A Deep Dive on the Recent Widespread DNS Hijacking Attacks
Krebs on Security
FEBRUARY 18, 2019
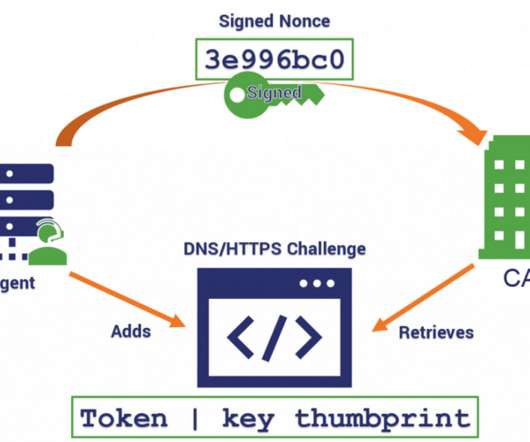
This post seeks to document the extent of those attacks, and traces the origins of this overwhelmingly successful cyber espionage campaign back to a cascading series of breaches at key Internet infrastructure providers. PASSIVE DNS.











































Let's personalize your content