Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

eSecurity Planet
FEBRUARY 14, 2024
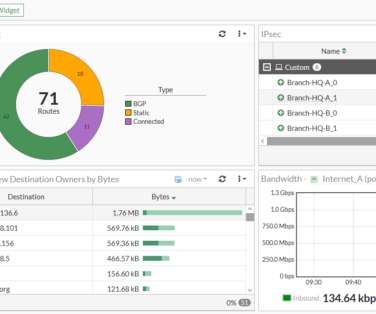
Stateful inspection is a firewall feature that filters data packets based on the context of previous data packets. This important feature uses header information from established communication connections to improve overall security. Table of Contents Toggle How Does Stateful Inspection Work? Stateless protocols (UDP, HTTP, etc.)
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
NOVEMBER 10, 2023
DNS security protects the domain name system (DNS) from attackers seeking to reroute traffic to malicious sites. Since a majority of business IT traffic now accesses or passes through the internet, DNS plays an increasingly important — and vulnerable — role.

eSecurity Planet
JANUARY 5, 2024
A firewall policy is a set of rules and standards designed to control network traffic between an organization’s internal network and the internet. It aims to prevent unauthorized access, manage data movement, and guard against potential security threats.

SC Magazine
MARCH 4, 2021
The National Security Agency (NSA) and Cybersecurity and Infrastructure Agency (CISA) released a joint information sheet Thursday that offers guidance on the benefits of using a Protective Domain Name System (PDNS). A PDNS service uses existing DNS protocols and architecture to analyze DNS queries and mitigate threats.

CyberSecurity Insiders
MAY 18, 2022
A foundational approach to cybersecurity empowers CISOs to see abnormalities and block threats before they do damage. Constantly playing catch-up seems to have become the unfortunate norm in the cybersecurity industry. So why aren’t more organizations taking advantage of protective DNS? So where do we go from here?

eSecurity Planet
JUNE 21, 2022
” Also read: Cybersecurity Employment in 2022: Solving the Skills Gap. How to Choose a Security Certification. Thycotic chief security scientist Joseph Carson told eSecurity Planet that choosing a certification should ultimately be about deciding which skillset or professional direction you want to focus on.

SC Magazine
MARCH 31, 2021
Centripetal Networks filed a lawsuit this month accusing Palo Alto of violating 12 separate patents for systems or policies designed to enhance network security. Worth noting that Centripetal has pursued – and won – patent cases against other industry titans in the past for incorporating its security innovations.

Webroot
MARCH 9, 2021
DNS (Domain Name System) is especially vulnerable. One of the most common methods of infiltration includes internet-based attacks, such as Denial of Service (DoS), Distributed Denial of Service (DDoS) and DNS poisoning. However, cybercriminals can also use legal DNS traffic surveillance to their advantage.
Webroot
MARCH 29, 2021
A firewall with the right threat intelligence embedded could have blocked communications with the command-and-control server thus preventing a Trojanized Orion install from connecting back to the attackers and stopping them from furthering the attack. Outside of the corporate firewall, it is the Wild West.

eSecurity Planet
APRIL 26, 2024
Network security architecture is a strategy that provides formal processes to design robust and secure networks. Effective implementation improves data throughput, system reliability, and overall security for any organization.

eSecurity Planet
DECEMBER 8, 2023
Domain name service (DNS) attacks threaten every internet connection because they can deny, intercept, and hijack connections. With the internet playing an increasing role in business, securing DNS plays a critical role in both operations and security. Everything You Need to Know.

CyberSecurity Insiders
MARCH 21, 2021
When it comes to protecting your small business from cyber attacks, the first and foremost thing is to upgrade your network security and IT infrastructure to the latest standards. Modern technology comes with improved network security offering higher protection. . Build a cyber security plan . Firewalls .

eSecurity Planet
MARCH 14, 2023
Network security creates shielded, monitored, and secure communications between users and assets. Securing the expanding, sprawling, and sometimes conflicting collection of technologies that make up network security provides constant challenges for security professionals.

eSecurity Planet
JULY 25, 2022
The domain name system (DNS) is basically a directory of addresses for the internet. Your browser uses DNS to find the IP for a specific service. For example, when you enter esecurityplanet.com, the browser queries a DNS service to reach the matching servers, but it’s also used when you send an email. DNS spoofing or poisoning.

