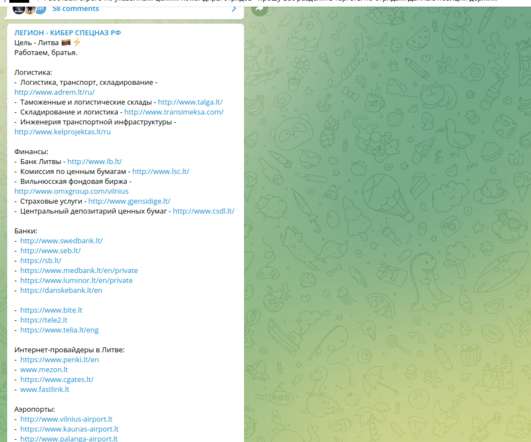
Exclusive: Lithuania under cyber-attack after the ban on Russian railway goods
Security Affairs
JUNE 22, 2022
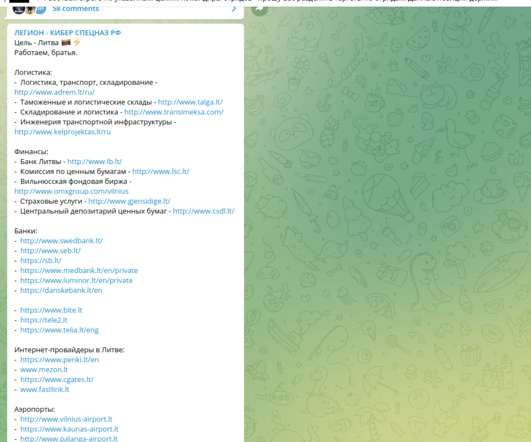
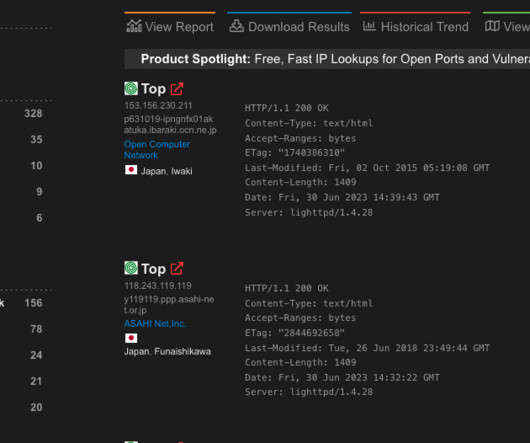
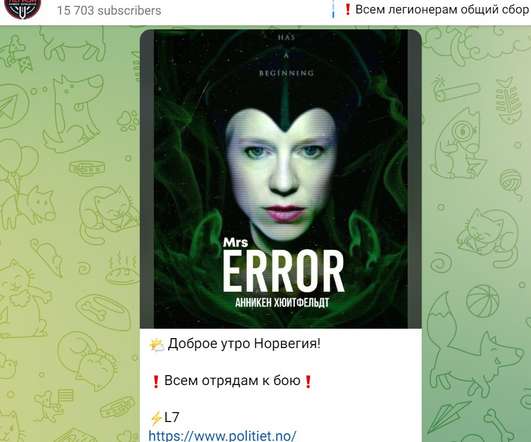
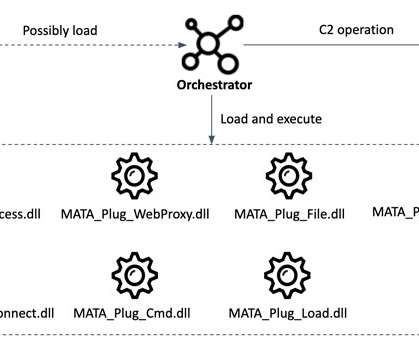
The group is leveraging relatively cost-effective means and methods of DDoS, by doing so they generate significant DDoS power by attacking compromised WEB-resources, WEB-sites, IoT devices and botnet networks belonging to other independent actors who agreed to join the campaign. SecurityAffairs – hacking, Lithuania).






































Let's personalize your content