Report: The top 5 cybersecurity threats of 2017
Tech Republic Security
JULY 26, 2017
A report from Accenture has examined key threats that have emerged in the first half of 2017. Here's how businesses can stay safe.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 top-5-cybersecurity-threats-of-2017
top-5-cybersecurity-threats-of-2017 
Tech Republic Security
JULY 26, 2017
A report from Accenture has examined key threats that have emerged in the first half of 2017. Here's how businesses can stay safe.
eSecurity Planet
APRIL 23, 2021
Cybersecurity podcasts are an easy way to immerse yourself in the world of SecOps. Depending on your interests, you can catch up on the latest news and hear analysis from experts in the field, or you can take a deep-dive into a major cybersecurity story or concept. Top cybersecurity podcasts. 5 stars, 3.9k
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CyberSecurity Insiders
OCTOBER 10, 2021
The last update to the OWASP Top 10 Vulnerability Ranking was in late 2017. Much has changed in the cyber threat landscape since then. In September this year, the update happened as the nonprofit Open Web Application Security Project refreshed the content of the OWASP Top 10 2021 website.

eSecurity Planet
APRIL 12, 2024
12 Data Loss Prevention Best Practices 3 Real Examples of DLP Best Practices in Action How to Implement a Data Loss Prevention Strategy in 5 Steps Bottom Line: Secure Your Operations with Data Loss Prevention Best Practices When Should You Incorporate a DLP Strategy? Table of Contents Toggle When Should You Incorporate a DLP Strategy?

eSecurity Planet
FEBRUARY 15, 2022
cybersecurity agencies, which highlighted the threats in a pair of warnings issued in recent days. And the Cybersecurity and Infrastructure Security Agency (CISA) added 15 more vulnerabilities to its list of actively exploited vulnerabilities. cybersecurity advisories in recent weeks. The FBI and U.S.
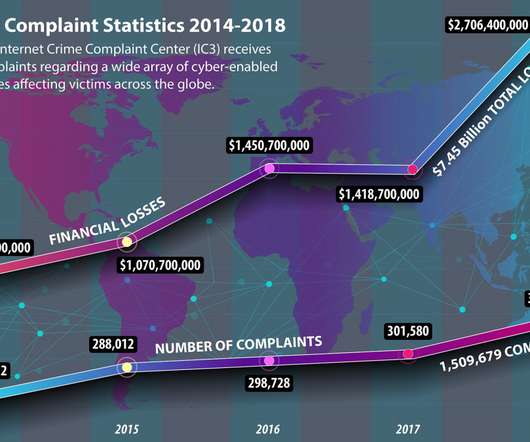
Security Affairs
JANUARY 18, 2020
According to the Cybersecurity Ventures’ cybercrime statistics 2017 cybercrime damages will amount to a staggering $6 trillion annually starting in 2021. Most financially devastating threats involved investment scams, business email compromises (BEC) , and romance fraud. 7 million in 2017 to a new high of US$13.

Jane Frankland
JANUARY 9, 2024
In recent years, data breaches and compliance failures have made organisations increasingly aware of the need for comprehensive cybersecurity solutions to detect and address threats. They include monitoring for potential threats and incidents, responding to confirmed breaches, and providing support for incident investigation processes.

eSecurity Planet
FEBRUARY 11, 2022
As data and IT infrastructure become more valuable by the day, cybersecurity risk management is increasingly important for enterprises with a steep cost for noncompliance or extensive, unaddressed vulnerabilities. What is Cybersecurity Risk Management? Read more : Best Third-Party Risk Management Tools of 2022.

SecureList
OCTOBER 7, 2022
Using LOLBINS, common legitimate pentesting tools, and fileless malware; misleading security researchers by placing false flags—these and other anti-forensic tricks often make threat attribution a matter of luck. Recently, I shared my TOP 10 list of the most mysterious APT campaigns/tools on Twitter. Project TajMahal. PuzzleMaker.

