Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

eSecurity Planet
NOVEMBER 10, 2023
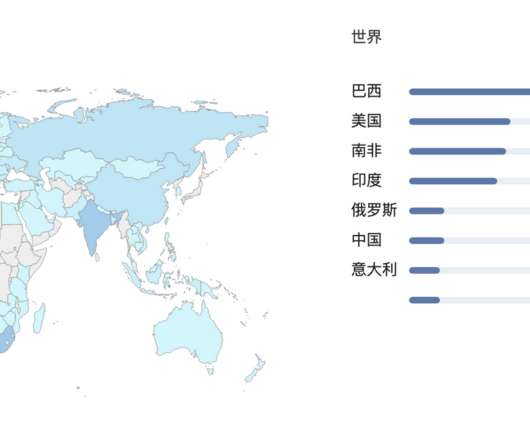
DNS security protects the domain name system (DNS) from attackers seeking to reroute traffic to malicious sites. Since a majority of business IT traffic now accesses or passes through the internet, DNS plays an increasingly important — and vulnerable — role.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
FEBRUARY 14, 2024
Stateful inspection is a firewall feature that filters data packets based on the context of previous data packets. This important feature uses header information from established communication connections to improve overall security. Table of Contents Toggle How Does Stateful Inspection Work? Stateless protocols (UDP, HTTP, etc.)
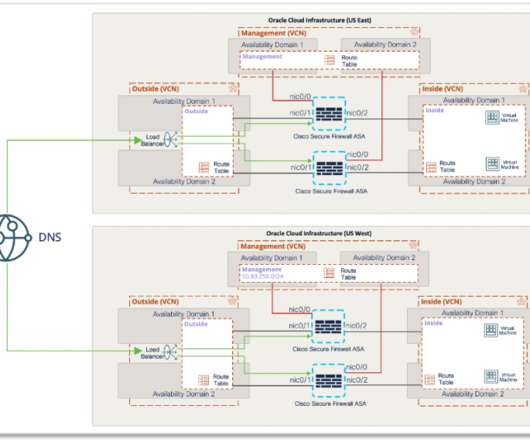
Cisco Security
JULY 9, 2021
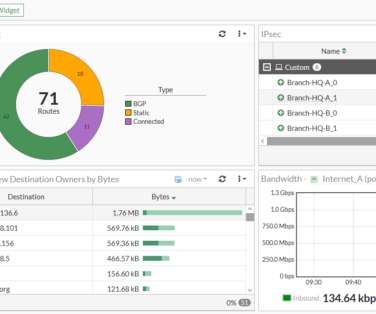
With Cisco Secure Firewall, organizations are able to build a scalable RAVPN architecture on OCI, providing employees secure remote access to their organization’s resources from any location or endpoint. It enforces security at the DNS layer to block malware, phishing, and command and control callbacks over any port.

SC Magazine
MARCH 4, 2021
The National Security Agency (NSA) and Cybersecurity and Infrastructure Agency (CISA) released a joint information sheet Thursday that offers guidance on the benefits of using a Protective Domain Name System (PDNS). A PDNS service uses existing DNS protocols and architecture to analyze DNS queries and mitigate threats.

CyberSecurity Insiders
MAY 18, 2022
But what are your options for proactive protection when the notion of a walled-in network has been shattered by the proliferation of new IoT devices, growth of cloud services, and new hybrid work from home models? When malware first breaches a network, it doesn’t make its presence known right away. So where do we go from here?
Webroot
FEBRUARY 16, 2021
In recent months, you’ve likely heard about DNS over HTTPS , also known as DNS 2.0 and DoH, which is a method that uses the HTTPS protocol to encrypt DNS requests, shielding their contents from malicious actors and others who might misuse such information. Ultimately, this DNS privacy upgrade has been a long time coming.
Webroot
MARCH 29, 2021
A firewall with the right threat intelligence embedded could have blocked communications with the command-and-control server thus preventing a Trojanized Orion install from connecting back to the attackers and stopping them from furthering the attack. Outside of the corporate firewall, it is the Wild West.

