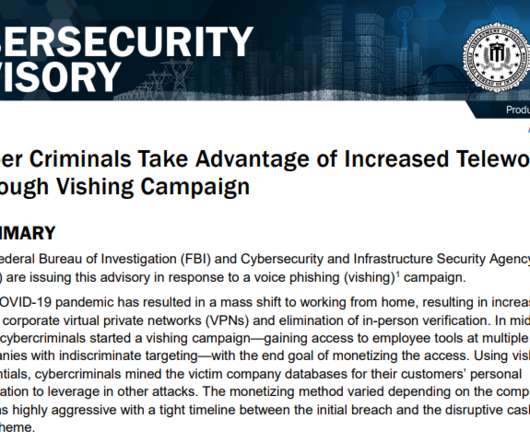
FBI, CISA Echo Warnings on ‘Vishing’ Threat
Krebs on Security
AUGUST 21, 2020
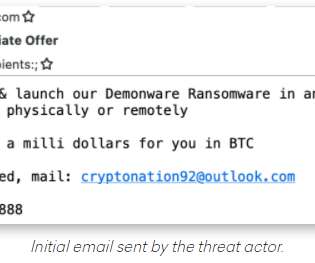
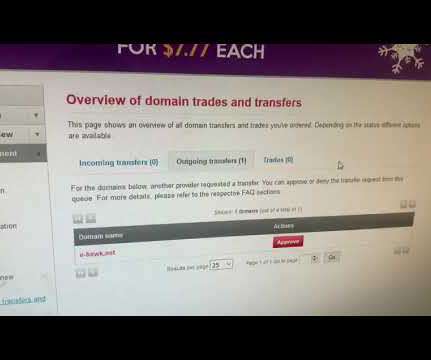
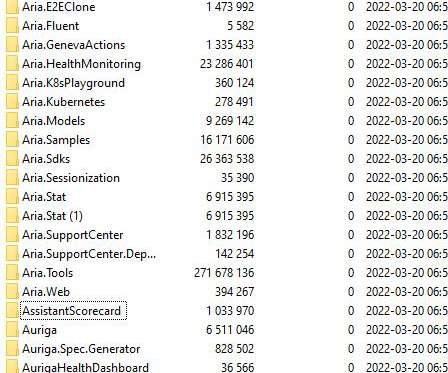
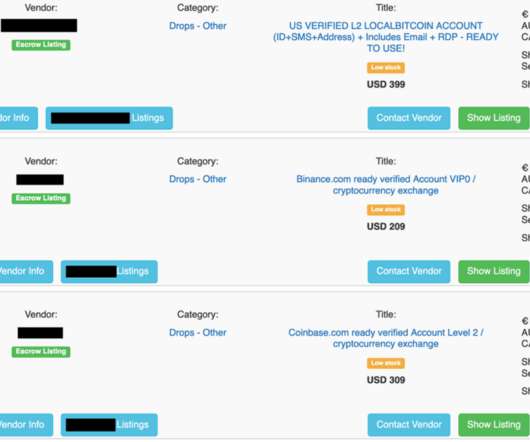
The advisory came less than 24 hours after KrebsOnSecurity published an in-depth look at a crime group offering a service that people can hire to steal VPN credentials and other sensitive data from employees working remotely during the Coronavirus pandemic. authenticate the phone call before sensitive information can be discussed.









































Let's personalize your content