GitHub rolling out two-factor authentication to millions of users
Tech Republic Security
MARCH 9, 2023
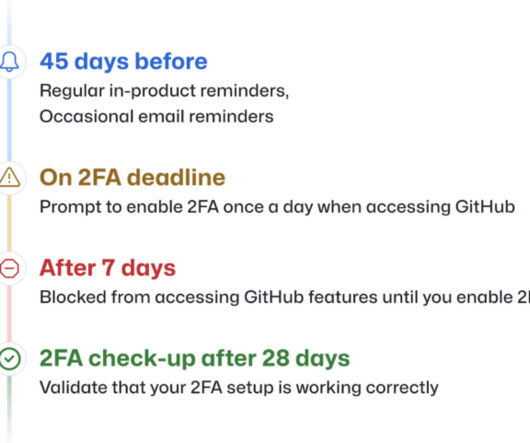
Over the next nine months, the largest internet hosting service for software development and collaboration will make all code contributors add another layer of electronic evidence to their accounts. The post GitHub rolling out two-factor authentication to millions of users appeared first on TechRepublic.








































Let's personalize your content