The Last Watchdog
DECEMBER 13, 2020
The problem here is that a secured, cost-effective, and efficient networkmust be developed to support remote operations at scale. Many enterprises have accelerated their use of Virtual Private Network (VPN) solutions to support remote workers during this pandemic. The makeup of SASE . But it much further. The cyber threats landscape.

CyberSecurity Insiders
MARCH 21, 2021
When it comes to protecting your small business from cyber attacks, the first and foremost thing is to upgrade your network security and IT infrastructure to the latest standards. Modern technology comes with improved network security offering higher protection. . Build a cyber security plan . Firewalls .
Cisco Security
AUGUST 11, 2021
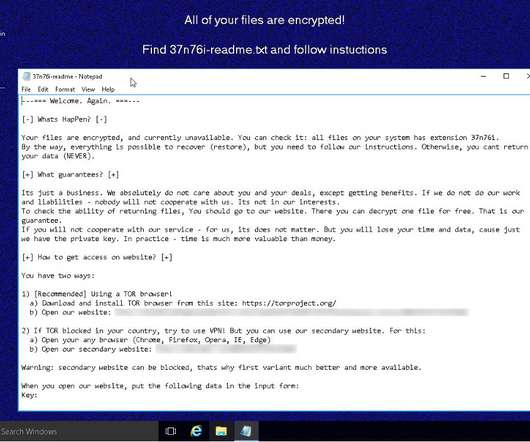
We looked at REvil, also known as Sodinokibi or Sodin, earlier in the year in a Threat Trends blog on DNS Security. In it we talked about how REvil/Sodinokibi compromised far more endpoints than Ryuk, but had far less DNS communication. Figure 1-DNS activity surrounding REvil/Sodinokibi. Changing firewall rules.

eSecurity Planet
DECEMBER 8, 2023
Domain name service (DNS) attacks threaten every internet connection because they can deny, intercept, and hijack connections. With the internet playing an increasing role in business, securing DNS plays a critical role in both operations and security. Everything You Need to Know.

eSecurity Planet
APRIL 26, 2024
Network security architecture is a strategy that provides formal processes to design robust and secure networks. Effective implementation improves data throughput, system reliability, and overall security for any organization.

eSecurity Planet
JULY 25, 2022
The domain name system (DNS) is basically a directory of addresses for the internet. Your browser uses DNS to find the IP for a specific service. For example, when you enter esecurityplanet.com, the browser queries a DNS service to reach the matching servers, but it’s also used when you send an email. DNS spoofing or poisoning.
Security Affairs
OCTOBER 5, 2020
Security researchers provided technical details about an IoT botnet dubbed Ttint that has been exploiting two zero-days in Tenda routers. Security researchers at Netlab, the network security division Qihoo 360, have published a report that details an IoT botnet dubbed Ttint.

eSecurity Planet
MARCH 14, 2023
Network security creates shielded, monitored, and secure communications between users and assets. Securing the expanding, sprawling, and sometimes conflicting collection of technologies that make up network security provides constant challenges for security professionals.

SiteLock
AUGUST 27, 2021
With cyberthreats increasing in variety, protecting your website is no longer about installing a basic firewall. You also need to consider the necessary add-ons in all the right places to develop a multi-layered security plan. Add-Ons That Help Website Security. CDN Deployment.

eSecurity Planet
MAY 25, 2022
An ideal security stack provides continuous protection without gaps. IDS and IPS solutions help fill in the gaps between endpoint protection , firewalls , and other parts of the security stack. Why We Still Need Network Detection and Protection. Also read: Best Network Monitoring Tools.

