Colorado Privacy Act – Blog Series (Part III)
TrustArc
JUNE 30, 2021
This is part III in a four-part series on the Colorado Privacy Act.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 category ACT
category ACT  Blog Related Topics
Blog Related Topics 
TrustArc
JUNE 30, 2021
This is part III in a four-part series on the Colorado Privacy Act.

Security Boulevard
JANUARY 14, 2024
DDoS simulation tests fall into a different legal category than real DDoS attacks carried out by hackers. In the United States, for example, the Computer Fraud and Abuse Act considers a DDoS attack to be a cybercrime with serious prison time and fines.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
SEPTEMBER 8, 2022
The Federal Information Security Modernization Act of 2002 (FISMA) requires all federal agencies and their contractors to implement. The post Determining FedRAMP Risk Impact Levels and Data Security Categories appeared first on Hyperproof.

Centraleyes
FEBRUARY 1, 2024
In 2023, California remained at the forefront of the movement of states with consumer privacy laws by approving the final text of the California Privacy Rights Act regulations and inviting public comments on proposed rulemaking for cybersecurity audits, risk assessments, and automated decision-making.

Centraleyes
APRIL 22, 2024
The Federal Information Security Modernization Act (FISMA) establishes a comprehensive strategy for enhancing the cybersecurity posture of federal agencies. The idea is that the security category should reflect the most significant potential impact. Moderate potential impact from a loss of integrity.

Approachable Cyber Threats
MARCH 31, 2021
Category Awareness Risk Level. Hive Systems President and CEO Alex Nette was recently featured on the Redfin Blog. This ACT post was originally published on the Redfin Blog and is reprinted with permission of Redfin. Water damage is one of the highest insurance claim categories for homeowners. Mutual Assurance.

Security Boulevard
NOVEMBER 29, 2023
The European Union's AI Act is emerging as a cornerstone document shaping the trajectory of AI governance, with the United States’ policies and considerations soon to follow. Unquestionably, this framing has significantly influenced the initial version of the AI Act, shaping its provisions and regulatory approach.

The Last Watchdog
APRIL 19, 2022
Individuals who possess security clearances are not prohibited from traveling to foreign countries; however, there are certain acts and behaviors that may raise foreign influence and/or foreign preference concerns. The conflict in Ukraine has the potential to further alienate Russia and place Russia in a category much like North Korea.

Centraleyes
DECEMBER 4, 2023
This blog post will dive into these questions, providing all the essential details. The New Federal Data Protection Act (BDSG-new): Replacing its predecessor on May 25, 2018, it aligns German privacy laws with GDPR and the EU-Privacy Directive. But what does this mean for data subjects, and how can they enforce their privacy rights?

Identity IQ
JANUARY 17, 2023
In this blog, we will take a closer look at what privacy data is and share details about how you can keep yourself safe. For example, some countries may use a singular set of data protection regulations, whereas the United States decided to divide the data protection law into multiple categories. Identity theft also affects around 1.4

BH Consulting
AUGUST 25, 2021
This blog will look at the issue relating to employee data. The regulation has specific safeguards when processing what is known as special category personal data. As Article 9 makes clear, this category includes biometric data like fingerprints. What the GDPR says about biometrics.

The Last Watchdog
FEBRUARY 17, 2022
While there are several types of proxies, we can easily group them into two categories based on the types of internet protocols (IP) they offer. These two categories are data center and residential proxies. Proxies are servers or computers that act as intermediaries and help route your requests to target destinations.

Security Boulevard
NOVEMBER 2, 2021
As more health-focused applications go to market, application developers need to know how Health Insurance Portability and Accountability Act (HIPAA) compliance fits into their coding practices. What are HIPAA and the HITECH Act? HIPAA outlines three categories of covered entities and an additional business associate category.

Cisco Security
JANUARY 10, 2023
Using this information, last year I wrote a blog summing up the nine top of mind issues I believed will most impact CISOs as we headed into 2022. For more practical advice on this topic, I also wrote a blog on some of the challenges and opportunities within the cyber liability insurance market back in June which you can read here.
Security Affairs
JUNE 6, 2022
The payload is a PowerShell script that is Base64-encoded and acts as a downloader to retrieve a second stage PowerShell script from a remote server named “seller-notification[.]live.” Please vote for Security Affairs and Pierluigi Paganini in every category that includes them (e.g. Pierluigi Paganini.

