New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Security Boulevard
APRIL 30, 2024
The post Brits Ban Default Passwords — and More IoT Stupidity appeared first on Security Boulevard. The UK’s Product Security and Telecommunications Infrastructure Act aims to improve the security of net-connected consumer gear.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Krebs on Security
SEPTEMBER 10, 2021
The assault came from “ Meris ,” the same new “Internet of Things” (IoT) botnet behind record-shattering attacks against Russian search giant Yandex this week and internet infrastructure firm Cloudflare earlier this summer. Cloudflare recently wrote about its attack , which clocked in at 17.2

The Last Watchdog
SEPTEMBER 5, 2023
New government rules coupled with industry standards meant to give formal shape to the Internet of Things (IoT) are rapidly quickening around the globe. When it comes to IoT, we must arrive at specific rules of the road if we are to tap into the full potential of smart cities, autonomous transportation and advanced healthcare.

Security Boulevard
MAY 31, 2022
In April of 2013, CNN introduced the world to Shodan, a search engine for internet-connected devices, by publishing an article titled, Shodan: The scariest search engine on the Internet. The post Shodan: Still the Scariest Search Engine on the Internet?

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. As with the rest of the IoT landscape, there's a lot of scope for improvement here and also just like the other IoT posts, it gets very complex for normal people very quickly.

The Last Watchdog
DECEMBER 11, 2022
The Internet of Everything ( IoE ) is on the near horizon. For instance, very visibly over the past decade, Internet of Things ( IoT ) computing devices and sensors have become embedded everywhere. Smart devices and IoT systems are beginning to interconnect with each other and this is only going to continue.”.

Schneier on Security
SEPTEMBER 11, 2018
This is really interesting research: " BlackIoT: IoT Botnet of High Wattage Devices Can Disrupt the Power Grid ": Abstract : We demonstrate that an Internet of Things (IoT) botnet of high wattage devices-such as air conditioners and heaters-gives a unique ability to adversaries to launch large-scale coordinated attacks on the power grid.
Security Boulevard
DECEMBER 9, 2021
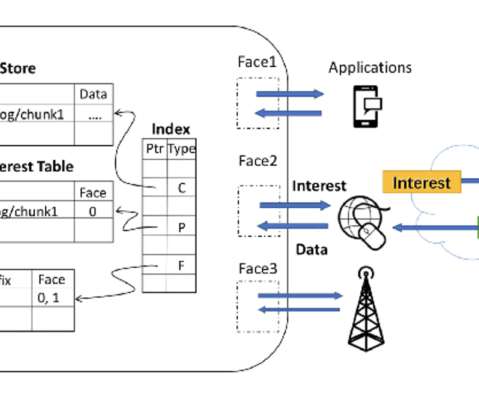
What is Named Data Networking for IoT Source: [link] The rise of the Internet of Things (IoT) has urged a new Internet architecture as IoT differs from the current Internet architecture due to constraints of devices’ resources and enormous volumes of small exchanged data.

Adam Shostack
JUNE 8, 2020
There’s an interesting new draft, Best Practices for IoT Security:What Does That Even Mean? It’s by Christopher Bellman and Paul C. van Oorschot.

The Last Watchdog
MARCH 9, 2020
Their capacity to ingest threat feeds is becoming more relevant with the rise of IoT (Internet of Things) systems and the vulnerabilities of old and new OT (operational technology). Digital transformation is leading to more intensive use of the cloud, faster development of software to support it, and the growth of the IoT.

Malwarebytes
APRIL 30, 2021
Those operating systems and libraries are widely used in smart, Internet-connected “things” The number of affected devices could be enormous. The researchers found that memory allocation implementations written throughout the years as part of IoT devices and embedded software have not incorporated proper input validations.

Heimadal Security
NOVEMBER 12, 2021
BotenaGo is a virus developed in Golang (Go), a programing language that has exploded in popularity in recent years, with malware developers praising it for producing harder-to-detect and reverse-engineer payloads. The post The BotenaGo Botnet Targets IoT Devices appeared first on Heimdal Security Blog.

The Security Ledger
JUNE 29, 2023
Host Paul Roberts speaks with Boyd Multerer, the CEO and founder of Kry10, which has made a secure OS for the Internet of Things. The post Episode 251: Kry10 CEO Boyd Multerer on building a secure OS for the IoT appeared first on The Security Ledger with Paul F. billion active IoT endpoints. billion active IoT endpoints.