SC Magazine
MAY 5, 2021
Signage with logo at the Silicon Valley headquarters of computer security and firewall company Palo Alto Networks, Santa Clara, California, August 17, 2017. Palo Alto Networks asked a Virginia judge to dismiss a patent lawsuit filed against them by Centripetal Networks.

eSecurity Planet
SEPTEMBER 24, 2021
Rapid7 combines threat intelligence , security research, data collection, and analytics in its comprehensive Insight platform, but how does its detection and response solution – InsightIDR – compare to other cybersecurity solutions? Alert Logic AT&T Cybersecurity BeyondTrust Crowdstrike F-Secure Invicti LogRhythm.

eSecurity Planet
JULY 7, 2023
Popular DDoS Web Analytics Tools Some popular DDoS web analytics tools include: CloudFlare Web Application Firewall Sucuri Website Firewall Azure Web Application Firewall AWS WAF Imperva Early Warning Signs of a DDoS Attack Having tools like web application firewalls and monitoring services in place are your best defense against a DDoS attack.

SiteLock
AUGUST 27, 2021
With cyberthreats increasing in variety, protecting your website is no longer about installing a basic firewall. You also need to consider the necessary add-ons in all the right places to develop a multi-layered security plan. Add-Ons That Help Website Security. CDN Deployment.

eSecurity Planet
MARCH 15, 2021
Also Read: Microsegmentation: The Next Evolution in Cybersecurity . Ten years after the conceptual roots of zero trust, the cybersecurity industry has four methods for implementing microsegmentation: network fabric, hypervisor, agent, or NFGWs. The first approach is doubling your network fabric for microsegmentation.

The Last Watchdog
MARCH 26, 2020
Related: Why cybersecurity should reflect societal values An emerging approach, called Network Traffic Analysis , is gaining traction as, in effect, a catch-all network security framework positioned at the highest layer of the networking stack. Just ask Equifax or Capital One.

eSecurity Planet
MARCH 16, 2023
Network security threats weaken the defenses of an enterprise network, endangering proprietary data, critical applications, and the entire IT infrastructure. This guide to major network security threats covers detection methods as well as mitigation strategies for your organization to follow.

eSecurity Planet
MAY 25, 2022
Intrusion detection system (IDS) and intrusion prevention system (IPS) technologies – often combined as intrusion detection and prevention (IDPS) – have been in use for decades, yet they remain important cybersecurity tools even in the face of today’s rapidly changing cyber threats and complex IT environments.

eSecurity Planet
FEBRUARY 23, 2024
An application gateway, also known as an application level gateway (ALG), functions as a critical firewall proxy for network security. Its filtering capability ensures that only certain network application data is transmitted, which has an impact on the security of protocols including FTP, Telnet, RTSP, and BitTorrent.

eSecurity Planet
SEPTEMBER 3, 2022
For example, the 2016 DDoS attack on the Dyn managed domain name service (DNS) caused the DNS service to fail to respond to legitimate DNS inquiries and effectively shut down major sites such as PayPal, Spotify, Twitter, Yelp, and many others. Also read: How to Secure DNS. Types of DDoS Attacks. In 2020 the U.S.
eSecurity Planet
APRIL 14, 2023
Cloudflare’s bot management solution is integrated with its Content Delivery Network (CDN) and web application firewall , which allows for more comprehensive protection against bot attacks. Cloudflare offers a range of security and performance solutions, including DDoS protection and website optimization.
eSecurity Planet
DECEMBER 2, 2021
A next-generation firewall (NGFW) is an important component of network security and represents the third generation of firewall technology. To add to the stateful inspection of network traffic and access control , NGFWs can block modern, sophisticated threats like application-layer attacks and advanced malware.

eSecurity Planet
MARCH 22, 2023
Networks connect devices to each other so that users can access assets such as applications, data, or even other networks such as the internet. Network security protects and monitors the links and the communications within the network using a combination of hardware, software, and enforced policies.

eSecurity Planet
DECEMBER 3, 2021
Fifteen years after the launch of the microblogging social media platform, Twitter remains a dominant public forum for instant communication with individuals and organizations worldwide on a universe of topics, including #cybersecurity. Top Cybersecurity Experts to Follow on Twitter. Binni Shah | @binitamshah. Eva Galperi n | @evacide.

eSecurity Planet
AUGUST 23, 2023
Clearing Tracks Advanced attackers can also take steps to erase traces of their activities, which makes it more difficult for cybersecurity experts to identify and respond to a breach. Endpoint security tools like EDR typically include security software capable of detecting and blocking dangerous attachments, links, and downloads.

eSecurity Planet
FEBRUARY 3, 2021
Since then, much has been learned about the tactics, techniques, and procedures (TTPs) deployed and what steps organizations are taking to harden their network and application security. Read Also: The IoT Cybersecurity Act of 2020: Implications for Devices. Amending firewall rules to allow sensitive, outgoing protocols.

