An Interview With the Target & Home Depot Hacker
Krebs on Security
NOVEMBER 14, 2024
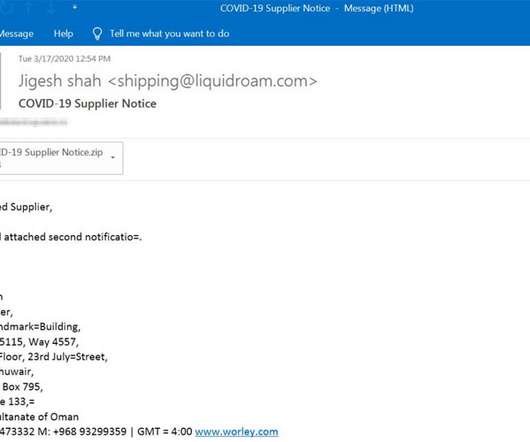
But not long after KrebsOnSecurity reported in April that Shefel/Rescator also was behind the theft of Social Security and tax information from a majority of South Carolina residents in 2012, Mr. Shefel began contacting this author with the pretense of setting the record straight on his alleged criminal hacking activities.






































Let's personalize your content