How is information stored in cloud secure from hacks
CyberSecurity Insiders
MAY 14, 2023
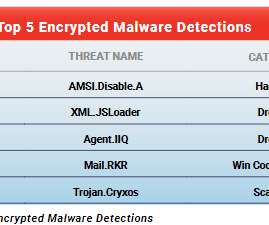
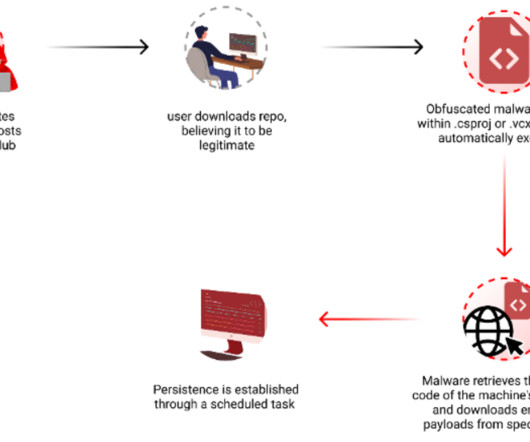
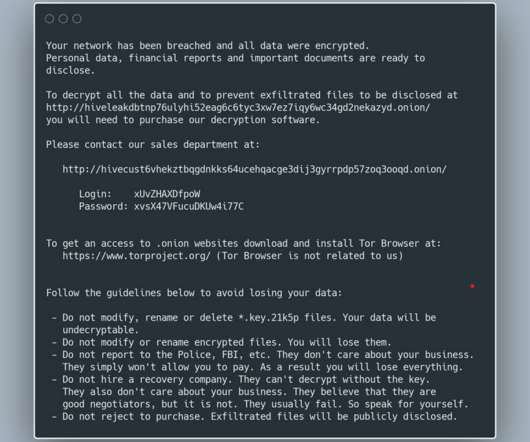
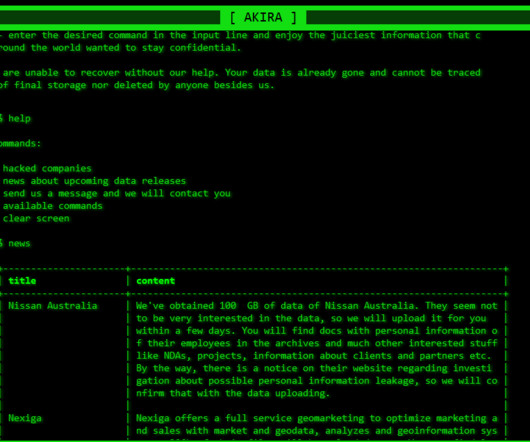
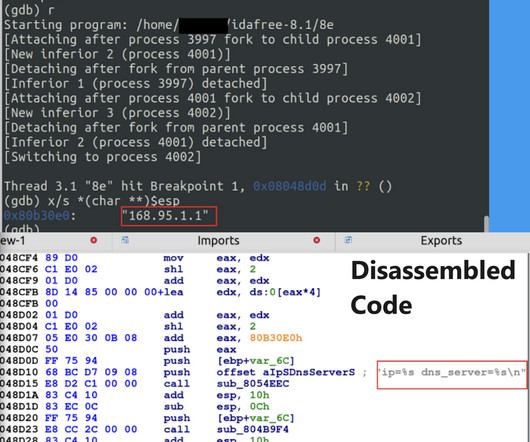
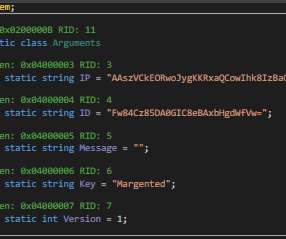
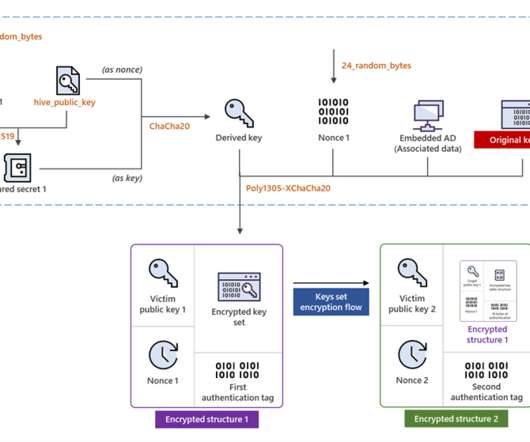
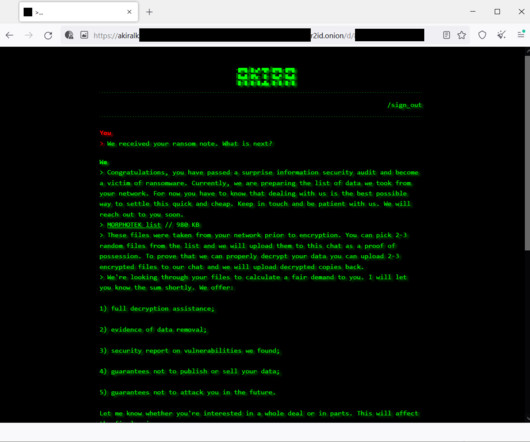
Cloud storage services have become a target for hackers, and the theft of personal and sensitive information can have serious consequences. So, how is information stored in the cloud secured from hacks? One way to secure information in the cloud is through encryption.
























Let's personalize your content