DDoS attacks largely target the US and the computers and internet sectors
Tech Republic Security
AUGUST 3, 2021
DDoS attacks are a nuisance to be sure, but they're also used in a variety of ways that make them a severe threat, says Atlas VPN.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Krebs on Security
MAY 23, 2024
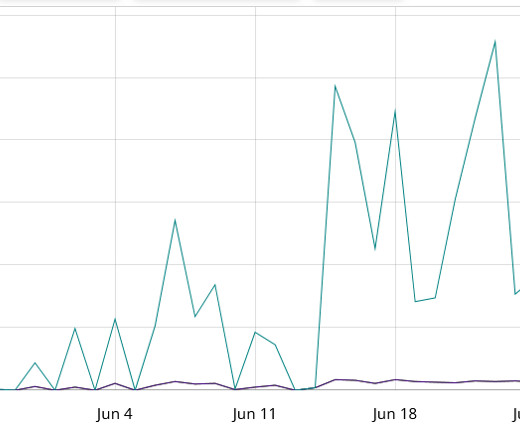
Two weeks before Russia invaded Ukraine in February 2022, a large, mysterious new Internet hosting firm called Stark Industries Solutions materialized and quickly became the epicenter of massive distributed denial-of-service (DDoS) attacks on government and commercial targets in Ukraine and Europe. Image: SentinelOne.com.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
JULY 22, 2023
Researchers warn of several DDoS botnets exploiting a critical flaw tracked as CVE-2023-28771 in Zyxel devices. Fortinet FortiGuard Labs researchers warned of multiple DDoS botnets exploiting a vulnerability impacting multiple Zyxel firewalls. through 4.73, VPN series firmware versions 4.60 through 5.35.

Krebs on Security
MARCH 20, 2020
In February, hardware maker Zyxel fixed a zero-day vulnerability in its routers and VPN firewall products after KrebsOnSecurity told the company the flaw was being abused by attackers to break into devices. For those devices, Zyxel’s advice was not to leave them connected to the Internet. Image: Palo Alto Networks.
Security Affairs
MARCH 10, 2022
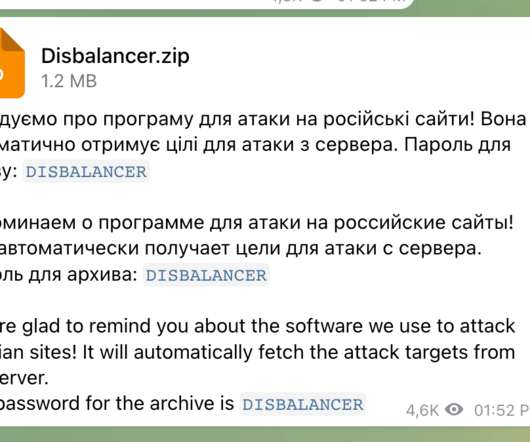
Cisco Talos researchers have uncovered a malware campaign targeting Ukraine’s IT Army , threat actors are using infostealer malware mimicking a DDoS tool called the “Liberator.” Liberator is advertised as a DDoS tool to launch attacks against “Russian propaganda websites.” ” continues the report.
Security Affairs
APRIL 28, 2020
Timetv.live is the latest Azeri news site targeted by Denial of Service (DDoS) attacks launched by Sandman threat actor, the attack took place on March 21, 2020. After reviewing the attack logs of the Denial of Service, Qurium could quickly determine that the attacker was using Fineproxy VPN service to build a botnet to flood the website.

Krebs on Security
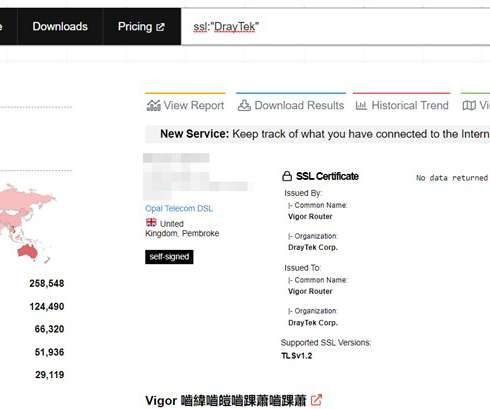
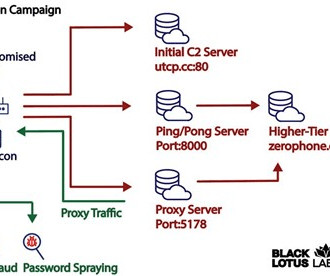
JULY 25, 2023
Researchers this month uncovered a two-year-old Linux-based remote access trojan dubbed AVrecon that enslaves Internet routers into botnet that bilks online advertisers and performs password-spraying attacks. SocksEscort[.]com com , is what’s known as a “SOCKS Proxy” service. SocksEscort began in 2009 as “ super-socks[.]com

