Silent Safeguards – The Essence of ISO 27001 Controls
Heimadal Security
NOVEMBER 3, 2023
ISO 27001, sometimes referred to as ISO/IEC 27001 is an international standard that addresses organizational information security.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 iso-27001-controls
iso-27001-controls  Blog Related Topics
Blog Related Topics 
Heimadal Security
NOVEMBER 3, 2023
ISO 27001, sometimes referred to as ISO/IEC 27001 is an international standard that addresses organizational information security.

Heimadal Security
NOVEMBER 17, 2023
When it comes to information security, ISO 27001 is of paramount importance. However, the journey from understanding to effectively implementing ISO 27001 controls is not without challenges. As CISOs and IT administrators, you’re likely familiar with its significance.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
APRIL 11, 2024
ISO 27001 is a globally recognized standard for information security management systems (ISMS). It offers organizations a framework for implementing a systematic approach to controlling information security threats. ISO 27001 compliance can benefit every business that handles confidential data.

Centraleyes
FEBRUARY 29, 2024
Understanding ISO Standards ISO standards are internationally recognized guidelines that ensure organizations meet specific quality, safety, and efficiency criteria in their products, services, or processes. ISO covers many areas, from quality management (e.g., ISO 9001) to information security (e.g., ISO 27001).

Duo's Security Blog
FEBRUARY 1, 2021
We are proud to announce the Duo has achieved ISO 27001:2013, 27017:2015, and 27018:2019 certification! You can thank ISO for that! What is ISO 27001:2013, 27017:2015 and 27018:2019? What’s the benefit of ISO 27001:2013, 27017:2015 and 27018:2019 certification to our customers?

Security Boulevard
APRIL 29, 2022
One of the key compliance requirements of ISO 27001 is to create an asset inventory. ISO 27001 outlines how organisations can develop an asset inventory in control A.8.1.1 ISO 27001 outlines how organisations can develop an asset inventory in control A.8.1.1 of Annex A. of Annex A.

The Last Watchdog
MAY 19, 2022
Wikipedia uses a CMS for textual entries, blog posts, images, photographs, videos, charts, graphics, and “ talk pages ” that help its many contributors collaborate. To do the job right, however, make sure that your employees follow good procedures, and that your platform provider is certified as following the ISO 27001 process.

Duo's Security Blog
FEBRUARY 1, 2021
We are proud to announce the Duo has achieved ISO 27001:2013, 27017:2015, and 27018:2019 certification! You can thank ISO for that! What is ISO 27001:2013, 27017:27017 and 27018:2019? What’s the benefit of ISO 27001:2013, 27017:27017 and 27018:2019 certification to our customers?

Notice Bored
JUNE 5, 2022
The organisation cannot adopt a generic suite of information security controls simply on the basis that they have been recommended or suggested by someone - not even if they are noted in Annex A. c) compare the controls determined in 6.1.3 c) compare the controls determined in 6.1.3 Subclause 6.1.3

Centraleyes
MARCH 12, 2024
At its core, an audit systematically examines an organization’s processes, controls, and practices. Operational Efficiency By evaluating security controls and practices, audits enhance the efficiency of cybersecurity operations, minimizing the impact of potential breaches. What is a Security Audit? Why are Audits Important?

Duo's Security Blog
FEBRUARY 1, 2021
We are proud to announce the Duo has achieved ISO 27001:2013, 27017:2015, and 27018:2019 certification! You can thank ISO for that! What is ISO 27001:2013, 27017:2015 and 27018:2019? What’s the benefit of ISO 27001:2013, 27017:2015 and 27018:2019 certification to our customers?
Centraleyes
MARCH 11, 2024
Enter cloud compliance frameworks—the mission control centers of the digital age—providing the necessary guidelines and protocols to avert crises and navigate the complexities of data security. Data Security: CSA CM provides guidelines and controls to ensure data security in the cloud. What are Cloud Architecture Frameworks?

Centraleyes
APRIL 25, 2024
Assessing Security Controls: Audits evaluate the effectiveness of security controls like firewalls, encryption, and access controls to safeguard against various threats. Unbiased Evaluation External auditors provide an unbiased evaluation of security controls, compliance with regulations, and overall security posture.

Centraleyes
APRIL 18, 2024
These evaluations aim to identify vulnerabilities, assess controls, and ensure compliance with industry standards and regulations. External Audits Mandated by international or federal standards like ISO 27001 or SOC 2, external audits involve independent third parties evaluating the implementation of standard requirements.

Thales Cloud Protection & Licensing
MAY 16, 2022
In a previous blog post, I discussed how The White House Executive Order issued on May 12, 2021 laid out new, rigorous government cyber security standards for federal agencies. Control – Insulate and layer access against digital threats like ransomware attacks. I’ll explore this point in my next blog post. Data security.

The Last Watchdog
JANUARY 17, 2022
One solution for secure software development is tracking security requirements and controls. CISOs are usually given authority to implementing perimeter controls and testing for defects, but don’t have the authority, mandate or incentive to change software development.

