How AI/ML Can Thwart DDoS Attacks
Dark Reading
DECEMBER 20, 2022
When properly designed and trained, artificial intelligence and machine learning can help improve the accuracy of DDoS detection and mitigation.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
DECEMBER 20, 2022
When properly designed and trained, artificial intelligence and machine learning can help improve the accuracy of DDoS detection and mitigation.

CyberSecurity Insiders
JULY 8, 2021
China is once again in the news for misusing the technology of Artificial Intelligence. Information is also out that these unmanned vehicles have sophisticated devices installed in them that can launch cyber attacks such as DDoS and malware after connecting to a wireless network.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
OCTOBER 19, 2023
During the reporting period, key findings include: DDoS and ransomware rank the highest among the prime threats, with social engineering, data related threats, information manipulation, supply chain, and malware following.
Security Boulevard
OCTOBER 16, 2023
A significant component of this is the emergence of artificial intelligence and machine learning to become embedded across every aspect of the enterprise, service provider, and government systems. In cybersecurity, Cisco invested early in IPS, Firewall, VPN, and endpoint security; they produced exceptional results.
Security Affairs
MAY 14, 2023
ransom Dragon Breath APT uses double-dip DLL sideloading strategy International Press Cybercrime San Bernardino County pays $1.1-million ransom Dragon Breath APT uses double-dip DLL sideloading strategy International Press Cybercrime San Bernardino County pays $1.1-million

Threatpost
AUGUST 27, 2018
Botnets fused with artificial intelligence are decentralized and self-organized systems, capable of working together toward a common goal – attacking networks.

The Last Watchdog
JULY 25, 2022
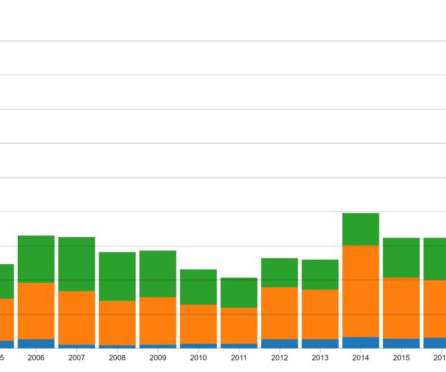
Having spiked during the COVID-19 pandemic, threats such as malware, ransomware, and DDoS attacks continue to accelerate. A10’s security research team recorded a significant spike in the number of potential DDoS weapons available for exploitation in 2021 and early 2022. Related: Apple tools abuse widespread. Key findings follow.

The Last Watchdog
OCTOBER 5, 2023
Byron: The economic impact of phishing, ransomware, business logic hacking, Business Email Compromise (BEC) and Distributed Denial of Service (DDoS) attacks continues to be devastating. Erin: What are some of the biggest cyber threats that businesses face today?

SecureList
NOVEMBER 9, 2022
If I had a magic 8-ball, I would predict that the greatest cyberthreats to businesses in 2023 will be a significant increase in foreign intelligence services conducting operations under the cover of hacktivist groups, fighting big oil, climate change, fiscal policies etc. DDOS Botnets. ris botnet which has climbed to the record.

The Last Watchdog
OCTOBER 7, 2019
Our growing fixation with leveraging artificial intelligence to extract profits from Big Data – for both constructive and criminal ends—is the order of the day. It can help companies get in a much better position to defend against, or recover from, targeted exploits, such as APT probes , DDoS attacks or ransomware , he says.

The Last Watchdog
NOVEMBER 9, 2020
On the immediate horizon, IoT systems will bring us autonomous vehicles and something called “digital twins” – virtual representations of physical objects infused with artificial intelligence. Mirai ultimately was used to carry out massive Distributed Denial of Service (DDoS) attacks.
eSecurity Planet
JANUARY 6, 2022
Third-party security, ransomware , artificial intelligence (AI) and decentralized finance (DeFi) are some of the threats you can expect to see more of this year – with the potential for far worse results than we’ve seen in the past. “A near-future event could cause a massive depopulation of internet-connected devices.

CyberSecurity Insiders
MARCH 28, 2023
Fraudsters Generate Fake ChatGPT Extension to Hijack Facebook Accounts Researchers at Guardio have flagge d up the danger of fake ChatGPT browser extensions, as users get carried away about the potential of the generative artificial intelligence (AI) platform.
eSecurity Planet
FEBRUARY 11, 2022
Machine learning (ML) and artificial intelligence (AI) have emerged as critical tools for dealing with the ever-growing volume and complexity of cybersecurity threats. DDoS (distributed denial of service) mitigation. Machines can recognize patterns to detect malware and unusual activity better than humans and classic software.