Malwarebytes
MARCH 29, 2022
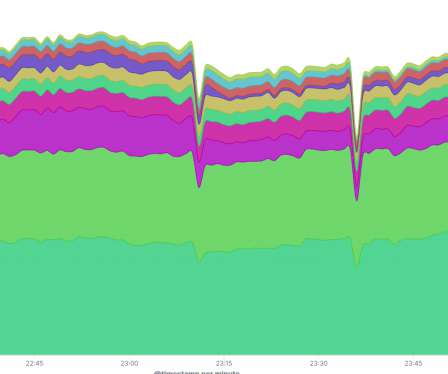
NetBlocks is a global Internet monitor based in London. It uses “diffscans”, which map the IP address space of a country in real time, and show Internet connectivity levels and corresponding outages. A tried and tested method to disrupt communications is to overload the network(s) with a Distributed Denial of Service (DDoS) attack.

Krebs on Security
MAY 22, 2023
Chaput said the spammers used more than 1,500 Internet addresses across 400 providers to register new accounts, which then followed popular accounts on Mastodon and sent private mentions to the followers of those accounts. Shortly after that, those same servers came under a sustained distributed denial-of-service (DDoS) attack.

Security Affairs
JUNE 1, 2023
through 4.73, VPN series firmware versions 4.60 VPN ZLD V4.60 The researchers warned that as of May 19, there were at least 42,000 instances of Zyxel devices on the public internet. Mirai botnets are frequently used to conduct DDoS attacks.” through 5.35, USG FLEX series firmware versions 4.60 USG FLEX ZLD V4.60

SecureList
NOVEMBER 23, 2023
Internet segmentation Amid growing geopolitical tensions, some web resources have blocked users from certain countries and regions. There are two main reasons for that: political pressure and DDoS attacks. In the other case, organizations use geofencing to protect their resources from DDoS attacks.

Malwarebytes
SEPTEMBER 15, 2023
The report follows the Internet Organized Crime Assessment (IOCTA), Europol’s assessment of the cybercrime landscape and how it has changed over the last 24 months. The Russian conflict with Ukraine led to a significant boost in Distributed Denial of Service (DDoS) attacks against EU targets. Prevent intrusions.
IT Security Guru
JANUARY 3, 2024
Swarming or DDoS attacks pose a threat to streamers. Multiple devices flooding your internet connection with traffic can cause slowdowns or crashes. A reliable VPN provider always maintains a DDoS-protected server. In this article, we will continue to explore how a VPN can fortify your Twitch stream.

Security Boulevard
SEPTEMBER 15, 2021
ris Botnet Breaks DDoS Record Targeting Russian Internet Giant Yandex. Groove Ransomware Group Leaks Credentials of 87,000 FortiGate SSL VPN Devices. Here are the top security stories from recent weeks: . Microsoft Fixes Vulnerabilities in Azure Allowing Hackers to Execute Code and Gain Data in Customer Containers.

Security Affairs
DECEMBER 22, 2022
Microsoft Threat Intelligence Center (MSTIC) researchers discovered a new variant of the Zerobot botnet (aka ZeroStresser) that was improved with the capabilities to target more Internet of Things (IoT) devices. com) with links to the bot was among the 48 domains associated with DDoS-for-hire services seized by the FBI in December.

