MoonBounce: the dark side of UEFI firmware
SecureList
JANUARY 20, 2022
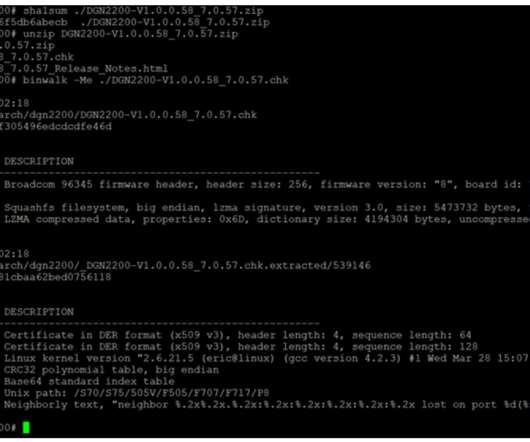
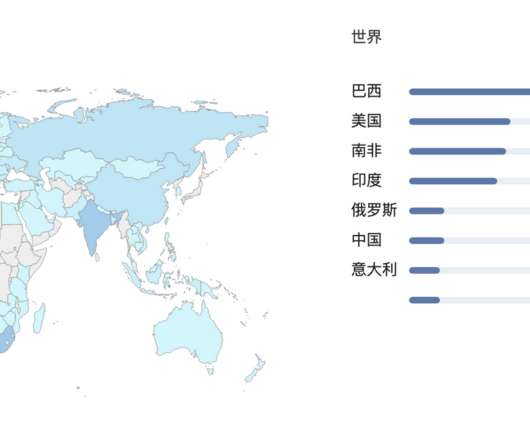
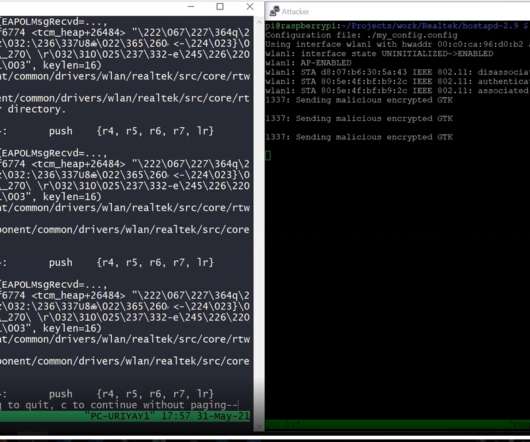
At the end of 2021, we were made aware of a UEFI firmware-level compromise through logs from our Firmware Scanner , which has been integrated into Kaspersky products since the beginning of 2019. This one is made up of implants found in the UEFI firmware within the SPI flash, a non-volatile storage external to the hard drive.







































Let's personalize your content