How to Prevent DDoS Attacks: 5 Steps for DDoS Prevention
eSecurity Planet
NOVEMBER 3, 2022
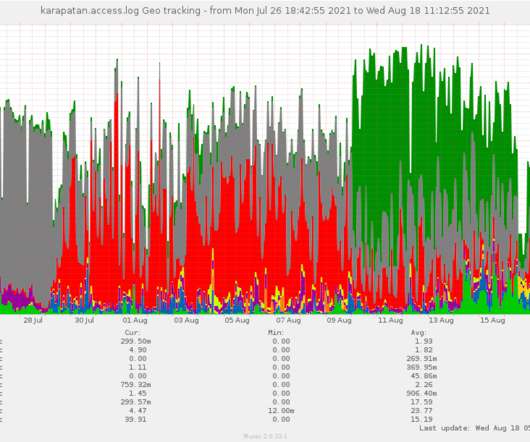
Distributed denial of service (DDoS) attacks seek to cripple a corporate resource such as applications, web sites, servers, and routers, which can quickly lead to steep losses for victims. However, DDoS attackers sometimes even target the specific computers (or routers) of unwary people – often to harass video gamers, for example.







































Let's personalize your content