Cisco Security
JUNE 15, 2021
As a network and workload security strategy leader, I spend a lot of time thinking about the future of the good old network firewall. Spoiler alert: I’m not going to join the cool club of pronouncing the firewall dead. Insert Your Firewall Here. How this insertion happens is changing quite rapidly, though.

eSecurity Planet
MARCH 15, 2021
Ten years after the conceptual roots of zero trust, the cybersecurity industry has four methods for implementing microsegmentation: network fabric, hypervisor, agent, or NFGWs. While all four approaches can help your organization move towards microsegmentation, some are critical to comprehensive network security. .

eSecurity Planet
MARCH 16, 2023
Network security threats weaken the defenses of an enterprise network, endangering proprietary data, critical applications, and the entire IT infrastructure. This guide to major network security threats covers detection methods as well as mitigation strategies for your organization to follow.

eSecurity Planet
FEBRUARY 16, 2021
Malware, short for “malicious software,” is any unwanted software on your computer that, more often than not, is designed to inflict damage. Since the early days of computing, a wide range of malware types with varying functions have emerged. Rogue security software. Best Practices to Defend Against Malware.

Pen Test Partners
SEPTEMBER 13, 2023
Section 6 A requirement coming into force in March 2025 is that organisations will need to have a web application firewall in place for any web applications exposed to the internet. IDS/IPS solutions must detect and alert on any covert malware communications being used such as DNS tunnelling.

eSecurity Planet
JUNE 21, 2022
SSCP (Systems Security Certified Practitioner). SSCP from (ISC)2 is a mid-level certification designed for IT administrators, managers, directors, and network security professionals responsible for the hands-on operational security of their organization’s critical assets. As of mid-2022, the cost is $381 USD.

eSecurity Planet
SEPTEMBER 3, 2022
For example, the 2016 DDoS attack on the Dyn managed domain name service (DNS) caused the DNS service to fail to respond to legitimate DNS inquiries and effectively shut down major sites such as PayPal, Spotify, Twitter, Yelp, and many others. Also read: How to Secure DNS. Types of DDoS Attacks.

McAfee
DECEMBER 22, 2021
The log4j vulnerability is helping threat actors to push Kinsing malware via encoded payloads to vulnerable services exposed to the internet. The same unique indicator is also reported as part of other two threat campaign on MVISION Insights: Kinsing Malware Adds Windows to Its Target List. Network Security Platform.

eSecurity Planet
FEBRUARY 3, 2021
Since then, much has been learned about the tactics, techniques, and procedures (TTPs) deployed and what steps organizations are taking to harden their network and application security. APT accessed SolarWinds; injects Sunspot malware. APT removes build VMs malware to avoid detection. The Solorigate malware family.
eSecurity Planet
DECEMBER 2, 2021
A next-generation firewall (NGFW) is an important component of network security and represents the third generation of firewall technology. To add to the stateful inspection of network traffic and access control , NGFWs can block modern, sophisticated threats like application-layer attacks and advanced malware.

eSecurity Planet
MARCH 22, 2023
Networks connect devices to each other so that users can access assets such as applications, data, or even other networks such as the internet. Network security protects and monitors the links and the communications within the network using a combination of hardware, software, and enforced policies.

eSecurity Planet
JUNE 8, 2023
This article explores: What Is Email Security Best Options to Secure Business Email Email Security Best Practices How Email Security Blocks Threats Bottom Line: Email Security What Is Email Security Email security is a concept that protects email accounts, servers, and communications from unauthorized access, data loss, or compromise.

eSecurity Planet
AUGUST 23, 2023
In order to verify the signature, the recipient’s email server will then use the sender’s publicly available key that is provided in DNS records for this domain. Endpoint security tools like EDR typically include security software capable of detecting and blocking dangerous attachments, links, and downloads.