Thales Cloud Protection & Licensing
OCTOBER 25, 2023
Vishing “While email may still be the most common mechanism for social engineering, we increasingly see attacks via social media, platforms such as WhatsApp, physical compromise, snail mail, and phone calls,” says ethical hacker FC in a blog. The best way of doing this is to pause, think about the conversation, and then act.

Malwarebytes
SEPTEMBER 30, 2021
Using this option the actors were able to let the app fetch the currently active URL that acted as a C&C server. By using the geo-specific sites and the spread across multiple categories of apps, the campaign was able to ensnare mobile users from more than 70 countries.

Approachable Cyber Threats
OCTOBER 18, 2021
Category Cybersecurity Fundamentals Risk Level. In another ACT post we talked about a process in cybersecurity that we call “vulnerability management.” You might be watching the local nightly news, or reading the Hive Systems blog , and see something that may impact you! Read more of the ACT. Let's Assess.

Thales Cloud Protection & Licensing
AUGUST 15, 2019
375 the California Consumer Privacy Act (CCPA), making California the first U.S. Last August, my colleague Ashvin Kamaraju wrote a blog shortly after this took place. A key variation with GDPR is the word “household” which adds more complexity to the implementation of the Act. state to pass its own data privacy law.
Security Affairs
JUNE 21, 2022
The scenarios acting as C2 scripts for intercepted credentials collection were also hosted on various hacked WEB-resources, leveraging domains having similar spelling to the names of existing corporations. Please vote for Security Affairs and Pierluigi Paganini in every category that includes them (e.g. To nominate, please visit:?.
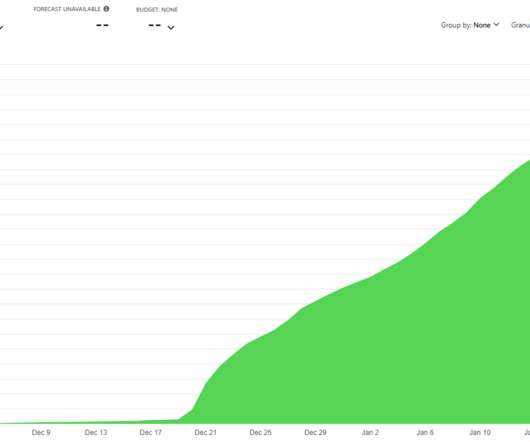
Troy Hunt
JANUARY 23, 2022
I wrote many blog posts about doing big things for small dollars and did talks all over the world about the great success I'd had with these approaches. I already needed to do better at monitoring this and I should have set up cost alerts - and acted on them - way earlier. Windows NT; Windows NT 10.0;

Duo's Security Blog
JULY 15, 2021
Part of our Administrator's Guide to Passwordless blog series See the video at the blog post. The other category of WebAuthn-compliant authenticators are roaming authenticators. This general category of attacks is known as QRLJacking. In some ways, the term “passwordless” is a misnomer.

Approachable Cyber Threats
AUGUST 10, 2022
Category Awareness, Case Study, Vulnerability. One such example of a successful nation state initiated DDoS attack used as a retaliatory tactic against a victim’s infrastructure and public services occurred in June 2022 in Lithuania, and is well documented and described by Elizabeth Montalbano in a June 2022 blog post at ThreatPost.

eSecurity Planet
JANUARY 11, 2024
This category also includes routers, switches, and Internet of Things (IoT) devices that can’t install traditional endpoint protection such as antivirus (AV) or endpoint detection and response (EDR) solutions. Sophos X-Ops illustrates how remote encryption operates beyond security tool detection. Which Unmanaged Devices Do Attackers Use?

Approachable Cyber Threats
SEPTEMBER 30, 2021
Category Cybersecurity Fundamentals Risk Level. These represent the frequencies in GHz of the radio waves carrying the Internet from your router, and they will both provide you access to your favorite blogs (ours of course!). Read more of the ACT. Some routers have two SSIDs (i.e. next to it and the other with 5.

