leeds 2023 – Liam Follin – How To Get Away With Hacking appeared first on Security Boulevard. Thanks are in order to BSides Leeds for publishing their presenter’s outstanding BSides Leeds 2023 security content on the organizations’ YouTube channel.

SC Magazine
APRIL 30, 2021
That includes the architectures, the computing platforms, the algorithms and the people and the process as well. We’ve seen the speed and cadence of hacking groups increase substantially over the past two years. We’ve seen a series of pretty damaging software-based supply chain hacks over the past year. And that’s been overcome.

IT Security Guru
SEPTEMBER 25, 2023
The IT Security Guru caught up with Tarnveer Singh a CISO and finalist in the Security Serious Unsung Heroes Awards 2023 for his thoughts on how to get more professionals involved in the cybersecurity industry: There are many ways we can inspire new cybersecurity professionals to join our industry. We must reduce barriers to entry.
Security Boulevard
JANUARY 9, 2024
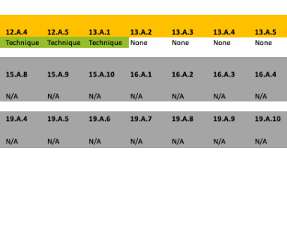
Many next-generation technologies became deployed parallel to existing solutions, including zero-trust architecture ( ZTNA ), extended detection and response ( XDR ), and cloud-based multi-factor authentication. Assessing Duplication of Security Controls. Importance of Assessing Duplication of Security Controls.

Security Boulevard
SEPTEMBER 14, 2023
Permalink The post BSides Buffalo 2023 – Magno Logan – Hacking GitHub Actions – Abusing GitHub And Azure For Fun And Profit appeared first on Security Boulevard. Many thanks to BSides Buffalo for publishing their presenter’s outstanding BSides Buffalo security content on the organizations’ YouTube channel.

SecureWorld News
APRIL 8, 2021
And the developers say this chip could end the "patch and pray" strategy that keeps security teams running in circles and lower the stress level of CISOs in the process. Undefined semantics are nooks and crannies of the computing architecture—for example the location, format, and content of program code.

SecureWorld News
JUNE 2, 2022
For more than 20 years, Glenn has advised senior executives and built teams throughout the delivery cycle: strategy, architecture, development, quality assurance, deployment, operational support, financials, and project planning. Answer: The day at my dotcom when Korea hacked one of our three web servers. Answer: Energized.

SC Magazine
MAY 12, 2021
Our CISO has a saying: Hackers don’t break in, they log in. We have a built-in defense in depth architecture, we had started with zero trust. So, between the massive hacking campaigns and the pandemic, what did Microsoft learn over the past year? That’s changing the dynamics of the networks and how we engage. .

SecureWorld News
JULY 6, 2023
The Japan Times is reporting that pro-Russian hacking group LockBit 3.0 Joseph Carson, Chief Security Scientist and Advisory CISO at Delinea, said: "Ransomware attacks have a far-reaching effect, particularly when a major part of the global supply chain is targeted.

Security Boulevard
MAY 26, 2022
Create an inventory of all components and data and map them to architecture. Pen testers, however, are typically a 3rd party external with the expertise for ethical hacking engagement. Architectural or infrastructure changes. Establish the scope. Define and describe what the model covers. Determine likely threats.

The Last Watchdog
AUGUST 19, 2021
Related: Kaseya hack worsens supply chain risk. Chris Clements, VP of Solutions Architecture, Cerberus Sentinel. Hacks and breaches are inevitable even for the most well-protected enterprise. At the start of this week, word got out that hackers claimed to have seized personal data for as many as 100 million T-Mobile patrons.
Cisco Security
APRIL 19, 2022
It’s no surprise that both hacking groups have made their presence felt. Cisco Secure Endpoint and MITRE ATT&CK: Why it matters to CISOs right now. Meeting security head-on requires adopting a comprehensive cloud-based endpoint protection solution for your secure remote worker, SASE, XDR, and Zero Trust architecture.

Security Boulevard
AUGUST 29, 2022
Except for a few “off-the-books” emergency budget requests to cover things cybersecurity insurance claims the provider did not pay, the CISO and CIO pretty much know how many “swords” they have to work with to support 24x7x365 security monitoring and operations. SOAR automation expertise supporting an adaptive security architecture.