Security Boulevard
FEBRUARY 28, 2022
The Industrial Internet of Things (IIoT) puts networked sensors and intelligent devices directly on the manufacturing floor to collect data, drive artificial intelligence and do predictive analytics. Driving an industrial revolution.

Adam Levin
APRIL 8, 2019
The primary means of detecting cyber incidents for trained experts or artificial intelligence is to look for inconsistent or unexpected behavior in a system: An influx of traffic could mean a major news event, but it could also mean a DDoS attack.

eSecurity Planet
DECEMBER 8, 2023
Design robust server architecture to improve redundancy and capacity for resilience against failure or DDoS attacks. Implement rate limiting to harden against DDoS and DNS tunneling attacks. Anti-DDoS configurations can enhance server architecture DDoS to protect DNS. Firewalls should be hardened to close unneeded ports.

eSecurity Planet
APRIL 22, 2022
Artificial intelligence and machine learning , too, are being increasingly layered into these tools to predict what risks might be on the horizon so companies can stay ahead of the curve and protect themselves and their employees.

Security Boulevard
MAY 31, 2023
Seceon will again be participating with AGC Partners in its 14th Annual Boston Technology Growth Conference to be held on Thursday, November 9th. The AGC Partner Conference is a premier showcase for fast growing, predominantly private technology companies.

Security Boulevard
MAY 31, 2023
Seceon will again be participating with AGC Partners in its 14th Annual Boston Technology Growth Conference to be held on Thursday, November 9th. The AGC Partner Conference is a premier showcase for fast growing, predominantly private technology companies.

SecureWorld News
NOVEMBER 8, 2023
What's more, the rise of artificial intelligence (AI) has made social engineering methods more complex, covert, and difficult to detect. If an organization is already susceptible to a range of cyberattacks like data breaches, DDoS (distributed denial-of-service), and malware, then AI will likely provide more headaches for businesses.

eSecurity Planet
MARCH 17, 2023
With faster response times, a more centralized platform, and artificial intelligence-powered workflows, many companies select XDR tools to optimize or go beyond what their SIEM and UEBA tools can do. BAS works in the background of daily operations and is frequently automated with artificial intelligence and machine learning.

BH Consulting
SEPTEMBER 14, 2021
Access denied: large-scale attack highlights DDoS risk . How good are your defences against DDoS? BankInfoSecurity’s report took a similar tack, quoting the NetScout Atlas Security Engineering and Response Team which found over 10 million DDoS attacks launched in 2020, up from 8.5 million in 2019.

eSecurity Planet
FEBRUARY 9, 2022
In the survey, cybersecurity spending came out ahead of other hot areas such as the cloud and artificial intelligence (AI). Phishing , general malware , and Distributed Denial of Service ( DDoS ) attacks are more common. DDoS Protection. Also read: Top 8 DDoS Protection Service Providers. CrowdStrike dashboard.

Malwarebytes
APRIL 19, 2021
Source: The Verge) The use of facial recognition for surveillance, or algorithms that manipulate human behaviour, is set to be banned under proposed EU regulations on artificial intelligence. Source: BBC). Stay safe, everyone! The post A week in security (April 12 – 18) appeared first on Malwarebytes Labs.

eSecurity Planet
AUGUST 26, 2022
Whereas older solutions like antivirus, firewalls, and endpoint detection and response (EDR) have long focused on threats at the network perimeter, the intent of NDR is to monitor and act on malicious threats within organization networks using artificial intelligence (AI) and machine learning (ML) analysis. Darktrace DETECT Features.

eSecurity Planet
MARCH 14, 2023
Distributed denial of service (DDoS) attacks currently will be used more often against internet-exposed resources, but can also be used by an attacker to take down networks and internal servers. Some anti-DDoS software and other resilience capabilities will also be built into routers, firewalls, etc.

eSecurity Planet
FEBRUARY 4, 2022
WAFs have to be able to quickly filter the traffic and make decisions on whether to allow each packet, especially when it comes to attackers attempting a DDoS attack. DDoS protection Challenge tests Honeypots for bad bots. The firewall allows any traffic that falls within that ruleset, while blocking any that doesn’t.

eSecurity Planet
MARCH 22, 2023
Assisted Monitoring: At the largest scales, alerts become overwhelming and often automation and artificial intelligence (AI) will be deployed to accelerate detection of anomalies. Other security functions and operations reporting can also be found in more advanced devices.

eSecurity Planet
APRIL 23, 2021
It uses AI-powered threat detection and response to keep up with attackers who incorporate artificial intelligence and machine learning into their methods. Firepower NGFWs provide advanced malware protection, security intelligence, sandboxing, DDoS mitigation and a next-generation intrusion prevention system. SentinelOne.