SC Magazine
APRIL 30, 2021
The IoT security team at the Microsoft Security Response Center said vulnerabilities discovered affect at least 25 different products made by more than a dozen organizations, including Amazon, ARM, Google Cloud, Samsung, RedHat, Apache and others. A signage of Microsoft is seen on March 13, 2020 in New York City. Jeenah Moon/Getty Images).
Security Affairs
JULY 28, 2020
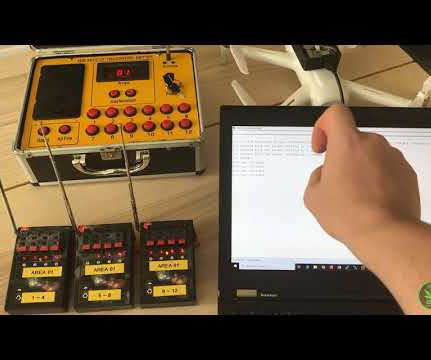
How to hack IoT & RF Devices with BürtleinaBoard. Few months ago I have presented #FocacciaBoard : a similar multipurpose breakout board that uses the famous FT232H to handle multiple protocols commonly found in (I)IoT devices (i.e. The post Hacking IoT & RF Devices with BürtleinaBoard appeared first on Security Affairs.

Security Affairs
AUGUST 17, 2021
FireEye Mandiant researchers have discovered a critical vulnerability in the Kalay cloud platform that exposes millions of IoT devices to attacks. The flaw could be easily exploited by a remote attacker to take over an IoT device, the only info needed for the attack is the Kalay unique identifier (UID) of the targeted user.

Security Affairs
MARCH 28, 2019
Shodan IoT search engine announced the launch of a new service called Shodan Monitor designed to help organizations to maintain track of systems connected to the Internet. Shodan Monitor is a precious tool for organizations that can determine their surface of attack assessing their Internet-exposed systems.

SC Magazine
APRIL 9, 2021
As the Department of Defense works on standards to dictate 5G rollout, security requirements may be too much for IoT manufacturers. Of course, many security hurdles for IoT device manufacturers are not specific to 5G. . The Internet of Things Cybersecurity Improvement Act of 2020 , which was enacted Dec. chapter of AFCEA.

CyberSecurity Insiders
MARCH 25, 2021
billion IoT devices active across the world – a figure that is expected to grow to 75 billion by 2025. This tripling will be a phenomenal feat to achieve in the next four years and relies upon IoT projects that are currently planned or under development to mature quickly. 1 Consider using generic IoT service modules.

Schneier on Security
DECEMBER 19, 2019
These are stupid design decisions made by engineers who had no idea how to create a secure system. And this, in a nutshell, is the problem with the Internet-of-Things. These aren't subtle vulnerabilities. Or anyone could have remotely nabbed the entire trove of customers' data.
Schneier on Security
SEPTEMBER 29, 2020
As expected, IoT devices are filled with vulnerabilities : As a thought experiment, Martin Hron, a researcher at security company Avast, reverse engineered one of the older coffee makers to see what kinds of hacks he could do with it. After just a week of effort, the unqualified answer was: quite a lot.

Security Affairs
JULY 16, 2018
A security researcher discovered that the IoT search engine ZoomEye has cached login passwords for tens of thousands of Dahua DVRs. The IoT search engine ZoomEye has cached login passwords for tens of thousands of Dahua DVRs, the discovery was made by security researcher Ankit Anubhav, Principal Researcher at NewSky Security.

SC Magazine
APRIL 14, 2021
The rapid growth of IoT over the past decade has sent billions of poorly-secured widgets and gadgets into the homes of consumers. Many of these devices connect to the internet, bringing a host of security weaknesses and vulnerabilities that could impact home and even corporate networks. Photo by Justin Sullivan/Getty Images).

ForAllSecure
APRIL 22, 2021
It seems everything smart is hackable, with IoT startups sometimes repeating security mistakes first made decades ago. The next day I cut the string, There's a parallel here to IoT light bulbs that change colors. The question is, who is hacking the internet of things today, and how does one even get started? Funny thing.

ForAllSecure
APRIL 22, 2021
It seems everything smart is hackable, with IoT startups sometimes repeating security mistakes first made decades ago. The next day I cut the string, There's a parallel here to IoT light bulbs that change colors. The question is, who is hacking the internet of things today, and how does one even get started? Funny thing.
Security Affairs
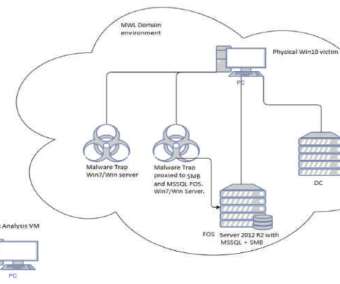
FEBRUARY 8, 2020
Hackers have infected with a piece of malware some IoT devices running Windows 7 designed by three of the world’s largest manufacturers. Security experts from TrapX reported that some IoT devices running Windows 7 have been infected with a piece of malware, is it a supply chain attack? Pierluigi Paganini.
Security Boulevard
MARCH 1, 2024
EKEN IoT FAIL: Amazon, Sears and Shein still sell security swerving stuff. The post Cheap Video Doorbell Cams: Tools of Stalkers and Thieves appeared first on Security Boulevard.

Adam Levin
MARCH 17, 2020
Internet of Things (IoT) devices in general have earned a reputation for poor cybersecurity, and internet-connected cameras are no exception. Setting up a firewall, or configuring your internet router to block unwanted incoming internet traffic can add another level of protection between your home devices and hackers.

