10 Tips for More Secure Mobile Devices
Dark Reading
JUNE 27, 2018
Mobile devices can be more secure than traditional desktop machines - but only if the proper policies and practices are in place and in use.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 mobile-security 10-tips-for-more-secure-mobile-devices
mobile-security 10-tips-for-more-secure-mobile-devices 
Dark Reading
JUNE 27, 2018
Mobile devices can be more secure than traditional desktop machines - but only if the proper policies and practices are in place and in use.

Webroot
APRIL 3, 2024
10 tips to keep your identity safe online Here are some practical tips to help you keep your identity safe online: Get the latest anti-virus software Investing in reliable anti-virus software is like putting a protective shield around your devices, such as your PCs, Macs, mobile devices, Chromebooks, and tablets.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Malwarebytes
MAY 7, 2023
Last week on Malwarebytes Labs: How to protect your small business from social engineering Microsoft: You're already using the last version of Windows 10 Is it OK to train an AI on your images, without permission? Want to learn more about how we can help protect your business? Upcoming webinar: Is EDR or MDR better for your business?

The Last Watchdog
JUNE 18, 2018
They are scrambling to invent and deliver a fresh portfolio of mobile banking services that appeal to millennials. Related articles: Hackers revamp tactics, target mobile wallets. Convenience must be delicately balanced against security. Chicago-based VASCO has been around since 1991 and has more than 600 employees.

eSecurity Planet
FEBRUARY 13, 2023
Application security is the practice of securing software and data from hackers, whether that application comes from a third party or was developed in house, regardless of where it resides or how it’s accessed. How Does Application Security Work? What Are the Types of Application Security?

eSecurity Planet
OCTOBER 30, 2023
Is it better to stress now, or stress more later? It can also be a challenge for security and IT pros even to know everything they own — a vulnerable device may have been forgotten — so asset management is an increasingly important part of vulnerability management. and CVE-2023-20273 with a CVSS Score of 7.2,

SecureList
MARCH 13, 2024
Stalkerware is commercially available software that can be discreetly installed on smartphone devices, enabling a perpetrator to monitor an individual’s private life without their knowledge. Not unlike malware, stalkerware apps are much less frequent on iPhones than on Android devices due to the proprietary and closed nature of iOS.

SecureWorld News
AUGUST 13, 2023
It's the unauthorized use of any digital service or device that is not formally approved and supported by the IT department. Whatever the reason, shadow IT can pose a serious security risk to organizations. Shadow IT devices and applications are often not subject to the same security controls as corporate systems.

eSecurity Planet
AUGUST 9, 2021
A malicious advertising campaign originating out of Eastern Europe and operating since at least mid-June is targeting Internet of Things (IoT) devices connected to home networks, according to executives with GeoEdge, which offers ad security and quality solutions to online and mobile advertisers. An Attack by a Criminal Ring.

eSecurity Planet
OCTOBER 26, 2023
Antivirus programs and firewalls are pretty good at catching malware before it can infect devices, but occasionally malware can slip through defenses, endangering personal and financial information. We’ll go over malware removal tools and steps, and offer some tips to keep your devices from getting reinfected.

SecureList
MARCH 8, 2023
Stalkerware is a commercially available software that can be discretely installed on smartphone devices, enabling perpetrators to monitor an individual’s private life without their knowledge. Some affected users may use another cybersecurity solution on their devices, while some do not use any solution at all.
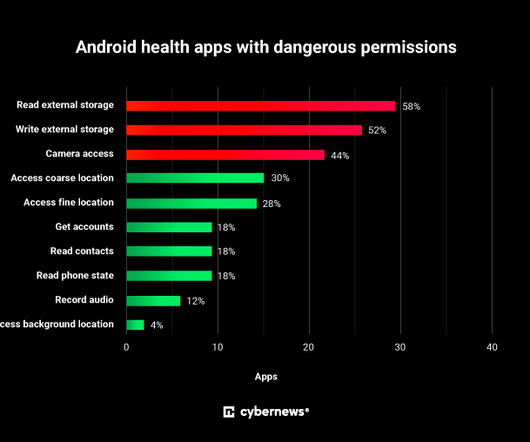
Security Affairs
SEPTEMBER 15, 2023
The Android challenge In the digital age, mobile applications have become an integral part of our lives, transforming the way we communicate, work, and entertain ourselves. Android, being the most widely used mobile operating system globally, offers developers great flexibility to create innovative and powerful applications.

