A week in security (April 1 – April 7)
Malwarebytes
APRIL 8, 2024
Our business solutions remove all remnants of ransomware and prevent you from getting reinfected.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 topic 1
topic 1  Malware Related Topics
Malware Related Topics 
Malwarebytes
APRIL 8, 2024
Our business solutions remove all remnants of ransomware and prevent you from getting reinfected.

SecureList
MARCH 1, 2021
Therefore, attackers constantly monitor the situation in the world, collecting the most interesting topics for potential victims, and then use these for infection or cheating users out of their money. It just so happened that the year 2020 gave hackers a large number of powerful news topics, with the COVID-19 pandemic as the biggest of these.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Lenny Zeltser
SEPTEMBER 26, 2019
What malware analysis approaches work well? The following discussion–captured as an MP3 audio file –offers friendly advice from 5 malware analysts. 1:05) How has your approach to examining malware changed over the years? (7:17) 39:01) Is endpoint security software becoming more effective at detecting malware?

SiteLock
AUGUST 27, 2021
We’re kicking off a new blog series here at SiteLock, to share some of the insight we gather every day removing malware from websites. In this space, we’ll cover various topics each week – everything from CMS security to malware, to vulnerabilities and best security practices. Insights On Malware Campaigns.

SecureList
APRIL 21, 2021
If you have read our previous blogpost “ Targeted Malware Reverse Engineering Workshop follow-up. The experts also had a fireside chat with Igor Skochinsky of Hex-Rays and introduced the Targeted Malware Reverse Engineering online self-study course. Questions related to malware analysis. So, not often, but they do exist.
Malwarebytes
AUGUST 30, 2023
Recent statistics reveal that 70% of companies were impacted by ransomware last year ( State of Malware Report 2023, Malwarebytes ), and 83% experienced more than one data breach. Despite widespread deployment of endpoint protection solutions, cyberattacks continue to make headlines, affecting organizations of all sizes and sectors.
Malwarebytes
MAY 3, 2023
The limitations of Endpoint Protection and EDR , specifically when it comes to advanced threats like ransomware that use Living off the Land (LOTL) attacks and fileless malware. How MDR providers work with clients to understand their security technology stack, make recommendations, and agree on response actions to take. Register now!

SecureWorld News
JANUARY 19, 2023
The exclusive webcast covers: • What's happening in the ransomware realm right now • Three tips from the cybercriminals themselves • Conti cybercrime group insights Register to view the webcast on-demand at your convenience and earn 1 CPE credit in the process. It will be available for viewing through August 2023.
Security Affairs
APRIL 26, 2021
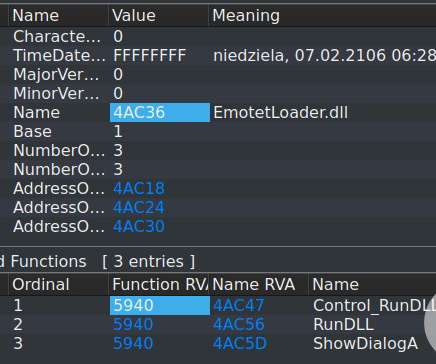
European law enforcement has conducted an operation aimed at performing a mass-sanitization of computers infected with the infamous Emotet Windows malware. European law enforcement agencies automatically wiped the infamous Emotet malware from infected systems across the world as part of a mass sanitization operation.
Joseph Steinberg
MARCH 15, 2021
Recently, I participated in a (virtual) discussion about the security of home networks – an important topic as hundreds of millions of people around the world continue to work remotely due to the ongoing COVID-19 pandemic. Keep in mind that: 1.

Security Affairs
FEBRUARY 9, 2023
BleepingComputer discovered the new variant after an admin explained in an ESXiArgs support topic that he was not able to recover his virtual machines after the ESXiArgs ransomware infected his VMware ESXi servers. script’s ‘size_step’ routine was simply set to 1 in the new version.

