Microsoft is Soft-Launching Security Copilot
Schneier on Security
OCTOBER 25, 2023
Microsoft has announced an early access program for its LLM-based security chatbot assistant: Security Copilot. I am curious whether this thing is actually useful.

Schneier on Security
OCTOBER 25, 2023
Microsoft has announced an early access program for its LLM-based security chatbot assistant: Security Copilot. I am curious whether this thing is actually useful.

We Live Security
OCTOBER 25, 2023
ESET Research discover campaigns by the Winter Vivern APT group that exploit a zero-day XSS vulnerability in the Roundcube Webmail server and target governmental entities and a think tank in Europe.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Bleeping Computer
OCTOBER 25, 2023
VMware issued security updates to fix a critical vCenter Server vulnerability that can be exploited to gain remote code execution attacks on vulnerable servers. [.

The Hacker News
OCTOBER 25, 2023
VMware has released security updates to address a critical flaw in the vCenter Server that could result in remote code execution on affected systems. The issue, tracked as CVE-2023-34048 (CVSS score: 9.8), has been described as an out-of-bounds write vulnerability in the implementation of the DCE/RPC protocol.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Dark Reading
OCTOBER 25, 2023
In the race over Citrix's latest vulnerability, the bad guys have a huge head start, with broad implications for businesses and critical infrastructure providers worldwide.

WIRED Threat Level
OCTOBER 25, 2023
Inauthentic accounts on X flocked to its owner’s post about Ukrainian president Vlodymr Zelensky, hailing “Comrade Musk” and boosting pro-Russia propaganda.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Bleeping Computer
OCTOBER 25, 2023
A custom Flipper Zero firmware called 'Xtreme' has added a new feature to perform Bluetooth spam attacks on Android and Windows devices.

The Last Watchdog
OCTOBER 25, 2023
North Andover, Mass., Oct.25, 2023— DataPivot Technologies , a prominent provider of Data Center, Cloud and Data Protection Solutions, understands that healthcare providers today are scrambling to solve complex clinical, operational and patient data backup & recovery challenges. In response to this industry’s data growth and complexity, DataPivot is delivering innovative data protection solutions that are modern, flexible and scalable, empowering their clients to navigate the complexitie
Bleeping Computer
OCTOBER 25, 2023
Microsoft is testing support for the Discovery of Network-designated Resolvers (DNR) internet standard, which enables automated client-side discovery of encrypted DNS servers on local area networks. [.

The Last Watchdog
OCTOBER 25, 2023
Singapore, Oct. 25, 2023 – Hardware cybersecurity solutions pioneer Flexxon (the “Company”) today announced the appointment of ex-Intel and Microsoft executive Mr Ravi Agarwal to its advisory board. An industry veteran with over three decades of experience, Mr Agarwal will lend his extensive expertise to the Company’s strategic growth and innovation strategy across its markets of operation.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

Security Affairs
OCTOBER 25, 2023
Citrix warned of attacks actively exploiting the vulnerability CVE-2023-4966 in NetScaler ADC and Gateway appliances. Citrix is urging administrators to secure all NetScaler ADC and Gateway appliances against the CVE-2023-4966 vulnerability, which is actively exploited in attacks. On October 10, Citrix published a security bulletin related to a critical vulnerability, tracked as CVE-2023-4966, in Citrix NetScaler ADC/Gateway devices. “ Exploits of CVE-2023-4966 on unmitigated appliances have bee

Bleeping Computer
OCTOBER 25, 2023
A proof-of-concept (PoC) exploit is released for the 'Citrix Bleed' vulnerability, tracked as CVE-2023-4966, that allows attackers to retrieve authentication session cookies from vulnerable Citrix NetScaler ADC and NetScaler Gateway appliances. [.

Security Boulevard
OCTOBER 25, 2023
Security flaws in the implementation of the OAuth authentication standard left hundreds of millions of users to at least three popular online sites exposed to possible account takeover by bad actors, according to researchers at Salt Security. The vulnerability resulting from how OAuth (Open Authorization) is integrated into web services platforms is the latest uncovered.

Bleeping Computer
OCTOBER 25, 2023
Windows 11 will let admins mandate SMB client encryption for all outbound connections, starting with today's Windows 11 Insider Preview Build 25982 rolling out to Insiders in the Canary Channel. [.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.
Security Affairs
OCTOBER 25, 2023
Russia-linked threat actor Winter Vivern has been observed exploiting a zero-day flaw in Roundcube webmail software. Russian APT group Winter Vivern (aka TA473) has been observed exploiting a zero-day flaw in Roundcube webmail software on October 11, 2023. ESET researchers pointed out that is a different vulnerability than CVE-2020-35730 , that the group exploited in other attacks.

Bleeping Computer
OCTOBER 25, 2023
The Winter Vivern Russian hacking group has been exploiting a Roundcube Webmail zero-day since at least October 11 to attack European government entities and think tanks. [.