SiteLock
AUGUST 27, 2021
Most small businesses typically don’t have the proper security measures in place because they don’t know they’re at risk of cyberthreats, or they don’t know how to protect themselves. This leaves a company’s network, emails, computers, and mobile devices at risk of compromise—especially its website. Website Security Tips.

Adam Levin
NOVEMBER 25, 2020
The number of people willing to use their personal devices for holiday shopping has also increased as a result of the pandemic. The number of people willing to use their personal devices for holiday shopping has also increased as a result of the pandemic. Individuals, businesses and organizations alike need to tread carefully.

BH Consulting
MAY 23, 2023
This knowledge could also help security professionals with developing or updating security awareness programmes. The regulation comes into effect from next August 25th and will affect very large platforms with more than 45 million monthly active users across the bloc. This figure corresponds to 10 per cent of the EU population.

Malwarebytes
APRIL 19, 2023
From the complaint, in relation to one support scam outfit using Nexway for payment processing: …on February 10, 2017, the Senior Key Account Manager at Nexway sent Potenzone an email titled "Nexway/TechLiveConnect: Chargeback & Cancellation rates". in November 2016, 2.6% in December 2016, and 1.5% in January 2017.
SecureList
JUNE 1, 2021
Children can now attend school remotely, and more and more adults are getting used to working from home. If the site falls into one of 14 undesirable categories, the product sends an alert to Kaspersky Security Network. For each set of 10, we took as 100% the sum of the hours spent on these apps. Website categorization.

BH Consulting
DECEMBER 14, 2021
At a time of year when many security professionals are putting the finishing touches to budget proposals, the latest Internet Organised Crime Threat Assessment (IOCTA) has outlined the key risks facing organisations in Europe. Now, a recent story shows another long-held piece of security advice that needs an update. Links we liked.

Centraleyes
FEBRUARY 25, 2024
However, critical security risks and threats inherent in cloud environments come alongside the myriad benefits. This blog aims to dissect the nuances of cloud security risks , shedding light on the challenges commonly faced when securing digital assets in the cloud. Who’s Responsible for Security in the Cloud?

CyberSecurity Insiders
SEPTEMBER 14, 2021
The high cost of remediation and the potential for reputational damage can be more than most small businesses can withstand. In honor of National Small Business Week , we’ve compiled a list of tips for small businesses to better secure their organizations from some of the more common threats they face.

ForAllSecure
FEBRUARY 23, 2023
With the release of Apple's HomeKit, we're seeing even more devices with APIs appearing in our homes. And as the Internet of Things continues to grow, the number of devices with APIs is only going to increase. All of these APIs have one thing in common: they need to be secure. Or something else entirely.

eSecurity Planet
AUGUST 22, 2023
And breaches will occur – because bad guys make a living by figuring out ways to circumvent security best practices. Prioritize Data Protection The downfall of many security strategies is that they become too general and too thinly spread. But it requires different levels of security.

