The ultimate guide to Cyber risk management
CyberSecurity Insiders
FEBRUARY 2, 2022
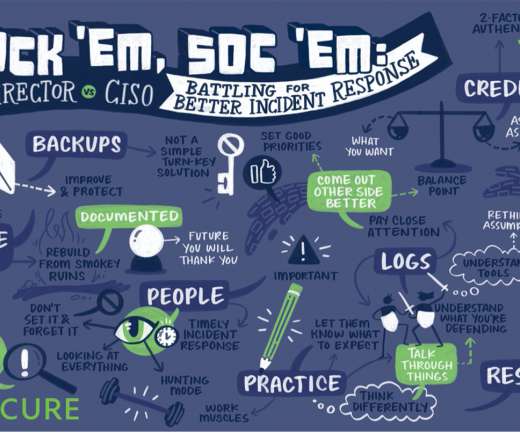
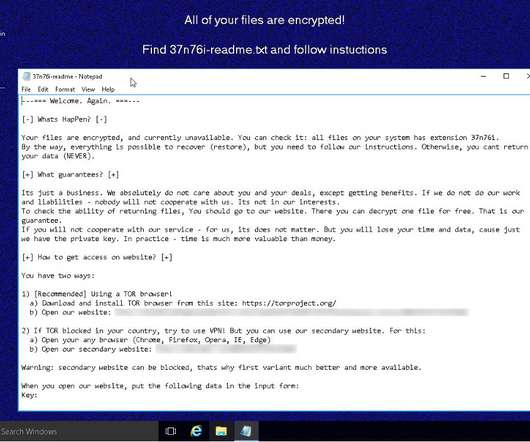
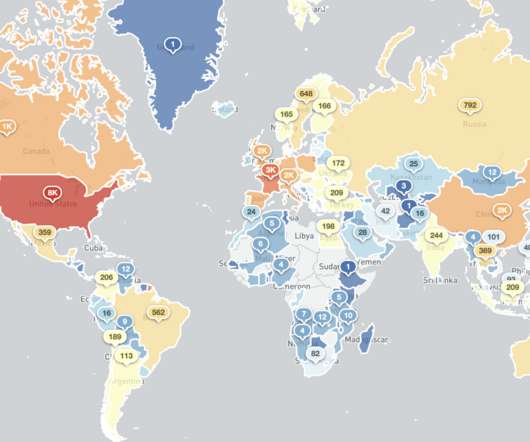
Ambitious information security experts serve as a critical part of cyber risk management. This can be achieved through the use of cyber risk management approaches. This article explores the need for security and provides an overview of cyber risk assessment. Organizations have long encountered various types of risk.





































Let's personalize your content