The 2019 State of Cloud Security
Dark Reading
MAY 3, 2019
Enterprise cloud security is making real progress, but emerging technologies call for security teams to keep up the pace.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cloud-security the-2019-state-of-cloud-security
cloud-security the-2019-state-of-cloud-security 
Dark Reading
MAY 3, 2019
Enterprise cloud security is making real progress, but emerging technologies call for security teams to keep up the pace.

Schneier on Security
JANUARY 5, 2021
But as businesses like Amazon and Microsoft that provide cloud services dig deeper for evidence, it now appears Russia exploited multiple layers of the supply chain to gain access to as many as 250 networks. There is also no indication yet that any human intelligence alerted the United States to the hacking.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
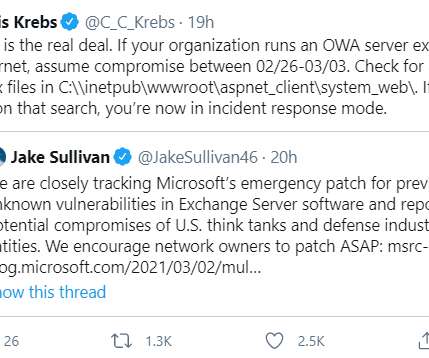
Krebs on Security
MARCH 5, 2021
On March 2, Microsoft released emergency security updates to plug four security holes in Exchange Server versions 2013 through 2019 that hackers were actively using to siphon email communications from Internet-facing systems running Exchange. Microsoft’s initial advisory about the Exchange flaws credited Reston, Va.

The Last Watchdog
NOVEMBER 8, 2021
There’s no doubt, the increasing use of telemedicine, the explosion of health-based cloud apps, and innovative medical IoT devices are improving the patient care experience. However, healthcare data ranks at the top of the list for needing improvements in security and privacy protections. Patient data exposures.

CyberSecurity Insiders
APRIL 13, 2021
Broadcom Inc has announced that it will move its security offerings acquired through Symantec onto Google Cloud Platform (GCP). Tom Krause, the President of Broadcom Software Group confirmed the news and stated that the rest of the security offerings that were hosted in the data center will be moved to GCP by this year end.
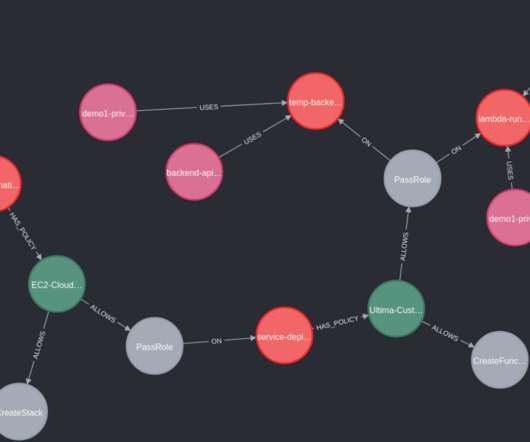
Security Affairs
SEPTEMBER 28, 2022
nuvola is the new open-source cloud security tool to address the privilege escalation in cloud environments. nuvola is the new open source security tool made by the Italian cyber security researcher Edoardo Rosa ( @_notdodo_ ), Security Engineer at Prima Assicurazioni. Cloud Security Context.
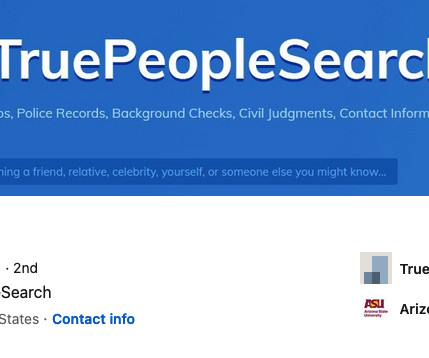
Krebs on Security
MARCH 20, 2024
It’s not unusual for the data brokers behind people-search websites to use pseudonyms in their day-to-day lives (you would, too). Some of these personal data purveyors even try to reinvent their online identities in a bid to hide their conflicts of interest. net , KrebsOnSecurity began poking around. What are the odds?

CyberSecurity Insiders
SEPTEMBER 13, 2021
Tenable has made an official announcement that it has acquired cloud security startup Accurics for $160 million. Therefore, Accurics programmatic detection and mitigation of risky tools will help customers to securely access and secure infrastructure related to security and development and operations teams.