SC Magazine
APRIL 2, 2021
Following the SolarWinds hack security pros are turning to purple teams to lock down security. In the wake of a multitude of ransomware attacks, fallout from the SolarWinds breach and the Oldsmar water supply attack, CISOs are looking for effective methods to reduce risk beyond traditional means such as penetration testing.

SecureWorld News
MAY 25, 2023
It's able to steal credentials and makes a strong effort to remain undetected, which is exactly how you would conduct a hack if you were gathering intelligence about the configuration of an IT network. Joseph Carson, Chief Security Scientist and Advisory CISO at Delinea: "The recent Volt Typhoon warning from Microsoft is alarming.

The Last Watchdog
JULY 8, 2021
Last Friday, July 2, in a matter of a few minutes, a Russian hacking collective, known as REvil, distributed leading-edge ransomware to thousands of small- and mid-sized businesses (SMBs) across the planet — and succeeded in locking out critical systems in at least 1,500 of them. Gary Phipps, VP of solution architecture, CyberGRX.

Security Boulevard
MARCH 24, 2022
Most CISOs and security practitioners do not realize that their software composition analysis tool or other cloud-based security scanners suck in all source code and process scans in the cloud before shipping results back. There is an alternative approach that safeguards your source code.

SecureWorld News
NOVEMBER 23, 2021
Apple is suing NSO Group, the company most known for its ability to hack iPhones using previously un-discovered Zero-Day vulnerabilities. And Apple's Head of Security Engineering and Architecture was extremely blunt when he announced the lawsuit on Twitter. Related with Rebecca Rakoski: Suing the CISO Podcast ].

ForAllSecure
APRIL 9, 2019
In 1998, I joined Stanford as a computer security officer, a role that is called CISO today. Updates only came after our users were hacked. In today’s piece, I’d like to share not only my vision for the future, but also an exciting announcement. Where it all began. It was me and one other person.

Security Boulevard
OCTOBER 27, 2021
Ransomware has become one of the most dangerous and high-profile problems facing CIOs and CISOs worldwide. The threat actor claimed to have hacked into T-Mobile’s production, staging, and development services two weeks prior to the event, including an Oracle database server containing customer data, sources told the Bleeping Computer.

SC Magazine
FEBRUARY 2, 2021
Mike Hamilton, president and chief information security officer at CI Security and former CISO of Seattle, told SC Media that the disparity in dates might simply be a matter of semantics. Our latest release of FTA has addressed all known vulnerabilities at this time,” said Frank Balonis, Accellion’s CISO, in a statement.

ForAllSecure
APRIL 9, 2019
In 1998, I joined Stanford as a computer security officer, a role that is called CISO today. Updates only came after our users were hacked. In today’s piece, I’d like to share not only my vision for the future, but also an exciting announcement. Where it all began. It was me and one other person.

ForAllSecure
APRIL 9, 2019
In 1998, I joined Stanford as a computer security officer, a role that is called CISO today. Updates only came after our users were hacked. In today’s piece, I’d like to share not only my vision for the future, but also an exciting announcement. Where it all began. It was me and one other person.

SecureWorld News
FEBRUARY 9, 2024
Technology: Technology is the foundation for an IAM program delivery within a layered security architecture. RELATED: Death of the VPN: A Security Eulogy ] VPNs have notably higher operating costs and lower scalability when using device-based architecture. In this case, CISOs must manage the risks due to the technology debt.

Security Affairs
JULY 24, 2018
Once an open adb port is identified, the malware drops a stage 1 shell script onto the device which, when launched, downloads two additional (stage 2) shell scripts which then download the “next stage binary for several architectures and launch the corresponding one.” He is currently Global CISO for the ATCO Group of companies.

CyberSecurity Insiders
DECEMBER 18, 2022
A look ahead to 2023 we can expect to see changes in MFA, continued Hactivism from non-state actors, CISOs lean in on more proactive security and crypto-jackers will get more savvy. 5 – Recession requires CISOs to get frank with the board about proactive security. By Marcus Fowler, CEO of Darktrace Federal.