SiteLock
AUGUST 27, 2021
Simply defined, the internet of things (IoT) is a network of Internet-connected objects able to collect and exchange data. To help avoid these online risks, it is highly recommended to use a Virtual Private Network (VPN). VPNs are the baseline cybersecurity tool to safeguard internet-enabled devices and a home network.
Security Affairs
AUGUST 4, 2022
“The attack can be performed without user interaction if the management interface of the device has been configured to be internet facing. “By default, this attack is reachable on the LAN and may be reachable via the internet (WAN) as well if the user has enabled remote web management on their device.

SecureList
SEPTEMBER 21, 2023
Dark web services: DDoS attacks, botnets, and zero-day IoT vulnerabilities Of all IoT-related services offered on the dark web, DDoS attacks are worth examining first. See translation I’m the world’s best-known DDoS attacker for hire (getting ahead of myself here). Our advantages: 1. Tested, tried.

Security Affairs
JUNE 21, 2020
Maze ransomware gang hacked M&A firm Threadstone Advisors LLP Ransomware attack disrupts operations at Australian beverage company Lion Tech firms suspend use of ‘biased facial recognition technology Accessories giant Claires is the victim of a Magecart attack, credit card data exposed Black Kingdom ransomware operators exploit Pulse VPN flaws (..)

eSecurity Planet
APRIL 15, 2024
Threats range from severe weaknesses in Ivanti’s VPN appliances to zero-day exploits in popular software such as Palo Alto Networks’ PAN-OS and Telegram’s Windows client. These issues affect over 91,000 exposed machines, putting them at risk of DDoS assaults, account theft, and malware infestations.

Security Affairs
OCTOBER 10, 2019
. “The vulnerability can be potentially exploited by sending a malicious request to either the Web Admin or SSL VPN consoles, which would enable an unauthenticated remote attacker to execute arbitrary commands.” Cyberoam Firewall protects organizations from DoS , DDoS and IP Spoofing attacks. said the spokesperson.

Security Affairs
NOVEMBER 26, 2021
Resecurity, a Los Angeles-based cybersecurity company has identified an active a zero-day vulnerability in the TP-Link device with model number TL-XVR1800L (Enterprise AX1800 Dual Band Gigabit Wi-Fi 6 Wireless VPN Router), which is primarily suited to enterprises.
Security Affairs
JULY 14, 2023
. “The manner of attack seems to focus predominantly on stealing bandwidth – without impacting end-users – in order to create a residential proxy service to help launder malicious activity and avoid attracting the same level of attention from Tor-hidden services or commercially available VPN services.”

Security Affairs
SEPTEMBER 27, 2020
fitness chains Town Sports leaked online Group-IB detects a series of ransomware attacks by OldGremlin HOW DO PROVIDERS IMPLEMENT INTERNET BLOCKING IN BELARUS? Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.

Malwarebytes
JUNE 26, 2023
Poorly configured Linux and Internet of Things (IoT) devices are at risk of compromise from a cryptojacking campaign , according to researchers at Microsoft. A portion of the install makes use of an open-source IRC bot with Distributed Denial of Service (DDoS) features. When possible, update OpenSSH to the latest version.

eSecurity Planet
APRIL 19, 2023
RADIUS and TACACS+ apply to specific types of endpoints, but the ZTNA-as-a-Service product works for all kinds of devices, including Bring-Your-Own-Device (BYOD) endpoints, Internet-of-Things (IoT) devices, operations technology (OT), industrial control systems (ICS), and industrial IoT (IIoT).

SecureList
DECEMBER 14, 2022
The Viasat “cyberevent” On the 24 th of February , Europeans who relied on the ViaSat-owned “ KA-SAT ” satellite faced major Internet access disruptions. Taking sides: professional ransomware groups, hacktivists, and DDoS attacks. As soon as the attack stops, the target website becomes available again.

Malwarebytes
SEPTEMBER 20, 2022
Kiwi Farms, which gained a reputation for sophisticated trolling and doxxing , was recently dropped by Cloudflare after a sustained campaign to have the DDoS mitigation and cloud hosting service abandon the forum. The latter is a commercial internet forum software package written in PHP.

SiteLock
FEBRUARY 15, 2022
According to the International Data Corporation, by 2025 nearly 56 billion devices will be connected to the internet throughout the world. Meanwhile, Cisco estimates that the number of distributed denial-of-service (DDoS) attacks will nearly double from 7.8 million in 2018 to 15.4 million in 2023.