eSecurity Planet
FEBRUARY 4, 2022
Malware is one of the biggest threats businesses face, and with nearly a third of all malware coming through the internet and email, businesses and consumers alike need ways to protect themselves. Also Read: Mobile Malware: Threats and Solutions. DNS leak protection Kill switch No log policy. Antivirus Software.
Security Boulevard
APRIL 18, 2022
These typically include phishing, malware attacks/compromised devices, ransomware, DDoS, unauthorized account creation, and network security rule changes. Maybe it’s DNS reputation on a suspicious IP address or an adversary profile based on the command and control traffic. What’s required to make that call?
Webroot
JUNE 21, 2021
It may be as simple as the deployment of antivirus plus backup and recovery applications for your end users, or a more complex approach with security operations center (SOC) tools or managed response solutions coupled with network security tools such as DNS and Web filtering, network and endpoint firewalls, VPNs, backup and recovery and others.

eSecurity Planet
SEPTEMBER 25, 2023
The lowest tier of Cloudflare One provides support for 50 users maximum, 24 hours of activity logging, and up to three network locations for office-based DNS filtering. Upgrading to the pay-as-you-go tier eliminates any user maximum and provides 30 days of activity logging and 20 office-based DNS filtering network locations.

eSecurity Planet
SEPTEMBER 26, 2023
Pricing & Delivery Cisco+ Secure Connect can be purchased directly from Cisco or through Cisco partners. SD-WAN integration with the SASE controller for Meraki, Catalyst, and others Cisco Umbrella SIG unifies firewall, SWG, DNS-layer security, CASB, and threat intelligence functions into a single and well-tested cloud service.

eSecurity Planet
AUGUST 11, 2023
Implementing SASE Bottom Line: Implement SASE to Improve Security and Operations What Problem Does SASE Solve? Traditional networking either causes operations bottlenecks by forcing all traffic to route through centralized firewalls or exposes remote assets and cloud resources to attack. What Are the SASE Benefits?

Fox IT
JANUARY 12, 2021
After this the adversary dumps the domain admin credentials from the memory of this machine, continues lateral moving through the network, and places Cobalt Strike beacons on servers for increased persistent access into the victim’s network. The DNS-responses weren’t logged. Command and control (TA0011).

eSecurity Planet
DECEMBER 15, 2021
Secure web gateway (SWG) solutions help keep enterprise networks from falling victim to ransomware , malware , and other threats carried by internet traffic and malicious websites. This is accomplished through various components, including malware detection and URL filtering. Malware detection. SSL/TLS decryption.

eSecurity Planet
MAY 28, 2021
Last week’s RSA Conference covered a litany of network security vulnerabilities, from developing more robust tokenization policies and to addressing UEFI-based attacks, and non-endpoint attack vectors. Malware detection has long been a game of signature detection. Ransomware: Encryption, Exfiltration, and Extortion.

Cisco Security
AUGUST 26, 2022
FAMOC manage from Techstep, a Gartner-recognized MMS provider, is an MDM designed to give IT a complete view and absolute control over mobile devices used by the workforce, so that people can work more effectively and securely. New Cisco Cloud Security Integrations. New Cisco Firepower Next-Gen Firewall Integrations.

eSecurity Planet
NOVEMBER 10, 2023
While logs are also used by developers and IT teams to address performance and operations issues, our focus is on the security uses of log data. Windows system logs , which include application, security, system, directory service, DNS server, and file replication service logs, give information on system activities and security incidents.

eSecurity Planet
DECEMBER 17, 2021
Continuous monitoring of unsanctioned applications, malware , security policies, and more. A part of the vendor’s Autonomous Security Engine (ASE) solution, Censornet Cloud Access Security Broker comes integrated with adaptive multi-factor authentication and email and web security. . Palo Alto Networks Features.

Cisco Security
AUGUST 28, 2023
XDR (eXtended Detection and Response) Integrations At Black Hat USA 2023, Cisco Secure was the official Mobile Device Management, DNS (Domain Name Service) and Malware Analysis Provider. We also deployed ThousandEyes for Network Assurance. Investigation of the IP confirmed it was known malicious.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content