How To Set Up DMZ on Servers: 7-Step DMZ Configuration
eSecurity Planet
APRIL 30, 2024
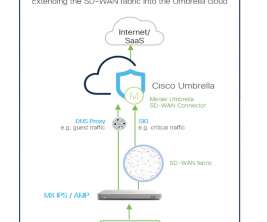
It’s important to prepare the network and firewalls in advance, then follow seven major steps to configure your DMZ’s protocols and rules. We recommend determining in advance every service you want to host, how many firewalls you plan to implement, and which traffic you want to allow and block.
















































Let's personalize your content