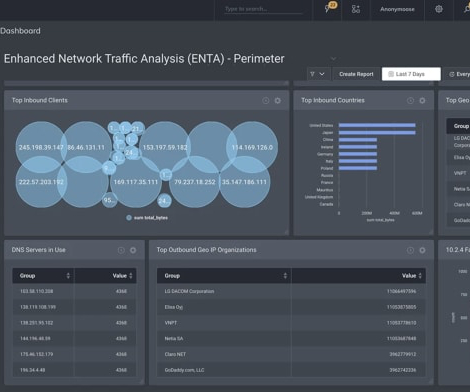
How to detect and respond to a DDoS network cyber attack
CyberSecurity Insiders
APRIL 9, 2023
A DDoS (Distributed Denial of Service) attack is a common form of cyber attack that aims to disrupt the normal functioning of a network by overwhelming it with traffic. In this type of attack, the attacker uses multiple devices to flood a network or a server with traffic, making it unavailable to legitimate users.






































Let's personalize your content