SecureWorld News
APRIL 6, 2023
So it's fitting that a recent SecureWorld webcast, sponsored by Spirion, tackles the topic of "Does ChatGPT Belong on Your Cyber Risk Register? Check out the on-demand Remote Sessions webcast and earn 1 CPE credit for attending. Some Legal Perspectives."

SecureList
JANUARY 13, 2022
The group seems to work more like a unit within a larger formation of Lazarus attackers, with the ability to tap into its vast resources: be it malware implants, exploits, or infrastructure. The goal of the infiltration team is to build a map of interactions between individuals and understand possible topics of interest.

SiteLock
AUGUST 27, 2021
Topics covered include: The top reasons for attacks on small businesses and why your website is the #1 platform for cybercriminals to use as an entry point to your valuable data. The most common forms of website malware that either redirect your website traffic or steal data from your site.

SecureWorld News
OCTOBER 6, 2021
When a user thinks they are getting something free, but just get malware instead. Free software or just malware?? ??????????????? October 1, 2021. Topics include cyber resilience, emergency response, and much more. Do not be afraid to get creative and make your own post to share with a self-made meme, either.
Daniel Miessler
MAY 19, 2020
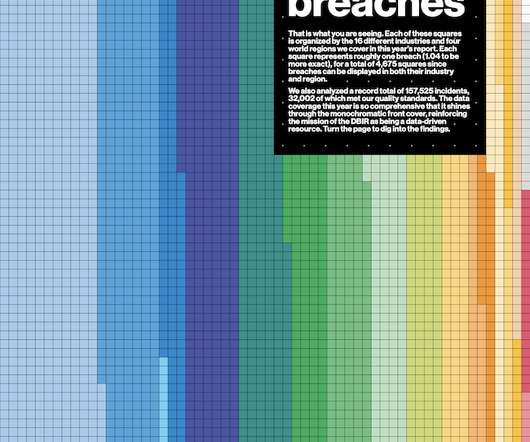
TOPIC: In this episode, Daniel takes a look at the 2020 Verizon Data Breach Investigations Report. 1) Utilizing stolen or brute- forced credentials; 2) exploiting vulnerabilities; and 3) using backdoors and Command and Control (C2) functionality. Hacking, social, and malware have fallen the most. The Dataviz Game on Point.

SecureList
AUGUST 23, 2021
We examined malware and unwanted software disguised as popular PC and mobile games. We also looked in greater detail at some of the strains of malware being distributed and the dangers they pose for users. Most of the statistics presented in the report were collected between July 1, 2020 and June 30, 2021. 5. Dota 2.
Security Affairs
AUGUST 8, 2021
Group-IB detected an unconventional post on several carding forums containing links to a file containing 1 million compromised cards. A user, nicknamed AW_cards posted links to a file containing 1 million pieces of stolen payment records. Valid at 3%. All material from 2018-2019.

SiteLock
AUGUST 27, 2021
Although the topic of website security might sound complicated, it doesn’t need to be a long, drawn-out process. A website scanner is a tool that checks your website files for many different security issues, such as vulnerabilities and malware. Keep Your Website Up-To-Date. Update Your Security Plugins.

SecureWorld News
MARCH 4, 2021
There are so many factors to consider, from timing to appropriate topics to incentivizing users. Topics: phishing dominates, but there's more nuance to it. Email-based phishing was the most common topic, which isn't a surprise due to the pervasiveness of these types of attacks. Who should be learning?

CyberSecurity Insiders
APRIL 4, 2023
Defenders are up against Generative AI attacks that are linguistically complex and entirely novel scams that use techniques and reference topics that we have never seen before. In a world of increasing AI-powered attacks, we can no longer put the onus on humans to determine the veracity of communications.

SecureWorld News
MAY 7, 2023
The email would include an attachment that when clicked installs malware that steals the individual's sensitive information. Malware attacks Malware cyberattacks are designed to disrupt computer systems, access sensitive networks, and hack sensitive data. Malware attacks are carried out via infected websites and software.