CyberSecurity Insiders
NOVEMBER 1, 2021
Likewise, if a business doesn’t integrate security into operations from the beginning there is only so much that can be done to implement necessary controls. Frameworks provide varying amounts and levels of controls depending on which you select. For larger, or more mature organizations ISO may be the perfect fit.

Centraleyes
NOVEMBER 23, 2023
It serves as a cornerstone in auditing, primarily concerned with evaluating the effectiveness of controls related to regulatory risks. In the context of IT compliance testing, compliance testing may begin by examining user access provisioning and de-provisioning controls. This step is crucial in determining which controls to test.

BH Consulting
JANUARY 11, 2022
In that spirit, we’ve rounded up five of our most popular blogs from the past year. The blog was inspired by the growing number of organisations coming under pressure to take out insurance cover. BH Consulting’s Head of Sales and Marketing John Mangan weighed the pros and cons in a thoughtful blog. Risk vs reward.

Centraleyes
DECEMBER 6, 2023
A cyber risk assessment will identify and prioritize your assets, show how well your controls are working, identify gaps and offer insights into cybersecurity risk mitigation. STRATEGY # 2 – IMPLEMENT SECURITY CONTROLS Once you have identified your specific vulnerabilities, it’s time to put mitigating security controls in place.
Notice Bored
AUGUST 23, 2020
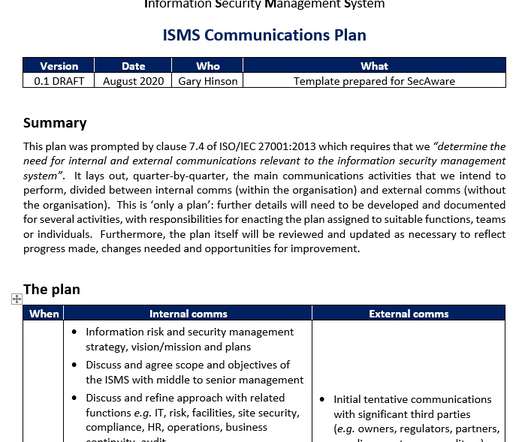
Yesterday I started preparing an ISMS communications plan to satisfy ISO/IEC 27001 :2013 clause 7.4, In other words, a documented comms plan is discretionary - advised as good practice but not strictly demanded of every organisation for '27001 compliance certification. They point out the link to discretionary control A.7.2.2

Centraleyes
DECEMBER 10, 2023
Originally established by the American Institute of CPAs, the original report (SAS 70) was used by a CPA to determine if an internal control was effective for financial reporting. ” This guide pertains to System and Organization Control (SOC) examinations, commonly known as SOC audits.

BH Consulting
MARCH 3, 2022
As we’ll explore in this blog, it’s essential that cybersecurity isn’t just a coat of paint on top but is part of the design and embedded into the foundations. Health and safety regulations are another concern, and technology is often deployed to help with fire and safety systems, security and access control, and alarm management.

Security Boulevard
JUNE 8, 2021
In the third installment of our series, Protecting Industrial Control Systems Against Cyberattacks , we explore additional risk factors and vulnerabilities facing ICS SCADA systems. Operators use the SCADA system to control large-scale processes that manage up to thousands of field connections and sensors. Additional Learning.

Notice Bored
JULY 23, 2020
As I'm drafting the procedure, I'm itching to mention related aspects such as governance, accountability, access control, competence, oversight, monitoring, resilience and more. Meanwhile, this blog is my relief valve: there, I've brought up some other matters and acknowledged their relevance without turning the procedure into War and Peace.

Notice Bored
MAY 25, 2022
Various forms of 'control' are important to stabilise situations and gain assurance that whatever actually happens is the anticipated result of whatever changes we have made, rather than some factor that we probably hadn't even appreciated - which itself can be valuable knowledge. Likewise, security improvements depend on one's perspective.

Duo's Security Blog
JUNE 9, 2022
As well as assisting underwriters to create policies, signals can also provide a goldmine of information for a CISO, alerting them to information they don’t know about their firm; things that could be heeded in order to implement the right controls to bring security maturity levels up and make an organization more resilient.

The Last Watchdog
OCTOBER 13, 2021
Check out the examples below from Forrester’s blog. Here are the big five that make first-party data superior to the others we’ve discussed: •Control: Dictate what data you want to collect and how to collect it. First-party” data is different from zero-party data. Just using zero- and first-party data only. First-party superiority.

Centraleyes
FEBRUARY 5, 2024
This is particularly critical for organizations handling digital assets, as compliance involves adopting risk-based controls to safeguard information confidentiality, integrity, and availability. Different categories of personal information may be subject to additional controls under various regulations.
Notice Bored
APRIL 22, 2021
There are clearly several aspects to this, some that are very tough to ‘manage’ or ‘control’ and many that are interrelated. Critical" controls typically deserve more focus and attention than relatively minor ones, for instance. Paradoxically, it is quite complicated and difficult to keep things simple!