McAfee
DECEMBER 1, 2021
Your Cybersecurity Comic Relief . CVE-2021-20322: Of all the words of mice and men, the saddest are, “it was DNS again.” Palo Alto Networks (PAN) firewalls that use its GlobalProtect Portal VPN running PAN-OS versions older than 8.1.17 Why am I here? . PAN GlobalProtect VPN: CVE-2021-3064 . What is it? .

eSecurity Planet
JUNE 8, 2023
It is very affordable for an organization to enable their security tools and web servers to check for and enforce these protocols. It can be time consuming to establish these protocols on an organization’s DNS servers, but doing so will provide two key benefits.
eSecurity Planet
APRIL 7, 2023
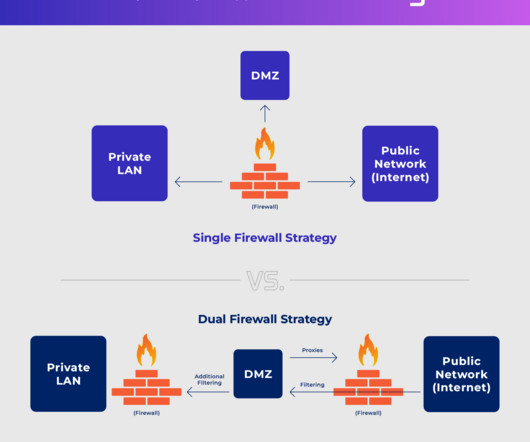
A DMZ network, or a demilitarized zone, is a subnetwork in an enterprise networking environment that contains public-facing resources — such as web servers for company websites — in order to isolate them from an enterprise’s private local area network (LAN).

eSecurity Planet
NOVEMBER 3, 2022
The standard practices for generic cybersecurity defense can provide reasonable protection against DDoS attacks. For effective DDoS defense, priority for patching and updates should be placed on devices between the most valuable resources and the internet such as firewalls, gateways , websites, and applications. Anti-DDoS Architecture.

eSecurity Planet
SEPTEMBER 25, 2023
The lowest tier of Cloudflare One provides support for 50 users maximum, 24 hours of activity logging, and up to three network locations for office-based DNS filtering. Upgrading to the pay-as-you-go tier eliminates any user maximum and provides 30 days of activity logging and 20 office-based DNS filtering network locations.

eSecurity Planet
JULY 28, 2021
We’ll look at what blockchain technology is, how its development relates to cybersecurity, and the state of blockchain-based security solutions. For modern networks, the introduction of new endpoints – be it remote laptops for personnel or client IoT devices – is a roadblock being actively addressed. Block Armour.

eSecurity Planet
FEBRUARY 4, 2022
Antivirus Software WiFi 6 Routers Virtual Private Networks Password Managers Email Security Software Web Application Firewall Bot Management Software. When choosing a VPN, these are the features you should look for: Encryption Multiple server locations to choose from Secure protocols ( WireGuard, OpenVPN , IKEv2/IPSec, etc.)

eSecurity Planet
SEPTEMBER 26, 2023
SD-WAN integration with the SASE controller for Meraki, Catalyst, and others Cisco Umbrella SIG unifies firewall, SWG, DNS-layer security, CASB, and threat intelligence functions into a single and well-tested cloud service.

eSecurity Planet
AUGUST 11, 2023
Implementing SASE Bottom Line: Implement SASE to Improve Security and Operations What Problem Does SASE Solve? Traditional networking either causes operations bottlenecks by forcing all traffic to route through centralized firewalls or exposes remote assets and cloud resources to attack. What Are the SASE Benefits?

eSecurity Planet
FEBRUARY 16, 2021
In general, here are some of the most frequent best practices to protect against malware: Update all network, application, and device software promptly. Boost your organization’s IT literacy with ongoing cybersecurity training so they recognize the threats posed by malware attacks. How to Defend Against a Backdoor.

eSecurity Planet
NOVEMBER 10, 2023
Log monitoring is the process of analyzing log file data produced by applications, systems and devices to look for anomalous events that could signal cybersecurity, performance or other problems. While logs are also used by developers and IT teams to address performance and operations issues, our focus is on the security uses of log data.

eSecurity Planet
MAY 28, 2021
Last week’s RSA Conference covered a litany of network security vulnerabilities, from developing more robust tokenization policies and to addressing UEFI-based attacks, and non-endpoint attack vectors. Sadly, advancements in cybersecurity extend to malicious actors as much as they do to industry professionals.

Cisco Security
AUGUST 26, 2022
Just like the myriad expanding galaxies seen in the latest images from the James Webb space telescope, the cybersecurity landscape consists of a growing number of security technology vendors, each with the goal of addressing the continually evolving threats faced by customers today. New Cisco Secure Endpoint Integrations.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content