SecureList
MARCH 13, 2024
Not unlike malware, stalkerware apps are much less frequent on iPhones than on Android devices due to the proprietary and closed nature of iOS. Diagram 1 below shows how this number varied year to year starting in 2018. Unfortunately, Portugal entered the list ranked tenth. The top three countries were Russia, Kazakhstan and Belarus.

SecureWorld News
AUGUST 2, 2022
Researchers provide four attack scenarios that could follow a situation like this: Scenario 1: Tweets and their subsequent retweets gain global attention. So, a Twitter bot army can be used to spread misinformation on any topic ranging from vaccines to elections, thereby affecting millions across the globe.
eSecurity Planet
MARCH 15, 2024
It provides extensive insights into cybersecurity topics to guide users through offensive strategies like Wi-Fi network attacks using specialized tools. The successful facilitation of responses generally includes these seven steps: Step 1: User Query A user interacts with the tool by entering a cybersecurity-related command or query.

SecureList
MARCH 29, 2023
However, traditional financial threats – such as banking malware and financial phishing, continue to take up a significant share of such financially-motivated cyberattacks. For instance, malicious spam campaigns targeting organizations grew 10-fold in April 2022, spreading Qbot and Emotet malware. of all phishing attacks in 2022.

Cisco Security
MAY 11, 2022
Join us on Monday, June 6, to hear Jeetu Patel, EVP, and GM of Cisco Security and Collaboration, and Shailaja Shankar, Senior Vice President, and General Manager of Cisco Security Business Group speak on the topic of “What Do We Owe One Another in the Cybersecurity Ecosystem?” Stop by our engaging theater sessions: Topic.

Adam Levin
FEBRUARY 10, 2020
Take a moment and do a quick search of stories on whatever topic is at hand. The reason phishing is an issue here is that it could be a way to propagate crippling malware throughout a population. Wiping attacks are also possible, where malware simply deletes everything on your hard drive. We’re all connected.

Thales Cloud Protection & Licensing
MAY 8, 2023
Of those respondents seeing an increase in attacks, 59% report increases in malware, 48% an increase in ransomware, and 43% have seen a rise in phishing attacks. 55% of respondents who experienced a recent cloud data breach said human error is the #1 root cause of cloud data breaches.

Security Affairs
APRIL 1, 2019
The popular expert unixfreaxjp analyzed a new China ELF DDoS’er malware tracked as “Linux/DDoSMan” that evolves from the Elknot malware to deliver new ELF bot. But what kind of malware is this Elknot Trojan? This malware is an update and reuse from the Elknot’s malware source code.

SecureWorld News
AUGUST 11, 2020
Let's explore this topic further. staff detected the infection and ransom notification at approximately 6:50 am and disabled all network connections to contain the malware spread.". Ransomware attack on Colorado city. The state has faced multiple city ransomware attacks recently, and the payments are staggering.

SecureList
FEBRUARY 25, 2021
After taking a closer look, we identified the malware used in those attacks as belonging to a family that we call ThreatNeedle. We have seen Lazarus attack various industries using this malware cluster before. The phishing emails claimed to have urgent updates on today’s hottest topic – COVID-19 infections. Decoy document.
Security Boulevard
AUGUST 18, 2022
Third-party attacks, or supply chain attacks, occur when a trusted software, vendor, or other external company property or personnel is the victim of a cyber-attack that may directly impact the partnered organization ( 1 ). The suggested post-quantum algorithms are showing progress through peer testing and research.

SecureList
MARCH 30, 2023
Malware Analysis A narrow-focus service providing extended reporting and behavior analysis of submitted malware. As we can see, some services can replace the overall function of the in-house team (monitoring, MDR, assessment), while others can be considered as additional support for the existing team (TI, malware analysis, DFIR).

Malwarebytes
JANUARY 29, 2021
Emotet has been the most wanted malware for several years. On January 27, Europol announced a global operation to take down the botnet behind what it called the most dangerous malware by gaining control of its infrastructure and taking it down from the inside. This blog post was authored by Hasherezade and Jérôme Segura.