Centraleyes
NOVEMBER 1, 2023
This blog post will delve into the fundamental principles underpinning effective information security principles and practices. Maintaining confidentiality involves implementing access controls, encryption, and user authentication mechanisms to restrict access to data based on user roles and permissions.

Centraleyes
NOVEMBER 16, 2023
SOC 2, short for System and Organization Controls 2, is an independent audit and certification that evaluates an organization’s information systems security, availability, processing integrity, confidentiality, and privacy controls. Assessment : Auditors will dive deep into your controls, policies, and procedures.

The Last Watchdog
FEBRUARY 26, 2023
Of the numerous security frameworks available to help companies protect against cyber-threats, many consider ISO 27001 to be the gold standard. The most recent updates came in October 2022, when ISO 27001 was amended with enhanced focus on the software development lifecycle (SDLC).
Notice Bored
OCTOBER 14, 2021
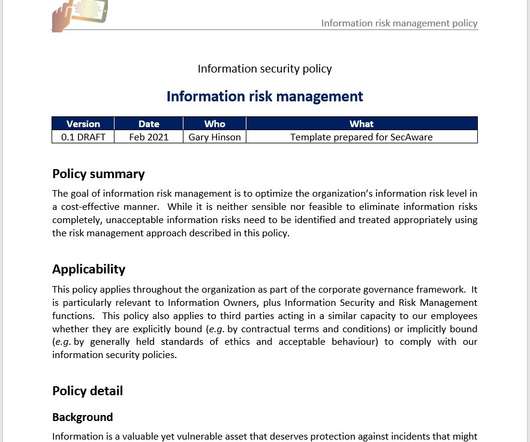
Transmission of information through broadcasting, training and awareness activities, reporting, policies, documentation, seminars, publications, blogs etc., plus its reception and comprehension. There is a common factor, however, namely information risk. Detailed policy requirements 1.

Centraleyes
FEBRUARY 13, 2024
This blog aims to serve as a guide to navigating the intricate terrain of cyber risk quantification, providing insights into its significance, methodologies, and the transformative impact it can have on organizational cybersecurity strategies. Evaluate these controls against industry best practices and regulatory requirements.

BH Consulting
AUGUST 10, 2023
Some privacy professionals consider controls frameworks to be ‘their secret sauce’, but I think of them as ‘our secret sauce’ as an industry. I am presenting two frameworks here (albeit one is technically a standard) from NIST and ISO. There are several others, such as CIS controls, HITRUST Common Security Framework, and COBIT.

Centraleyes
MARCH 18, 2024
is compatible with the NIST Privacy Framework, NIST AI Risk Management Framework , NIST SP 800-53 , ISO 27001 , and CIS Controls , among other industry standards. This function covers the following outcomes: platform security (i.e., The NIST CSF 2.0

Notice Bored
FEBRUARY 24, 2022
Last week's release of a completely restructured ISO/IEC 27002:2022 has naturally prompted a rash of questions from anxious ISO27k users around the world about the implications for ISO/IEC 27001:2013, particularly on the certification aspects since '27002:2022 no longer aligns with '27001:2013 Annex A.
Notice Bored
NOVEMBER 26, 2021
I mentioned recently here on the blog that there can be strategic elements to policies, just as there are operational aspects to the supporting procedures and guidelines. What controls are appropriate to contain the risks in this domain? With the new year fast approaching, I'd like to explore that further today. Prepare for the glare.

Pen Test Partners
SEPTEMBER 26, 2023
There are plenty of ways to meet your security requirements ISO 27001 is not everything. There, I said it What is the Secure Controls Framework (SCF)? They usually default to one framework, ISO 27001. But ISO 27001 is not your only option. But ISO 27001 is not your only option.

Security Boulevard
DECEMBER 8, 2022
Trustero Compliance as a Service (CaaS) now supports SOC 2 and ISO 27001. The post ISO 27001 Compliance: Trustero has you covered! The post ISO 27001 Compliance: Trustero has you covered! Manage both from the same powerful platform. Learn more. appeared first on Trustero.

Notice Bored
JUNE 23, 2022
Having recently blogged about the dreaded SoA , 'nuff said on that. ISO/IEC 27001 barely even acknowledges the RTP. ISO/IEC 27003 offers a page of 'guidance on formulating an information security risk treatment plan (6.1.3 Necessary control(s); Where both 'controls' and 'necessary' are decidedly ambiguous.

Security Boulevard
JANUARY 26, 2023
Raw data is not "audit-ready" evidence. Read more to learn why, and how Trustero Compliance as a Service delivers true, actionable evidence. The post Complete Compliance: Actionable Evidence Versus Simple Integrations appeared first on Trustero.

Approachable Cyber Threats
DECEMBER 21, 2023
This blog post will explore the evolving threat landscape of supply chain attacks, highlighting recent statistics and offering practical recommendations for organizations looking to strengthen their cybersecurity posture. Consider factors such as their track record, security certifications (SOC2, ISO 27001, PCI-DSS, etc.),
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content