‘Predator’ — Nasty Android Spyware Revealed
Security Boulevard
MAY 30, 2023
Intellexa mercenary spyware chains five unpatched bugs—plus ‘Alien’ technology The post ‘Predator’ — Nasty Android Spyware Revealed appeared first on Security Boulevard.

Security Boulevard
MAY 30, 2023
Intellexa mercenary spyware chains five unpatched bugs—plus ‘Alien’ technology The post ‘Predator’ — Nasty Android Spyware Revealed appeared first on Security Boulevard.
Security Affairs
JANUARY 21, 2022
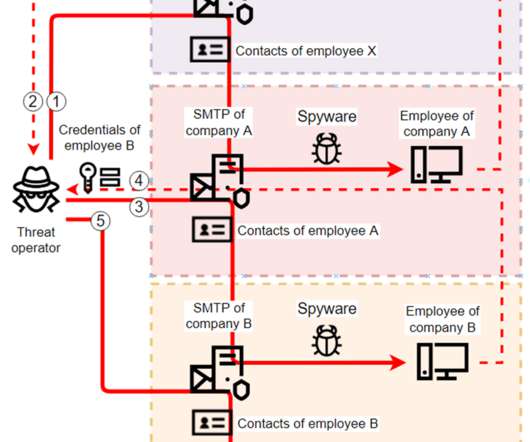
Researchers spotted several spyware campaigns targeting industrial enterprises to steal credentials and conduct financial fraud. Researchers from Kaspersky Lab have uncovered multiple spyware campaigns that target industrial firms to steal email account credentials and carry out fraudulent activities. ” concludes the report.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
JUNE 4, 2023
Xplain hack impacted the Swiss cantonal police and Fedpol Zyxel published guidance for protecting devices from ongoing attacks Kimsuky APT poses as journalists and broadcast writers in its attacks New Linux Ransomware BlackSuit is similar to Royal ransomware CISA adds Progress MOVEit Transfer zero-day to its Known Exploited Vulnerabilities catalog (..)

Hacker's King
MAY 20, 2023
However, if hackers gain access to these tokens through social engineering, phishing attacks, or other means, they can bypass 2FA by directly entering the codes, granting them unauthorized access. Social Engineering: Guarding Against Manipulation Social engineering remains a potent tool in hackers’ arsenal.
SecureList
JANUARY 19, 2022
Kaspersky ICS CERT has uncovered a number of spyware campaigns targeting industrial enterprises. The attackers use off-the-shelf spyware, but limit the scope and lifetime of each sample to the bare minimum. The attackers use off-the-shelf spyware, but limit the scope and lifetime of each sample to the bare minimum.
Security Affairs
JUNE 11, 2023
Gox exchange and operating BTC-e Japanese Pharmaceutical giant Eisai hit by a ransomware attack Clop ransomware gang was testing MOVEit Transfer bug since 2021 Stealth Soldier backdoor used is targeted espionage attacks in Libya Researchers published PoC exploit code for actively exploited Windows elevation of privilege issue Experts detail a new Kimsuky (..)

Security Affairs
MARCH 25, 2021
Facebook has closed accounts used by a China-linked APT to distribute malware to spy on Uyghurs activists, journalists, and dissidents living outside China. This group used various cyber-espionage tactics to identify its targets and infect their devices with malware to enable surveillance.” ” concludes the report.
Let's personalize your content