Security Affairs
OCTOBER 25, 2023
VMware addressed a critical out-of-bounds write vulnerability, tracked as CVE-2023-34048, that impacts vCenter Server. vCenter Server is a critical component in VMware virtualization and cloud computing software suite. It serves as a centralized and comprehensive management platform for VMware’s virtualized data centers. The vulnerability CVE-2023-34048 (CVSS score 9.8) is an out-of-bounds write vulnerability in the implementation of the DCERPC protocol. “ vCenter Server contains an

Bleeping Computer
OCTOBER 25, 2023
Japanese watchmaker Seiko has confirmed it suffered a Black Cat ransomware attack earlier this year, warning that the incident has led to a data breach, exposing sensitive customer, partner, and personnel information. [.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

SecureList
OCTOBER 25, 2023
Introduction It’s just another cryptocurrency miner… Nobody would even suspect the mining malware was merely a mask, masquerading behind an intricate modular framework that supports both Linux and Windows. It comes equipped with a built-in TOR network tunnel for communication with command servers, along with update and delivery functionality through trusted services such as GitLab, GitHub, and Bitbucket, all using custom encrypted archives.
Bleeping Computer
OCTOBER 25, 2023
Security researchers hacked the Samsung Galaxy S23 smartphone two more times on the second day of the Pwn2Own 2023 hacking competition in Toronto, Canada. [.

Malwarebytes
OCTOBER 25, 2023
VMWare has issued an update to address one out-of-bounds write and one information disclosure vulnerability in its server management software, vCenter Server. Since there are no in-product workarounds, customers are advised to apply the updates urgently. The affected products are VMware vCenter Server versions 7.0 and 8.0 and VMware Cloud Foundation versions 5.x and 4.x.
Heimadal Security
OCTOBER 25, 2023
BHI Energy, a US energy services company linked to Westinghouse Electric Company, has revealed specifics about a cyberattack on their systems. The Akira ransomware group is responsible for the breach that took place on May 30, 2023. As a division of Westinghouse Electric Company, BHI Energy provides specialized engineering services and staffing solutions to oil […] The post US Energy Company Reveals How Akira Ransomware Compromised its Systems appeared first on Heimdal Security Blog.

Advertisement
The losses companies suffered in 2023 ransomware attacks increased by 74% compared to those of the previous year, according to new data from the Federal Bureau of Investigation (FBI). The true figure is likely to be even higher, though, as many identity theft and phishing attacks go unreported. Ransomware attackers can potentially paralyze not just private sector organizations but also healthcare facilities, schools, and entire police departments.
Dark Reading
OCTOBER 25, 2023
We have too much cybersecurity awareness. It's time to implement repeatable, real-world practice that ingrains positive habits and security behaviors.

Malwarebytes
OCTOBER 25, 2023
In what may come as a surprise, subscription-based face search engine PimEyes seems to have realized that their service can be used for nefarious purposes. PimEyes’ CEO Giorgi Gobronidze told the New York Times that it has taken technical measures to block such searches as part of a “no harm policy.” PimEyes is a search service that uses facial recognition technology to find online photos of people.

Dark Reading
OCTOBER 25, 2023
Cyber threats on satellite technology will persist and evolve. We need a comprehensive cybersecurity framework to protect them from attackers.

Bleeping Computer
OCTOBER 25, 2023
Ransomware incidents continue to grow at an alarming pace, targeting the enterprise and governments worldwide. Learn more from Specops Software on how ransomware gangs gain initial access to networks and how to protect against attacks. [.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?

The Hacker News
OCTOBER 25, 2023
The threat actor known as Winter Vivern has been observed exploiting a zero-day flaw in Roundcube webmail software on October 11, 2023, to harvest email messages from victims' accounts. "Winter Vivern has stepped up its operations by using a zero-day vulnerability in Roundcube," ESET security researcher Matthieu Faou said in a new report published today.

Dark Reading
OCTOBER 25, 2023
VMware vCenter Servers need immediate patch against critical RCE bug as race against threat actors begins.

The Hacker News
OCTOBER 25, 2023
In today's digital landscape, around 60% of corporate data now resides in the cloud, with Amazon S3 standing as the backbone of data storage for many major corporations. Despite S3 being a secure service from a reputable provider, its pivotal role in handling vast amounts of sensitive data (customer personal information, financial data, intellectual property, etc.
Duo's Security Blog
OCTOBER 25, 2023
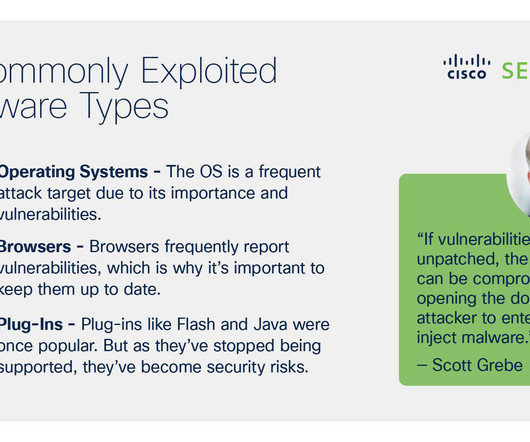
You may be familiar with Cisco’s slogan, “If it’s connected, it’s protected.” It’s the idea that you need to secure the people and devices that connect to your network from cyberattacks so your organization can continue to move forward. Securing the people, your workforce, has to do with identity and verifying users are who they say they are before they’re allowed to access network applications and resources.

Speaker: Erika R. Bales, Esq.
When we talk about “compliance and security," most companies want to ensure that steps are being taken to protect what they value most – people, data, real or personal property, intellectual property, digital assets, or any other number of other things - and it’s more important than ever that safeguards are in place. Let’s step back and focus on the idea that no matter how complicated the compliance and security regime, it should be able to be distilled down to a checklist.
Let's personalize your content