SecureList
MAY 10, 2021
Botnet operators use infected devices to carry out DDoS attacks or mine cryptocurrency. In Q1 2021, cybercriminals also found a host of new tools for amplifying DDoS attacks. RDP servers listening on UDP port 3389 were used to amplify DDoS attacks. That said, a VPN is no panacea if it too is vulnerable to amplification attacks.

Security Affairs
DECEMBER 8, 2019
Europol seized 30,506 Internet domain names for IP Infringement. China used the Great Cannon DDoS Tool against forum used by Hong Kong protestors. CVE-2019-14899 flaw allows hijacking VPN connections on Linux, Unix systems. Google warned 12K+ users targeted by state-sponsored hackers. The evolutions of APT28 attacks.

eSecurity Planet
NOVEMBER 3, 2022
Distributed denial of service (DDoS) attacks seek to cripple a corporate resource such as applications, web sites, servers, and routers, which can quickly lead to steep losses for victims. However, DDoS attackers sometimes even target the specific computers (or routers) of unwary people – often to harass video gamers, for example.

Adam Levin
FEBRUARY 10, 2020
Most likely you didn’t pause before you clicked, and got phished or compromised in some other way–possibly by an internet of things device connected to your home network. Distributed denial of service attacks (DDoS) are a very likely mode of attack. Tip: Back up everything (for more, see below). Your Finances Glitch.

eSecurity Planet
FEBRUARY 4, 2022
Malware is one of the biggest threats businesses face, and with nearly a third of all malware coming through the internet and email, businesses and consumers alike need ways to protect themselves. This guide covers the major categories of internet security suites and includes a few of the top options for each. Key Features of a VPN.

SecureWorld News
OCTOBER 22, 2023
Enforce enterprise-grade antivirus, firewalls, and internet security software across all connected devices. Document how security incidents like data breaches, insider threats, phishing attacks, DDoS (distributed denial-of-service), and malware infections will be reported, contained, and reported on.

SecureList
NOVEMBER 23, 2021
Also, many groups relied on vulnerabilities in VPN servers. An incident investigation conducted by Kaspersky ICS CERT at one of the attacked enterprises revealed that they exploited a vulnerability in FortiGate VPN servers (CVE-2018-13379). If not ransomware, then DDoS or possibly both. We also saw attackers relying on 0-days.

Security Affairs
OCTOBER 13, 2020
The number of sensors and smart devices connected to the internet is exponentially rising, which are the 5 Major Vulnerabilities for IoT devices. Unfortunately, at that moment, there were over 300,000 of those cameras connected to the internet. Nowadays, malware is an indispensable part of the internet (even if we do not like it).

eSecurity Planet
JANUARY 14, 2022
Distributed denial of service (DDoS) attacks can cripple an organization, a network, or even an entire country, and they show no sign of slowing down. DDoS attacks may only make up a small percentage of security threats, but their consequences can be devastating. According to Imperva Research Labs, DDoS attacks tend to come in waves.

SiteLock
AUGUST 27, 2021
Dictionary.com defines it as: precautions taken to guard against crime that involves the internet, especially unauthorized access to computer systems and data connected to the internet. As the name implies, website security protects a website from cyber threats on the internet. However, there is much more to it than that.

BH Consulting
DECEMBER 14, 2021
At a time of year when many security professionals are putting the finishing touches to budget proposals, the latest Internet Organised Crime Threat Assessment (IOCTA) has outlined the key risks facing organisations in Europe. In last month’s newsletter, we looked at why using a VPN doesn’t always protect the user.

IT Security Guru
JULY 19, 2021
The internet can provide attackers all the knowledge they need about a company’s infrastructure to launch an attack, and organisations need to review how much information on their infrastructure they’re presenting online. Even security defences themselves can provide unintended insights. Consider Zero Trust.

SecureWorld News
NOVEMBER 12, 2020
Distributed Denial of Service (DDoS). Using Remote Desktop Protocol (RDP) continues to be one of the riskiest moves by organizations: "Unfortunately, many organisations still use RDP instead of the more secure Virtual Private Network (VPN) for remote access. Web-based Attacks. Web Application Attacks. Identity Theft. Data Breach.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?




Let's personalize your content