IT Security Guru
AUGUST 17, 2023
Cybersecurity is a matter of national and international security and should be prioritised as such. The 2023 Edition of the National Risk Register predicts that, in the next two years, there is a 5 to 25% chance that a devastating attack will target critical infrastructure and cause physical harm.

CyberSecurity Insiders
JANUARY 26, 2022
In November 2021, AT&T Alien Labs™ first published research on our discovery of new malware written in the open-source programming language Golang. The team named this malware “BotenaGo.” ” (Read previous article here.) In this article, Alien Labs is updating that research with new information. Background.

CyberSecurity Insiders
SEPTEMBER 9, 2021
5 to discuss leadership, teamwork, and how playing smart has led to a winning career. 5 to discuss leadership, teamwork, and how playing smart has led to a winning career. Outdated cybersecurity tools and legacy approaches stack the odds against security teams and keep them in the dark. FOSTER CITY, Calif.–( About Exabeam.

SecureWorld News
MAY 27, 2021
These violations by employees became the primary threat vector for the agency in the past year. The Agency's cybersecurity challenges are further exacerbated by the number and variety of IT devices at NASA and the sheer volume of data the Agency maintains.". Further, improper use continued to be the top attack vector type in 2020.".

eSecurity Planet
SEPTEMBER 10, 2021
CloudPassage’s 2021 AWS Cloud Security Report found that misconfiguration of cloud platforms (71 percent), exfiltration of sensitive data (59 percent), and insecure APIs (54 percent) are the top cloud security threats facing cybersecurity professionals. Top 12 best practices for cloud security.

SecureWorld News
SEPTEMBER 20, 2021
Apps and software, when not designed with proper threat modelling, can lead to bad things for a business and the consumers. The Open Web Application Software Project (OWASP) compiled data from several major cybersecurity organizations to create this list. OWASP reports top 10 web and app weaknesses.

NopSec
FEBRUARY 9, 2017
The year 2016 will be remembered for some big moments in the world of cybersecurity: the largest known distributed denial of service (DDoS) attack, a phishing attack on a United States presidential candidate’s campaign, and ransomware attacks on major healthcare organizations are just a few. The attack may have approached a volume of 1.2

eSecurity Planet
JANUARY 22, 2021
Last month’s passage of the IoT Cybersecurity Improvement Act of 2020 means all IoT devices used by government agencies will soon have to comply with strict NIST standards. Lastly, we touch on the political rationale of how the landmark IoT cybersecurity legislation came to be. And that boom in devices shows no signs of stopping.

The Last Watchdog
AUGUST 1, 2019
Just a few days before Capital One’s disclosure, Equifax rather quietly agreed to pay up to $700 million to settle consumer claims and federal and state investigations into its 2017 data breach that compromised sensitive information of more than 145 million American consumers. Arrests in network breaches are rare, indeed.

CyberSecurity Insiders
JUNE 3, 2021
Arun Vishwanath from his office in Buffalo, New York and discuss some of the recent high-profile security breaches and some of the urgent cyber security threats faced by governments and businesses. Can you tell us about the Colonial Pipeline breach and how it could have been prevented? The call was largely ignored as were the solutions.

Malwarebytes
MARCH 14, 2022
On Friday March 3, the Cybersecurity and Infrastructure Security Agency (CISA) added a whopping number of 95 new known exploited vulnerabilities to its Known Exploited Vulnerabilities Catalog. In fact, only 5 vulnerabilities were patched in 2022. Not so new. This brings me to the next thing that is remarkable. Some examples.

Security Affairs
AUGUST 7, 2018
The USA, Russia and China are TOP-3 countries in which registered users became the victims of cyberattacks. In 2017, when cryptocurrencies were gaining momentum, their record-breaking capitalization and a spike in Bitcoin’s exchange rate led to dozens of attacks on cryptocurrency services. The report «2018 Cryptocurrency Exchanges.