Security Boulevard
JULY 29, 2021
Choosing sessions to attend this year was more difficult, with many of my favorite speakers missing from the lineup. Tom Tervoort | Principal Security Specialist, Secura. This was discovered by security researchers at Secura so it’s sure to be interesting and is at the top of my list. Tracks : Cryptography, CorpSec.
Doctor Chaos
APRIL 10, 2022
Some of that has to do with the fact that I have learned a few tips to make my travel life easier. Tip 1: Travel Underwear. Tip 2: Apple Airtags. Tip 3: Wear Comfy Clothes, but Carry Reserves. Tip 4: Air Boss. Alternate Tip 4-A: Briggs & Riley Cabin Bag. Tip 4-C: Other carry-on bag options.

eSecurity Planet
FEBRUARY 16, 2021
The internet is fraught with peril these days, but nothing strikes more fear into users and IT security pros than the threat of ransomware. Below we outline 18 industry tips for actions you can take to reduce your risk of a ransomware attack: Action. Raising awareness about ransomware is a baseline security measure.

eSecurity Planet
OCTOBER 24, 2023
One bit of good news: Even widely used email services like Gmail have gotten much better at filtering out spam and malicious email, and businesses have a range of email security tools that can help. Paranoia is a very good thing with web security in general. Here are 15 important controls and best practices for preventing malware.

Troy Hunt
DECEMBER 19, 2017
Incidentally, do note the inclusion of things like mobile device ID, IoT data and trade union memberships; many people wouldn't normally think of these as "personal data", but once you consider the potential for abuse, it makes a lot more sense.) Best of all, it's about prevention rather than cure. The cat site?

eSecurity Planet
MARCH 17, 2023
Whether you’re operating a global enterprise network or a small family business, your network’s security needs to be optimized with tools, teams, and processes to protect customer data and valuable business assets. Also read: What is Network Security?

Security Boulevard
NOVEMBER 12, 2021
Healthcare providers increasingly use mobile apps and web applications as part of the move to telemedicine. The emphasis on telehealth brings security challenges. Many healthcare-focused apps provide mobile and web facing interfaces. Fundamentally, the HIPAA Security Rule sets the stage for the safeguards that protect PHI.

eSecurity Planet
MARCH 22, 2023
Networks connect devices to each other so that users can access assets such as applications, data, or even other networks such as the internet. Network security protects and monitors the links and the communications within the network using a combination of hardware, software, and enforced policies.

eSecurity Planet
FEBRUARY 16, 2021
Malware, short for “malicious software,” is any unwanted software on your computer that, more often than not, is designed to inflict damage. Malicious mobile app. Rogue security software. As you browse the myriad of malicious software featured in this article, we offer tips for how best to defend against each type.

Malwarebytes
OCTOBER 7, 2022
After installation, the apps would ask device owners to punch in user credentials, which were then stolen. Keep your device and apps updated. Use a mobile security app. (It It won't shock you to learn that we recommend Malwarebytes Mobile Security.). When apps go stylin' and profilin'.
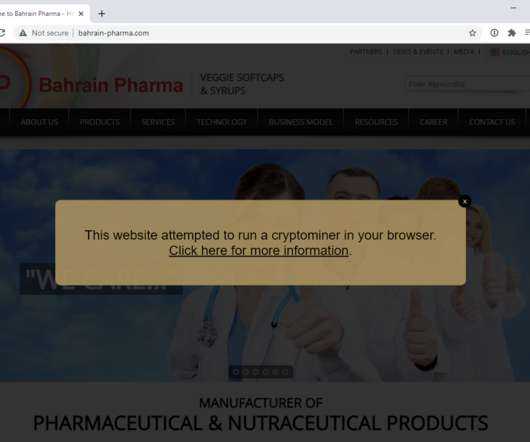
Troy Hunt
MARCH 31, 2021
And that's where things got a lot more interesting. More than 2 years after Coinhive was gone and the miner is still embedded in enough places to be serving more than 100k unique visitors per day. ATU-LX3)+AppleWebKit/537.36+(KHTML,+like+Gecko)+Chrome/88.0.4324.181+Mobile+Safari/537.36 Linux;+Android+8.0.0;+ATU-LX3)+AppleWebKit/537.36+(KHTML,+like+Gecko)+Chrome/88.0.4324.181+Mobile+Safari/537.36
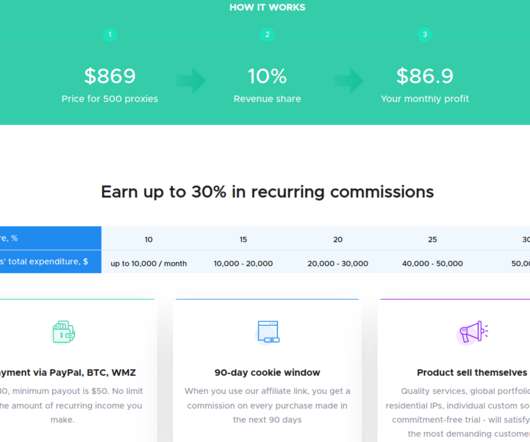
Krebs on Security
MARCH 1, 2021
A company that rents out access to more than 10 million Web browsers so that clients can hide their true Internet addresses has built its network by paying browser extension makers to quietly include its code in their creations. Singapore-based Infatica[.]io An Infatica graphic explaining the potential benefits for extension owners.