Google Security
JUNE 22, 2023
Anthony Weems, Information Security Engineer 2022 was a successful year for Google's Vulnerability Reward Programs (VRPs), with over 2,900 security issues identified and fixed, and over $12 million in bounty rewards awarded to researchers.

SiteLock
AUGUST 27, 2021
We are excited to announce that SiteLock ® INFINITY™ has been recognized as a WINNER of the 2019 Cloud Computing Security Excellence Awards ! forced to go under following a cyberattack, the need for simple, affordable and powerful website security has never been more important. With 60% of small businesses.

CyberSecurity Insiders
FEBRUARY 28, 2021
In November 2020, Security firm FireEye revealed that a Russian intelligence funded hacking group had infiltrated the computer networks of several organizations and was indulging in several espionage related tactics since 2019. The post It is Microsoft vs Dell and IBM after SolarWinds hack appeared first on Cybersecurity Insiders.

Schneier on Security
FEBRUARY 3, 2021
Microsoft analyzed details of the SolarWinds attack: Microsoft and FireEye only detected the Sunburst or Solorigate malware in December, but Crowdstrike reported this month that another related piece of malware, Sunspot , was deployed in September 2019, at the time hackers breached SolarWinds’ internal network.

Krebs on Security
JUNE 27, 2019
based cloud solution provider, allowed hackers to access email and file sharing systems for some of the company’s clients, KrebsOnSecurity has learned. based PCM [ NASDAQ:PCMI ] is a provider of technology products, services and solutions to businesses as well as state and federal governments. A digital intrusion at PCM Inc. ,

SC Magazine
APRIL 14, 2021
Co-founder and CEO at Cloudflare Matthew Prince shares the stage with venture capital leaders at TechCrunch Disrupt Berlin 2019. Cloud is among the factors influencing massive investments in the cybersecurity space during 2020. While 2017, 2018 and 2019 all saw at least 700 deals, there were just 665 in 2020. billion last year.
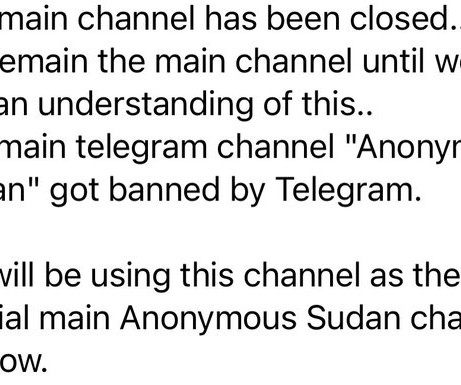
Security Affairs
SEPTEMBER 12, 2023
Its these type of spiteful, vengeful attacks that put doubt on the state controlled narrative of the group. Its these type of spiteful, vengeful attacks that put doubt on the state controlled narrative of the group. However, some security researchers believe that Anonymous Sudan is a sub-group of the Pro-Russian threat group Killnet.

Security Boulevard
JUNE 1, 2021
The events of 2020 didn’t prevent small- to mid-sized businesses (SMBs) from adopting the cloud. Impact Networking reported that SMBs’ overall cloud spending grew 6.3% between 2019 and 2020. million on public cloud services by […]… Read More. million on public cloud services by […]… Read More.
Krebs on Security
JANUARY 6, 2022
Norton’s parent firm says the cloud-based service that activates the program and allows customers to profit from the scheme — in which the company keeps 15 percent of any currencies mined — is “opt-in,” meaning users have to agree to enable it. ” Norton 360 is owned by Tempe, Ariz.-based

SC Magazine
JUNE 4, 2021
Today’s columnist, Raj Badhwar of Voya Financial, says to prevent cloud-based breaches like the one that happened to Capital One in 2019, security teams need to develop an enterprise cloud operating model based on a cloud-first approach. For Phase 1, establish a core cloud infrastructure security foundation.

SC Magazine
MARCH 29, 2021
Advancements in cyber technology and increasingly sophisticated tactics of bad actors require all security professionals to be in a constant state of learning. Similarly, companies need to have the assurance that their security team maintains the skills needed to protect systems and data. labor market.

