How to make sure your digital transformation is secure
CyberSecurity Insiders
FEBRUARY 12, 2021
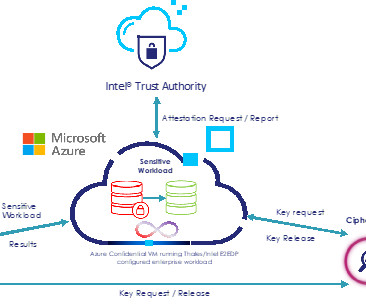
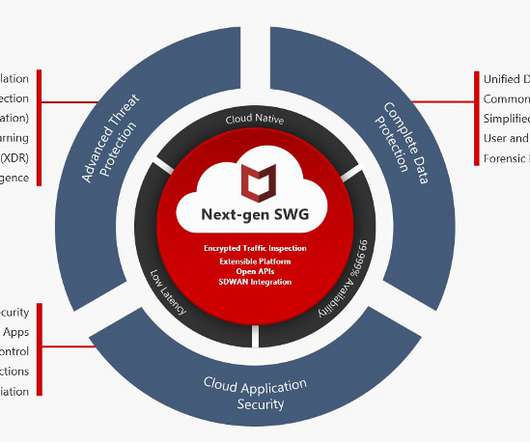
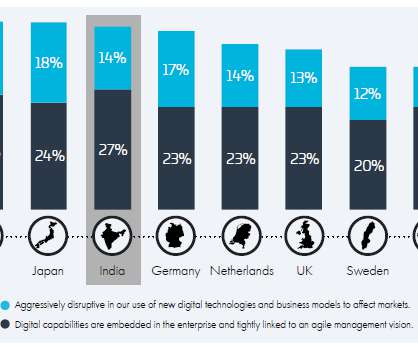
In our increasingly digital world, a greater proportion of businesses across different sectors are trying to integrate new technologies into their processes. Without this foundation, the architecture can collapse, allowing attackers to steal digital keys to break into other parts of a business’ network. Untapped potential.












































Let's personalize your content