ForAllSecure
SEPTEMBER 21, 2021
What role might the security industry have in identifying or even stopping it? And what if that unease was coming from your mobile device. Some of those who bought the spyware were allegedly able to see live locations of the devices, view the targets emails, photos, web browsing history, text messages, video calls, etc.

eSecurity Planet
MARCH 9, 2023
Some vulnerability scanning tool providers recognize the key role managed IT service providers (MSPs) and managed IT security service providers ( MSSPs ) play for the many organizations with constrained IT resources.

eSecurity Planet
SEPTEMBER 19, 2022
Since many people use the same passwords or patterns when generating passwords, hackers have more and more opportunities to gain access to sensitive company data. Password manager tools allow organizations and their employees to seamlessly and securely handle login credentials. Best Password Manager Tools. Password auto-filling.
Duo's Security Blog
MARCH 24, 2023
Today: Christi Volny, a senior software engineer for the Duo Single Sign-On platform at Cisco Secure, discusses the breaking point for passwords, the tipping point for passwordless, and she trusts the math. Why does it seem to be kind of past a tipping point that a good enough solution is no longer good enough?

SecureList
MAY 31, 2021
This resulted in the deployment of a custom backdoor, named Sunburst, on the networks of more than 18,000 SolarWinds customers, including many large corporations and government bodies, in North America, Europe, the Middle East and Asia.

eSecurity Planet
JANUARY 9, 2023
Vulnerability management tools go well beyond patch management and vulnerability scanning tools by discovering security flaws in network and cloud environments and prioritizing and applying fixes. Intruder makes it easy to find and fix issues such as misconfigurations, missing patches, application bugs, and more. Heimdal Security.

eSecurity Planet
JANUARY 14, 2022
DDoS attacks may only make up a small percentage of security threats, but their consequences can be devastating. While there are some things security teams can do to lessen the impact of DDoS attacks , the growing sophistication of such attacks has sparked strong growth in the market for DDoS solutions, driven by the growth in DDoS itself.

eSecurity Planet
FEBRUARY 11, 2021
The recent boom in remote work due to the Covid-19 pandemic has further amplified the need to secure network endpoints , in which effective password management plays a big role. Password manager tools allow organizations and their employees to seamlessly and securely handle login credentials. Top Password Manager Software.

ForAllSecure
SEPTEMBER 29, 2020
Researchers claim they’ve found a flaw that allows hackers to access your device from hundreds of feet away, giving them the ability to unlock your front door, even start your car. But this is just the tip of the iceberg. Everyday we are surrounded by tiny sensors that we more or less take them for granted.

ForAllSecure
SEPTEMBER 29, 2020
Researchers claim they’ve found a flaw that allows hackers to access your device from hundreds of feet away, giving them the ability to unlock your front door, even start your car. But this is just the tip of the iceberg. Everyday we are surrounded by tiny sensors that we more or less take them for granted.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content