Malwarebytes
APRIL 6, 2023
If someone finds out what it is, either from a list online or by socially engineering the victim, the game is indeed up. The Internet of Things can be a perilous place, and the lack of effective security in these tools we entrust our homes to is far from ideal. Also recognize VPN is only as secure as its connected devices.

WIRED Threat Level
OCTOBER 1, 2020
A researcher reverse engineered an internet-connected coffee maker to see what kinds of hacks he could do with it. The answer: quite a lot.

Security Affairs
OCTOBER 1, 2019
Security Labs discovered a new IOT bot named “GUCCI”. It seems like the IOT botnet is named after an Italian luxury brand of fashion and leather goods. The IOT threat detection engine picked the infection IP has shown below hosting number of bins for different architectures. Inference. Pierluigi Paganini.

The Security Ledger
DECEMBER 19, 2023
Security researcher and IoT hacker Dennis Giese talks about his mission to liberate robot vacuums from the control of their manufacturers, letting owners tinker with their own devices and - importantly - control the data they collect about our most intimate surroundings. Forget the IoT. Read the whole entry. »

Malwarebytes
AUGUST 20, 2021
For Internet devices, the network edge is where the device, or the local network containing the device, communicates with the Internet. You may remember hearing about this botnet after the massive East Coast internet outage of 2016 when the Mirai botnet was leveraged in a DDoS attack aimed at Dyn, an Internet infrastructure company.

CyberSecurity Insiders
MAY 28, 2023
Social Engineering: Investigate the human element of cybersecurity by exploring social engineering techniques and tactics used to manipulate individuals. Internet of Things (IoT) Security: Examine the security risks associated with IoT devices, including privacy concerns, data integrity, and device authentication.

Security Through Education
JANUARY 18, 2023
The Internet of Things. IBM describes the internet of things (IoT) as the “the concept of connecting any device … to the Internet and to other connected devices.” Basically, the IoT encompasses anything from smart microwaves and fridges to self-driving cars and fitness devices (to name a few). Rosa Rowles.
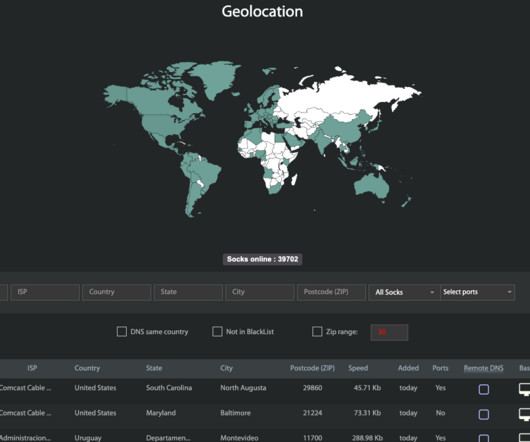
Krebs on Security
APRIL 18, 2023
Kilmer said Faceless has emerged as one of the underground’s most reliable malware-based proxy services, mainly because its proxy network has traditionally included a great many compromised “Internet of Things” devices — such as media sharing servers — that are seldom included on malware or spam block lists.

Thales Cloud Protection & Licensing
NOVEMBER 14, 2018
According to statistica the number of Internet of Things (IoT) devices connected will rise to 23 billion this year. From industrial machinery and intelligent transportation to health monitoring and emergency notification systems, a broad range of IoT devices are already being deployed by enterprises.

Security Affairs
AUGUST 6, 2019
The STRONTIUM Russia-linked APT group is compromising common IoT devices to gain access to several corporate networks. Researchers at Microsoft observed the Russia-linked APT group STRONTIUM abusing IoT devices to gain access to several corporate networks. ” IoT risk must be taken seriously. ” continues Microsoft.

The Security Ledger
NOVEMBER 26, 2018
But what new kinds of Internet of Things use cases may become possible? And, just as important, what are the security implications of massively distributed IoT endpoints connected to capacious 5G cellular infrastructure? But what new kinds of Internet of Things use cases may become possible? Read the whole entry. »

CyberSecurity Insiders
FEBRUARY 12, 2021
With a little help from the power of the Internet of Things ! Whether it is automation in his workshops or upgrading the connectivity of his sleigh, the world of IoT is here to give Santa that little bit of extra support around the jolliest time of the year. Keen to learn about IoT? Making his Elves’ workshop smarter.

The Security Ledger
JULY 26, 2018
In this Spotlight Podcast, sponsored by Trusted Computing Group*, Dennis Mattoon of Microsoft Research gives us the low-down on DICE: the Device Identifier Composition Engine Architectures, which provides a means of solving a range of security and identity problems on low cost, low power IoT endpoints. Read the whole entry. »

Krebs on Security
JULY 25, 2023
Researchers this month uncovered a two-year-old Linux-based remote access trojan dubbed AVrecon that enslaves Internet routers into botnet that bilks online advertisers and performs password-spraying attacks. SocksEscort[.]com com , is what’s known as a “SOCKS Proxy” service.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content