Retailer Orvis.com Leaked Hundreds of Internal Passwords on Pastebin
Krebs on Security
NOVEMBER 11, 2019
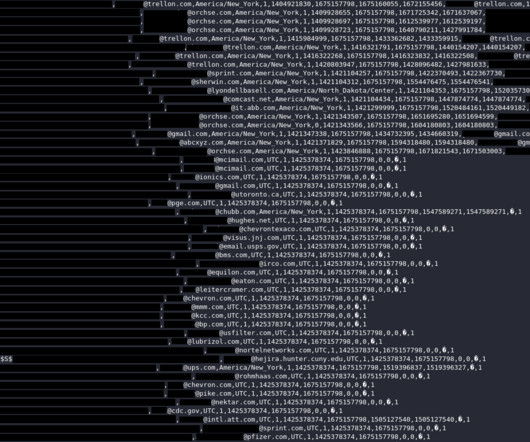
In late October, this author received a tip from Wisconsin-based security firm Hold Security that a file containing a staggering number of internal usernames and passwords for Orvis had been posted to Pastebin. Data backup services. Microsoft Active Directory accounts and passwords. Battery backup systems. Linux servers.











































Let's personalize your content