Android devices shipped with backdoored firmware as part of the BADBOX network
Security Affairs
OCTOBER 8, 2023
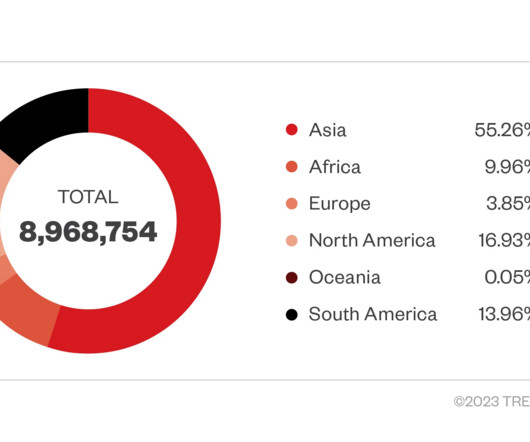
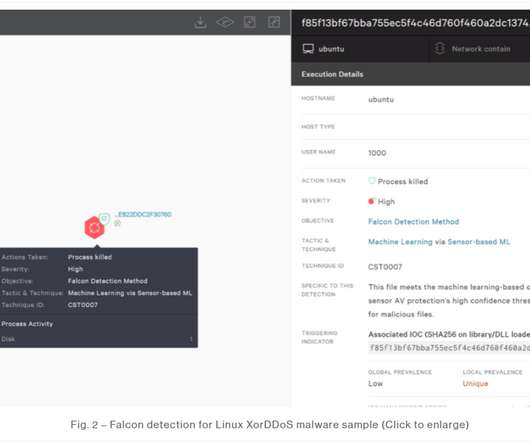
Researchers warn that more than 70,000 Android smartphones, CTV boxes, and tablets were shipped with backdoored firmware as part of BADBOX network. Cybersecurity researchers at Human Security discovered a global network of consumer products, dubbed BADBOX, with firmware backdoors installed and sold through a compromised hardware supply chain.








































Let's personalize your content