Security Affairs
AUGUST 9, 2020
US Office of the Comptroller of the Currency (OCC) regulator has fined the credit card provider Capital One Financial Corp with $80 million over 2019 data breach. The US Office of the Comptroller of the Currency (OCC) has imposed an $80 million fine to the credit card provider Capital One Financial Corp over 2019 data breach.

CyberSecurity Insiders
DECEMBER 21, 2022
Aston University data scientists argue that cloud platforms will become full in the next 2-3 years, leaving the humans find for ways to support the storage tech in coming years. Scientists at Aston University are predicting a data deluge by the year 2025 that will pave the way to storage crisis later.

Duo's Security Blog
JUNE 14, 2021
It is important for companies to ensure their information is secure regardless of where their employees are working. Prisma Clouds’ 2021 Cloud Threat Report and Verizon’s 2021 DBIR Report show how companies have needed to adapt and expand cloud workloads and how this has affected their cybersecurity.

BH Consulting
DECEMBER 11, 2023
Cloudy outlook for security? Cloud technology use is growing , but are organisations’ taking precautions to secure these services? Datadog’s latest annual report uncovered common weak security practices from analysing thousands of organisations using platforms like AWS, Microsoft Azure and Google Cloud.

CyberSecurity Insiders
AUGUST 15, 2021
T-Mobile that occupies over 35% of mobile subscriber base in United States has launched a detailed probe after receiving several media concerns that over 100 million T mobile customer data was available on sale on the dark web. Interestingly, the hackers’ forum doesn’t hold recognition that the data is related to T-Mobile customers.

Thales Cloud Protection & Licensing
SEPTEMBER 17, 2019
As government agencies get back to work after summer barbeques, family vacations and once-in-a-lifetime getaways, the focus is on the priorities for the rest of 2019. The focus on the rest of 2019 and looking ahead to 2020 was very clear when I attended two recent industry events. The Continued Impact of IoT. In fact, the U.S.

The Last Watchdog
MARCH 12, 2020
market in 2019. It comes as no surprise that top cyber crime rings immediately pounced on the Coronavirus outbreak to spread a potent strain of malware via malicious email and web links. I had the chance to visit with Votiro CEO and founder Aviv Grafi at RSA 2020. For a full drill down give a listen to the accompanying podcast.

eSecurity Planet
OCTOBER 8, 2021
And like other old-guard companies, ESET knows it needs to innovate to stay competitive, which the company has done with its cloud-based endpoint protection platform, ESET PROTECT. Administrators can quickly deploy ESET and configure policies to meet network security objectives through the cloud-based management console.

Thales Cloud Protection & Licensing
MAY 14, 2019
Digital transformation is driving IT modernization, IoT, and cloud migrations at a record pace in the federal government. The ability to narrow the gap between taking advantage of digital transformation without compromising security was a reoccurring theme at our 2019 annual Data Security Summit on May 1. are discovered.

Thales Cloud Protection & Licensing
MAY 1, 2019
Over the last two election cycles, we’ve seen an increased focus on election security, hacking and fraud. While many state and government officials are under no illusion that they are safe from a digital attack, concern should run deeper than election integrity. Security measures continue to be more reactive than proactive.

McAfee
NOVEMBER 3, 2020
The RSA Conference USA 2019 held in San Francisco — which is the world’s largest cybersecurity event with more than 40,000 people and 740 speakers — is a decent measuring stick for representation of women in this field. Women in Cloud and Security – A Panel with McAfee, AWS, and Our Customers. Live Panel. Register Now.

Security Affairs
APRIL 5, 2019
Security experts at Rapid7 have discovered that over 2 million Apache HTTP servers are still affected by the CVE-2019-0211 critical privilege escalation flaw. According to an analysis conducted by Rapid7, more than 2,000,000 servers, many on public cloud platforms, are still running vulnerable versions of Apache.

The Last Watchdog
FEBRUARY 24, 2020
Related: The role of PKI is securing digital transformation That was in 2002. I recently had a chance to have a rich discussion about the state of cybersecurity with Stiennon, the occasion being him sending me a copy of his new book: Security Yearbook 2020: A History and Directory of the IT Security Industry.

Krebs on Security
FEBRUARY 23, 2019
based Apex HCM is a cloud-based payroll software company that serves some 350 payroll service bureaus that in turn provide payroll services to small and mid-sized businesses. The company quickly took all of its systems offline, and began notifying customers that it was trying to remediate a security threat. Roswell, Ga.