ForAllSecure
APRIL 3, 2019
This doesn’t allow the IT administrator, the end-user, or the CISO to independently verify the security, safety, and resiliency of the software they buy and use. Of the 209 million tests, 2 million resulted in successful hacking of programs. Shouldn’t they be able to check the software? The only cost was Amazon.

Security Boulevard
AUGUST 21, 2023
Permalink The post BSidesTLV 2023 – Andy Ellis – Hacking Harry Potter: The Untold Story Of Fantastical Social Engineering appeared first on Security Boulevard. Many thanks to BSidesTLV for publishing their presenter’s erudite BSidesTLV 2023 security content on the organizations’ YouTube channel.

SecureWorld News
JUNE 3, 2024
Brad Jones, CISO at Snowflake, issued a Joint Statement regarding Preliminary Findings in Snowflake Cybersecurity Investigation on its Snowflake Forums. This isn't a supply chain hack but a reminder: if users can access your SaaS with just a password, so can attackers," said Toby Lewis, Global Head of Threat Analysis at Darktrace. "

McAfee
JUNE 21, 2021
While the vast majority of our customers made the overnight switch—many still need to adopt a cloud-native architecture. Thanks in part to the harsh publicity and severe damage caused by state-sponsored hacks that day is finally in sight. Gartner Survey Reveals Only 12% of CISOs Are Considered “Highly Effective” (Gartner).

ForAllSecure
APRIL 3, 2019
This doesn’t allow the IT administrator, the end-user, or the CISO to independently verify the security, safety, and resiliency of the software they buy and use. Of the 209 million tests, 2 million resulted in successful hacking of programs. Shouldn’t they be able to check the software? The only cost was Amazon.

ForAllSecure
APRIL 3, 2019
This doesn’t allow the IT administrator, the end-user, or the CISO to independently verify the security, safety, and resiliency of the software they buy and use. Of the 209 million tests, 2 million resulted in successful hacking of programs. Shouldn’t they be able to check the software? The only cost was Amazon.

ForAllSecure
APRIL 30, 2020
People see what happens after a system has been hacked and someone who's installed malware. There's a bunch of hacking competitions throughout the year and CMU has consistently been ranked, the top international United States team and won Defcon CTFs which is the Superbowl of hacking. Can you automatically hack programs?

ForAllSecure
APRIL 30, 2020
People see what happens after a system has been hacked and someone who's installed malware. There's a bunch of hacking competitions throughout the year and CMU has consistently been ranked, the top international United States team and won Defcon CTFs which is the Superbowl of hacking. Can you automatically hack programs?

ForAllSecure
APRIL 30, 2020
People see what happens after a system has been hacked and someone who's installed malware. There's a bunch of hacking competitions throughout the year and CMU has consistently been ranked, the top international United States team and won Defcon CTFs which is the Superbowl of hacking. Can you automatically hack programs?

McAfee
NOVEMBER 10, 2021
Under the guidance of Dan Meacham, VP of Global Security and Corporate Operations and CSO/CISO, the multi-billion dollar organization transitioned from on-premises data centers to the cloud in 2012. Its cloud-native, open architecture was exactly the right fit for Legendary Entertainment’s environment.

Security Boulevard
JANUARY 2, 2024
This hack served as a stark reminder that the supply chain remains a critical vulnerability in enterprise security. The fall of VPNs and firewalls The cyberthreats and trends of 2023 send a clear message to organizations: they must evolve their security strategies to the times and embrace a zero trust architecture.

Thales Cloud Protection & Licensing
MARCH 31, 2021
People resist ‘losing’ anything, both psychologically and technically, so we shouldn’t underestimate how quickly users learn to ‘hack’ the new system, or find ways to get around the limits of the program. Moving to a Zero Trust architecture would help with this model if setup in a single sign-on, VPN-less architecture.

ForAllSecure
DECEMBER 2, 2021
To be good at digital forensics, to be a digital Sherlock Holmes, you need to understand systems architecture. It’s about challenging our expectations about the people who hack for a living. And, you need to understand how attackers think. And in a moment I’ll introduce you to someone who’s very good at both.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content