Astaroth malware uses YouTube channel descriptions for hacks
SecureBlitz
FEBRUARY 21, 2024
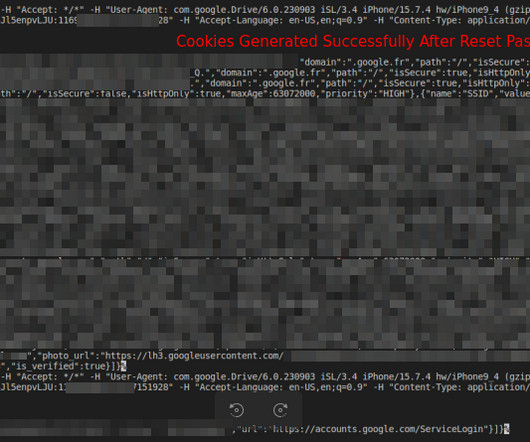
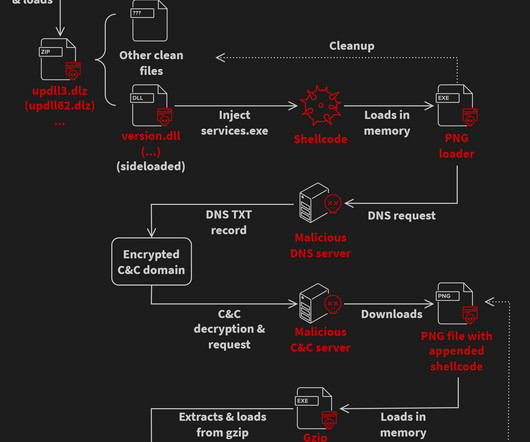
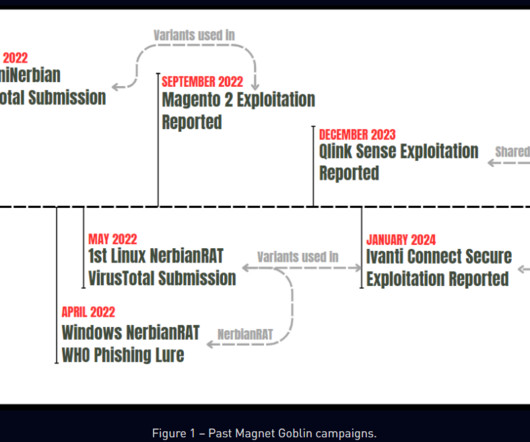
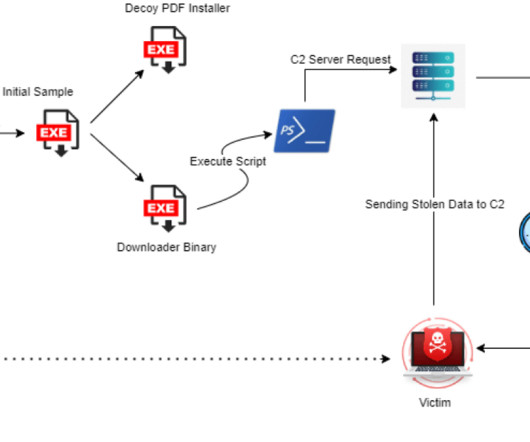
In 2020, the digital landscape witnessed a cunning maneuver by the infamous Astaroth malware. Cisco Talos researchers first uncovered this devious strategy, revealing that Astaroth embedded encrypted and […] The post Astaroth malware uses YouTube channel descriptions for hacks appeared first on SecureBlitz Cybersecurity.


























Let's personalize your content