Telecommunications: A Case Study
Approachable Cyber Threats
MARCH 9, 2023
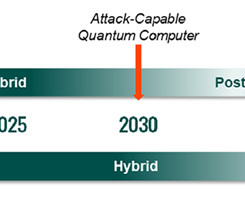
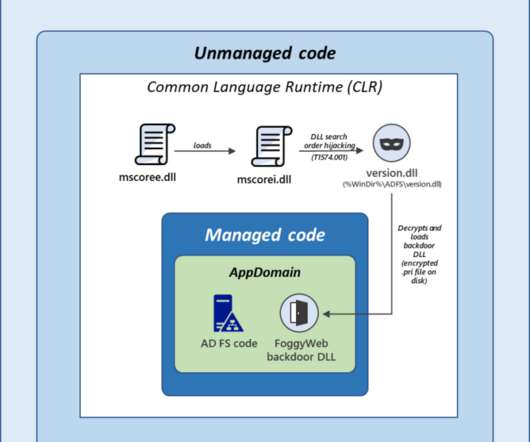
Category Awareness, News, Case Study As one of the world’s fastest-growing industries, telecommunication has become a highly vulnerable target for cybersecurity threats. The Industry Information technology's ability to connect and communicate has become integral to our society here in the digital age. What can be done?










































Let's personalize your content