#World Password Day: Protecting corporate social media passwords
IT Security Guru
MAY 4, 2023
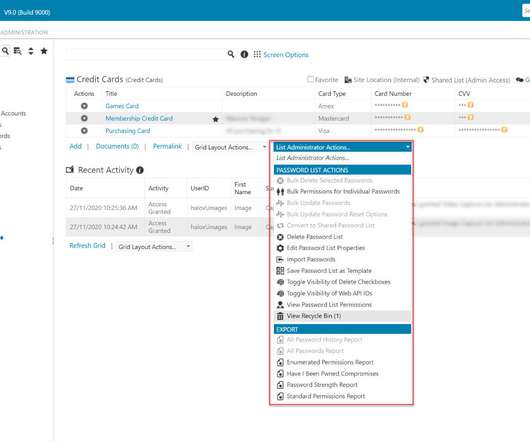
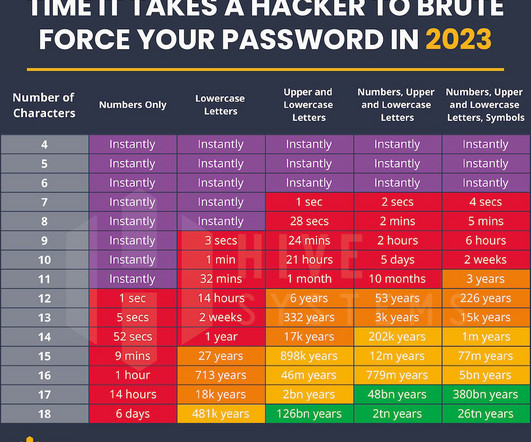
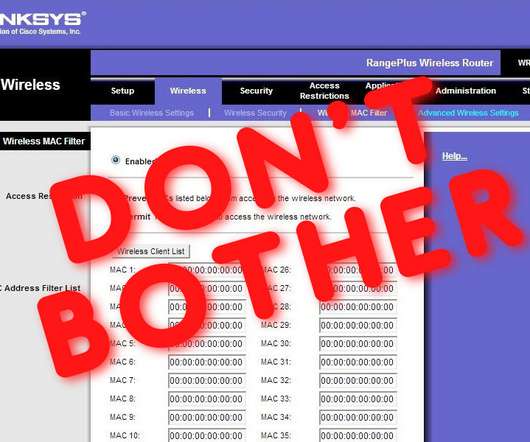
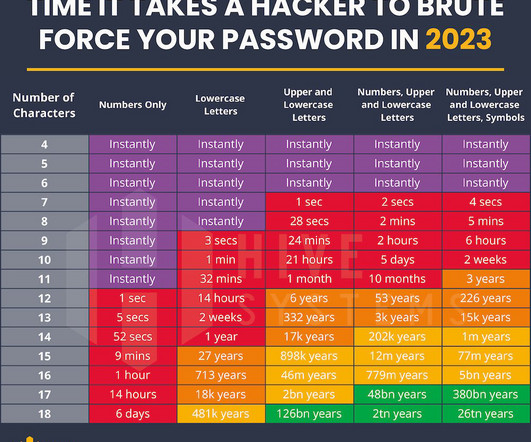
However, social media passwords pose unique security issues that companies are sometimes ill-prepared to address. Whether due to an internal policy or if social media is outsourced to a third party agency, this lack of password security could be putting organisations and their reputations at risk.











































Let's personalize your content