SC Magazine
FEBRUARY 11, 2021
Researchers from RiskSense have identified as many as 223 distinct IT security vulnerabilities in the Common Vulnerabilities and Exposures (CVE) database that were tied to attacks involving ransomware in 2020. The vast majority of flaws (96%) used in ransomware attacks are years old, having been publicly identified prior to 2019.

CyberSecurity Insiders
MARCH 4, 2022
Now, Microsoft issued a public statement on March 4th,2022 stating that it will suspend all the new sales of its services and products in Russia on an immediate note. News is out that the American tech company will also suspend security updates for all the PCs operating on Russian soil from next week.
Security Affairs
JANUARY 6, 2023
Cloud services provider Rackspace confirmed that the recent data breach was the result of the Play Ransomware gang’s attack. Cloud services provider Rackspace announced this week that the recent data breach was the result of an attack conducted by the Play ransomware group. ” reads an update provided by the company.

CyberSecurity Insiders
JUNE 21, 2021
The content in the webpage states to fill in some details to have future access to the cloud-based account that has been blocked due to some security reasons. In the year 2019, Trend Micro detected over 61.2 Google is urging users to beware of the phishing attacks that are taking place on Google Drive.

The Last Watchdog
JANUARY 6, 2022
Related: Why the ‘Golden Age’ of cyber espionage is upon us. The global threat intelligence market size was estimated at $10.9 billion in 2020 and will grow to $16.1 billion by 2025. Yet, according to the study by the Ponemon Institute, the number of insider leaks has increased by 47 percent in 2020 compared to 2018. Demyanchuk.
Malwarebytes
MARCH 13, 2024
The Common Vulnerabilities and Exposures (CVE) database lists publicly disclosed computer security flaws. The attention for Hyper-V is remarkable since only a week earlier, VMware released security updates to fix critical sandbox escape vulnerabilities in VMware ESXi, Workstation, Fusion, and Cloud Foundation.

Thales Cloud Protection & Licensing
FEBRUARY 24, 2020
In previous years, we have discussed the efforts of businesses to digitally transform their processes to maintain or gain a competitive advantage and many of these transformative technologies involves moving to the cloud. Whatever the nature of the data stored in the cloud, it needs to be secured.

SC Magazine
JULY 1, 2021
warns that Fancy Bear, a hacking group tied to Russia’s Main Intelligence Directorate (GRU), has been conducting a stealthy two-year espionage campaign that targets global enterprise and cloud environments with brute-force attacks. and foreign organizations across the world, with a particular focus on the United States and Europe.

Thales Cloud Protection & Licensing
APRIL 14, 2020
As a result, companies around the globe are doing everything they can to maintain a “business as usual” pace so there is minimal disruption, even if it means relaxing security processes and quickly adopting new tools that may create new risks. A 2019 survey of full time workers in the U.S.
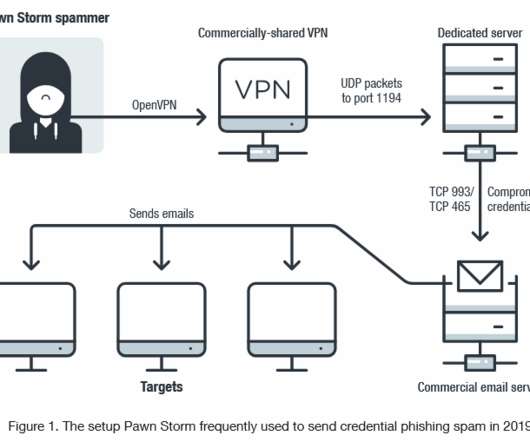
Security Affairs
MARCH 20, 2020
According to security researchers from Trend Micro, the Russia-linked APT28 cyberespionage group has been scanning vulnerable email servers for more than a year. The nation-state hackers are scanning the entire internet, in search of vulnerable webmail and Microsoft Exchange Autodiscover servers that expose TCP ports 445 and 1433.

SecureWorld News
NOVEMBER 12, 2020
Sometimes when you are down in the cyber attack trees defending your organization, it can be tough to see the cyber threat forest. Understanding how things are shifting in the forest, or overall threat landscape, can help us categorize, strategize, and prioritize our resources. What are the top cyber threats right now? Web-based Attacks. Ransomware.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content