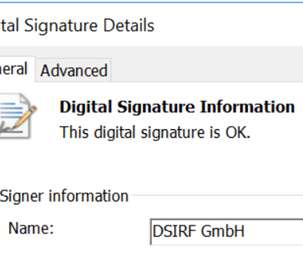
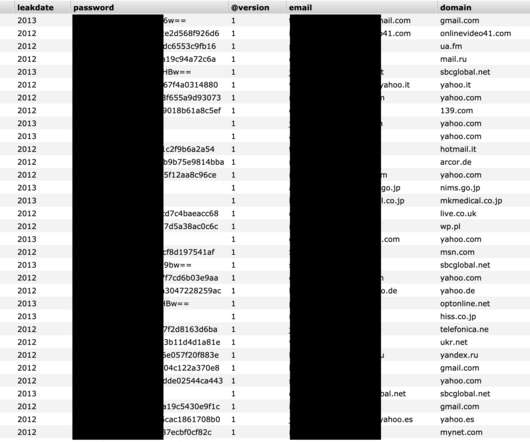
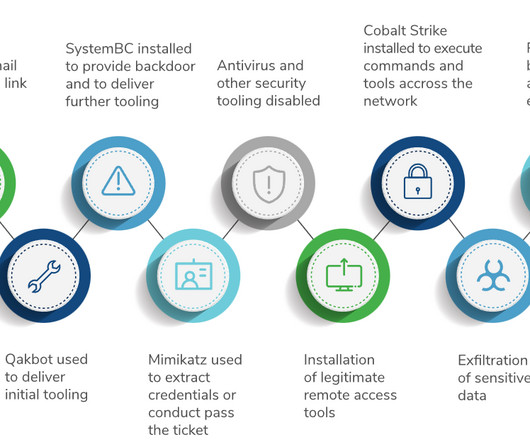
European firm DSIRF behind the attacks with Subzero surveillance malware
Security Affairs
JULY 28, 2022
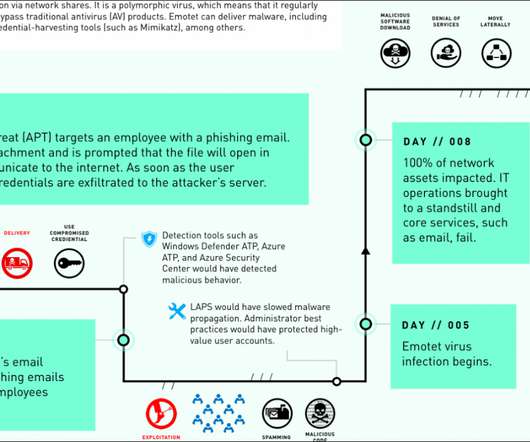
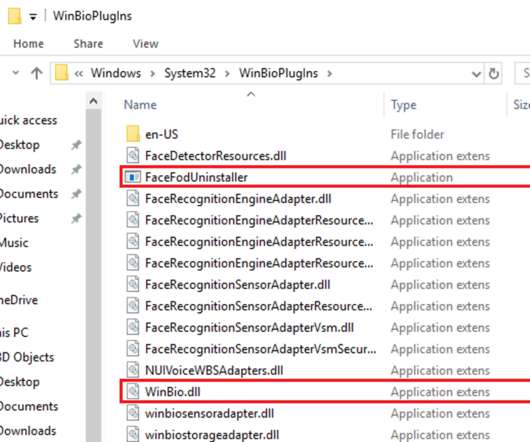
Microsoft linked a private-sector offensive actor (PSOA) to attacks using multiple zero-day exploits for its Subzero malware. The group targets entities in Europe and Central America with a surveillance tool dubbed Subzero. com Running PowerShell scripts directly from a GitHub gist created by an account associated with DSIRF.



































Let's personalize your content