Trying to Find a Balance: Introducing Risk-Based Authentication
Duo's Security Blog
SEPTEMBER 22, 2022
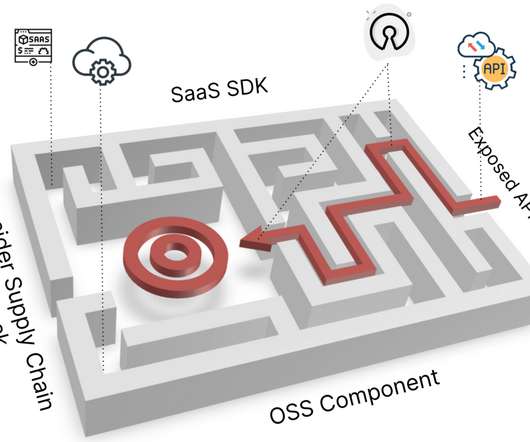
These challenges make it hard to follow the most secure practices: employing the most secure authentication methods, requiring constant re-authentication and only allowing access from corporate devices. Risk-Based Authentication assesses user and device telemetry to identify known threat patterns and high-risk anomalies.















































Let's personalize your content