Security Affairs
FEBRUARY 1, 2019
Hash Sha 256:a3088d98d46a7202edeafeb744dbd822c647c72ce0d3949f895106ff3e201c9c Threat Dropper Brief invoice(7).doc Hash Sha 256:a3088d98d46a7202edeafeb744dbd822c647c72ce0d3949f895106ff3e201c9c Threat Dropper Brief invoice(7).doc Figure 5 – Deobfuscated C2’s IP. Figure 5 – Deobfuscated C2’s IP. Technical analysis.

Security Boulevard
JUNE 26, 2023
Gathering threat intelligence on prospective cyber threats across your organization’s internal and external attack surface , as well as sensitive information that may be shared across the deep and dark web is always the first step to preventing data breaches. Once a consumer’s trust has been lost, it is often impossible to restore.

eSecurity Planet
DECEMBER 17, 2021
With the adoption of cloud-based applications and services growing exponentially, especially as a result of the dramatic growth in remote work in response to the COVID-19 pandemic, more than ever organizations need to protect their data and IT systems from cloud-based threats. Top 10 CASB solutions. Jump ahead to: Broadcom. Forcepoint.

SecureList
OCTOBER 6, 2022
Now, as we predicted in last year’s forecast , many are returning to their usual ways of life, visiting stores and withdrawing cash, and the threat of PoS/ATM malware is also making a comeback: the cybercriminals are already implementing new ways to steal from banks and organizations, and the number of attacks is on the rise, too.

eSecurity Planet
FEBRUARY 16, 2021
The internet is fraught with peril these days, but nothing strikes more fear into users and IT security pros than the threat of ransomware. A ransomware attack is about as bad as a cyber attack can get. Jump to: What is ransomware? How ransomware works. Preventing ransomware. Ransomware attacks and costs. Ransomware types. What is ransomware?

eSecurity Planet
DECEMBER 3, 2021
????????Fifteen years after the launch of the microblogging social media platform, Twitter remains a dominant public forum for instant communication with individuals and organizations worldwide on a universe of topics, including #cybersecurity. Top Cybersecurity Experts to Follow on Twitter. Binni Shah | @binitamshah.

Cisco Security
SEPTEMBER 28, 2022
The stories surrounding these high-profile vulnerabilities generally carry an implied threat that the CVE in question will throw the doors wide open to attackers if not addressed immediately. In addition to this, Kenna.VI+ includes an API that brings in an additional layer of external threat intelligence, enabling further analysis.
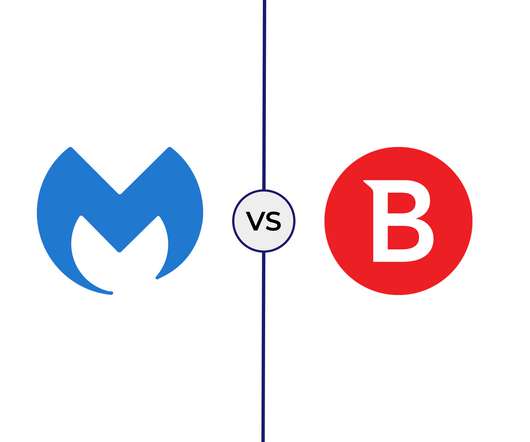
eSecurity Planet
FEBRUARY 11, 2022
Malwarebytes and Bitdefender are two of the most recognized names in the cybersecurity market for the latest antivirus software, endpoint detection and response (EDR), and endpoint protection platforms ( EPP ). 5 Devices 50 Devices 99 Devices 1 Year $58 $46 $46 2 Year $93 $73 $73 3 Year $116 $91 $91. Endpoint Detection and Response.

Digital Shadows
AUGUST 17, 2021
According to this year’s research—and this should be no surprise to the Verizon fans like us—it’s still the top method of attack for external threat actors. Going back a bit, it was also the top attack vector in 2020, 2019, 2018, 2017, 2016, and well, hopefully, you get the picture.

eSecurity Planet
SEPTEMBER 11, 2023
Here are some of the top vulnerabilities from the last week that security and IT teams should address. Here are some of the top vulnerabilities from the last week that security and IT teams should address. These vulnerabilities could be exploited by threat actors to gain control of devices if security updates are not applied.

eSecurity Planet
APRIL 6, 2023
Ransomware is the most feared cybersecurity threat and with good reason: Its ability to cripple organizations by locking their data is a threat like no other. Ransomware as a Service (RaaS) allows less technically capable hackers to launch ransomware attacks by paying to use a threat group’s ransomware.

eSecurity Planet
DECEMBER 7, 2023
This guide will provide a high level overview of encryption and how it fits into IT through the following topics: How Encryption Works To understand how encryption works, we need to understand how it fits into the broader realm of cryptology, how it processes data, common categories, top algorithms, and how encryption fits into IT security.