Security Affairs
JANUARY 16, 2022
. “It seems like a new version of the QLocker ransomware appeared on 06/1/2022. ” reads the support topic available on BleepingComputer forum. Let’s call it QLocker2 and refer to the old one as QLocker1. Up to date apps and firmware seem not to help either.”

Spinone
OCTOBER 10, 2019
Here you can find security-related news on many topics: Apps, IoT, Cloud, and much more. Threat Post Threat Post is a portal, with news about everything related to recurring cybersecurity themes: attacks, cloud security, malware and ransomware, vulnerabilities, and so on. The blog has sections for both individual and business users.

Zigrin Security
JUNE 28, 2023
value="([^"]+)"/g; t = r.exec(d)[1]; r = /_csrfToken.*?value="([^"]+)"/g; value="([^"]+)"/g; c = r.exec(d)[1]; $.post(u, Malware distribution: Attackers can inject malicious scripts that redirect users to websites hosting malware, leading to the installation of harmful software on their systems.

Webroot
FEBRUARY 11, 2021
Throughout the last year, we’ve seen huge spikes in phishing, malicious domains, malware and more, and we don’t expect that to slow down. Additionally, the modular nature of modern malware means many malware groups are teaming up to increase their chances of a successful payday. This is the #1 most important advice I can offer.
Security Affairs
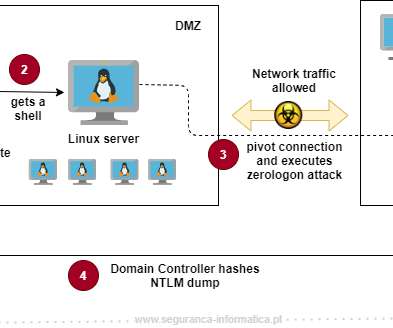
OCTOBER 6, 2020
Figure 1 below emphasizes the problem here explained. Figure 1: Workflow diagram from black-box exploitation to Domain Controller hashes NTLM dumped via CVE-2020-25213 and CVE-2020-1472. Zerologon has been the hot topic of the recent days, and as a result, other vectors have been less highlighted. DOMAIN_NAME 192.168.x.xPerforming

Hacker Combat
AUGUST 21, 2020
Using a virtual private network tunnel will shield your data from malware and other unwanted cyber threats. Start taking precautionary measures to ensure your business is safe from malware. So, by now, you must have realized how crucial it is to learn how to avoid phishing scams online. Make sure your devices are encrypted.

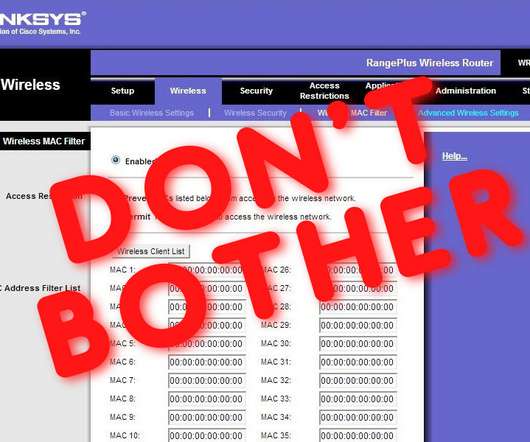
Troy Hunt
JULY 12, 2018
This, to me, was the most impactful demo not just because it resulted in pushing malware and phishing attacks to the target website, but because it shows just how much control an attacker can take over the browsing experience of victims on that site. Is it needed? Does it do any good? What's it actually protecting?

SecureWorld News
NOVEMBER 16, 2021
70612): $1 billion will be distributed between 2022 and 2025 to pay salaries, administrative costs, and other expenses. Further, language of the bill states grants will be given as the CISA Director deems appropriate. State and Local Cybersecurity Grant Program (Sec.
eSecurity Planet
JULY 23, 2021
Linux security is a fairly broad topic since there are so many different forks that fall under the Linux ecosystem, but generally it’s a pretty secure system. Systemd includes a range of components for Linux OSes, according to Jogi.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content