eSecurity Planet
FEBRUARY 9, 2024
Older distributed denial of service (DDoS) attacks used malformed TCP requests to overwhelm servers and session filtering drops requests not associated with new or established sessions. Automatically dropping unauthorized and unwanted traffic also reduces the number of packets upon which an NGFW will need to perform deep packet inspection.

eSecurity Planet
AUGUST 11, 2023
As SASE continues to evolve and improve, the cloud-based SASE solutions will quickly deploy upgrades and enable artificial intelligence (AI) enhancement as well. Security will become centralized, integrated, and simplified and operations can improve by removing any VPN and local firewall bottlenecks.

eSecurity Planet
MAY 2, 2024
Vendor reports note huge volume of attacks on local and public infrastructure, such as: CrowdStrike: Monitored hacktivist and nation-state distributed denial of service (DDoS) attacks related to the Israli-Palestinian conflict, including against a US airport. 50,000 DDoS attacks on public domain name service (DNS) resolvers.

eSecurity Planet
JULY 5, 2021
Identity and application access, single sign-on with multi-factor authentication, and threat and DDoS protection are some of the ways Akamai cloaks and protects applications while accelerating performance. Stop attacks at the edge before they reach your apps, infrastructure, and people. Learn more about Symantec.

Spinone
MAY 8, 2020
Many organizations are starting to use artificial intelligence (AI) and machine learning (ML) to make decisions or perform intelligent analysis. Distributed Denial of Service (DDoS) attacks are another familiar type of attack that can prevent businesses from carrying out operations. A great example of this is ransomware.

Security Boulevard
FEBRUARY 1, 2023
WAAPs and their legacy WAF functionality and protection capabilities are still critical to defending APIs against a litany of pre-set attacks, including SQLi, code execution, and DDoS attacks. Our artificial intelligence (AI) and machine learning (ML) engine flagged those exploits as deviations from existing API behavioral baselines.

eSecurity Planet
APRIL 29, 2022
Firepower NGFWs provide advanced malware protection, security intelligence, sandboxing, DDoS mitigation, and a next-generation intrusion prevention system. It combines automation and artificial intelligence to ensure reliable cloud security of sensitive data and intellectual property. CASB Benefits.

eSecurity Planet
JANUARY 15, 2021
IDPS tools can detect malware , socially engineered attacks and other web-based threats, including DDoS attacks. TippingPoint solutions are provided as hardware or virtual platforms and provide real-time, vulnerability protection through Automated Vaccine Threat Intelligence. Darktrace Enterprise Immune System.

eSecurity Planet
AUGUST 13, 2021
This includes Active Directory for identity and access management, Windows Defender, Azure cloud security services such as Security Center, Key Vault, Azure DDoS Protection, Azure Information Protection and Application Gateway for protecting Web applications. Imperva (WAF, database security, threat intelligence, DDoS ).

ForAllSecure
APRIL 21, 2023
Anonymous used a variety of techniques, including Distributed Denial of Service (DDoS) attacks, to take down websites and disrupt online services. In 2016, the Mirai botnet , which was composed of compromised IoT devices, was responsible for a DDoS attack that took down large portions of the internet.

Adam Levin
DECEMBER 27, 2019
The hackers who brought you Hillary’s emails and who probably have President Trump’s tax returns are going to target operational systems with an array of tactics that include ransomware and more DDoS attacks that will snarl things up in ways we’ve not yet seen. 2020 promises to be an interesting ride.
Malwarebytes
MAY 21, 2023
ChatGPT—the much-hyped, artificial intelligence (AI) chatbot that provides human-like responses from an enormous knowledge base—has been embraced practically everywhere, from private sector businesses to K–12 classrooms. As of November 2022, people can no longer ignore the artificial elephant in the room.
Security Affairs
OCTOBER 29, 2023
F5 urges to address a critical flaw in BIG-IP Hello Alfred app exposes user data iLeakage attack exploits Safari to steal data from Apple devices Cloudflare mitigated 89 hyper-volumetric HTTP distributed DDoS attacks exceeding 100 million rps Seiko confirmed a data breach after BlackCat attack Winter Vivern APT exploited zero-day in Roundcube webmail (..)

Spinone
SEPTEMBER 3, 2018
For instance, DDOS attacks are effective because they send a barrage of requests that eventually overwhelm and take down the targeted servers. Along with securing digital transactions, blockchain technology integration within existing security protocols reduces numerous cybersecurity risks.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content