Pen Test
OCTOBER 10, 2023
The Surge of Double Extortion Ransomware Attack s Ransomware attacks have become an increasingly severe threat to organizations around the world. WannaCry and NotPetya ransomware worms, in 2017, illustrated how quickly ransomware could spread through networks and cause global disruption.

Security Boulevard
JUNE 15, 2023
Many espionage-focused threat groups operate stealer families for pilfering information from target networks. With the amount of visibility we have at Zscaler, we are accustomed to encountering new threats on a daily basis. The same way you do in the real world – the market becomes flooded.
SecureWorld News
JUNE 18, 2020
It was this week's bombshell cybersecurity news. Some of the most secret parts of the CIA appear to have worse cybersecurity than a typical small or medium-sized business (SMB). Senator Ron Wyden revealed that this has been known within the agency for years and well documented, yet "woefully lax" cybersecurity persists.

ForAllSecure
FEBRUARY 23, 2021
I thought I would live my life on a mountain top staring at the night skies through some massive university-sponsored telescope. To help more people to become penetration testers, Kim Crawley and Phillip L. Wylie wrote The PenTester BluePrint: Starting A Career As An Ethical Hacker. The infinite universe-- so much yet to learn and discover.

ForAllSecure
FEBRUARY 23, 2021
I thought I would live my life on a mountain top staring at the night skies through some massive university-sponsored telescope. To help more people to become penetration testers, Kim Crawley and Phillip L. Wylie wrote The PenTester BluePrint: Starting A Career As An Ethical Hacker. The infinite universe-- so much yet to learn and discover.

eSecurity Planet
FEBRUARY 16, 2021
Boost your organization’s IT literacy with ongoing cybersecurity training so they recognize the threats posed by malware attacks. Here are some common and not so common malware threats and how to defend against them. Backdoors are among the most challenging types of threats to protect against. Jump ahead: Adware.

eSecurity Planet
MARCH 30, 2023
To compare Cisco ISE against their competition, see the complete list of top network access control (NAC) solutions. Cisco built upon its legacy of networking equipment to acquire and develop other IT and cybersecurity products. Who is Cisco? It trades on the NASDAQ stock exchange under the symbol CSCO. MAC Address bypass (MAB) 802.1x

CyberSecurity Insiders
JANUARY 31, 2021
Regardless of how familiar you are with Information Security, you’ve probably come across the term ‘malware’ countless times. From accessing your business-critical resources and sensitive information to halting business operations and services, a malware infection can quickly become an organization’s worst nightmare come true. What is Malware?

Spinone
NOVEMBER 15, 2016
Information Technology research and advisory company, Gartner, presented its top predictions for the cybersecurity industry for 2017 earlier this year. So how must the cybersecurity industry adapt and grow in order to defend against this onslaught? But defense against cyber criminals is not just about increasing spending.
Spinone
JANUARY 20, 2020
The ransomware threat is huge, and it gets bigger every day. Key Information About Ransomware Ransomware is in the top-five threats in all fields and the second biggest cybersecurity threat in the retail business. The example – NotPetya cyberattack against Ukraine in 2017. But how does ransomware work?

Cisco Security
AUGUST 28, 2023
File Analysis and Teamwork in the NOC Corelight and NetWitness extracted nearly 29,000 files from the conference network stream, which were sent for analysis in Cisco Secure Malware Analytics (Threat Grid). It was humorous to see the number of Windows update files that were downloaded at this premier cybersecurity conference.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content