Gamblers’ data compromised after casino giant Strendus fails to set password
Security Affairs
NOVEMBER 15, 2023
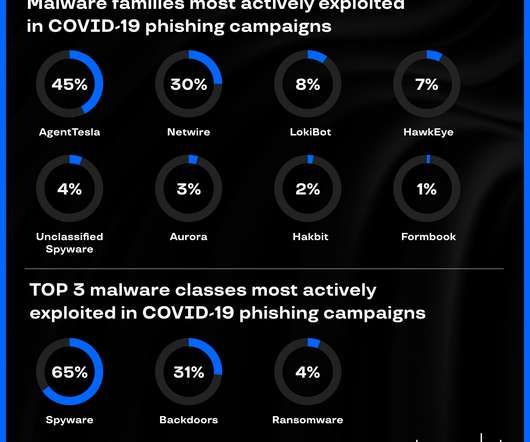
Source: Cybernews The exposed phone numbers can be exploited for spam, malware and spyware attacks, SIM swapping, and the discovery of user accounts on platforms like WhatsApp, Signal, and others. Notes on users, submitted by admins and customer support agents. The leaked IP addresses introduce the risk of a takeover of a local network.































Let's personalize your content