BH Consulting
JULY 14, 2021
The agency acted to help companies that adopted new technologies during Covid-19, but failed to update their security accordingly. Our data protection consultant Tom Knierim pondered this very problem, and blogged about it in May. MORE ICS-focused but still plenty of good incident response insights from this SANS blog.

BH Consulting
SEPTEMBER 7, 2022
This blog is the first in a series where I will cover what a cyberattack involves, outline how it’s carried out, and explain how it might differ depending on your chosen technology platform. The framework divides attacks into 14 separate categories and provides in-depth descriptions of the techniques associated with each one.

Centraleyes
JANUARY 4, 2024
Act : This phase segregates identified vulnerabilities into three categories—remediate, mitigate, or accept. The acceptance category may include devices or software earmarked for replacement, requiring no immediate action. Compliance standards often dictate the specific requirements for assessment frequency.

Centraleyes
FEBRUARY 8, 2024
EDR is a category of tools designed to continuously monitor the intricate web of cyber threats on endpoints across a network. Gartner introduced this category in 2013, recognizing the imperative for tools that could provide visibility into the often overlooked endpoints within a network.

BH Consulting
JANUARY 4, 2023
Back in October, we blogged about how phishing scams are becoming more common. Remind people that we tend to put email and text messages into the ‘urgent and important’ category. So instead of replying or acting right away, pause and wait until you can verify the message on a laptop or desktop PC. Warning signs.

Cisco Security
JANUARY 22, 2021
They fit nicely into categories like external attackers or insider threats. In this blog series, the Magic of Mitigations , we’ve highlighted Mitigations as MITRE’s recommendations against attacker behavior. We make policy enforcement simple and consistent, so that you can act quickly and with confidence. And the best part?

Security Affairs
MAY 24, 2019
Those efforts fall into the business email compromise (BEC) category. That’s enough genuine information for the recipients to act without looking at the rest of the email address too closely. Think Before You Act. Barracuda’s study examined 3,000 such attacks. It found that 60% percent did not contain links.

Centraleyes
APRIL 18, 2024
Electronic Evidence Digital data stored on systems, servers, and networks, including log files, configuration settings, and other digital artifacts, encompass this category. Use well-defined categories and labels to make it simple for auditors to locate appropriate and sufficient audit evidence.

Centraleyes
DECEMBER 6, 2023
Some of the most important controls to consider will fall into these 4 categories: Technical Controls : This covers both hardware and software that is used to protect systems, networks and organizations. Controls are often categorized as administrative, technical or physical. Extensive lists can be found online.

Webroot
APRIL 15, 2021
These can be broken down into two categories: Blue Teams and Red Teams. You act as the lead generator and offer their services as an adjunct to your own. appeared first on Webroot Blog. So, what types of testing methods are there? In other words, tools are specific to the environment.).

BH Consulting
DECEMBER 14, 2020
This is the second blog in our series on the evolving international transfers landscape following the Court of Justice of the European Union [ CJEU ] decision in July 2020 which ruled the Privacy Shield data transfer mechanism invalid. The final blog in our series will explain the new standard contractual clauses and how to implement them.

Centraleyes
NOVEMBER 5, 2023
HIPAA, or the Health Insurance Portability and Accountability Act of 1996, is a federal law, whereas HITRUST is a comprehensive control framework. ” HIPAA: An Overview HIPAA, short for the Health Insurance Portability and Accountability Act, is a pivotal U.S.
Google Security
MAY 11, 2022
This blog will deep dive into the method of phishing and how it has evolved today. The simplest approach is an almost off-the-shelf "reverse proxy" which acts as a "person in the middle", forwarding the victim's inputs to the legitimate page and sending the response from the legitimate page back to the victim's browser.

Cisco Security
AUGUST 12, 2021
It is a balancing act that the NOC team enjoys creating at each conference. SECURITY CATEGORY (PHISHING). Look for a blog from Aditya on how he accomplished this with SecureX orchestration. This way, those who are delivering presentations and demos can still reach their attended target, but unaware attendees can be protected.

The Last Watchdog
JULY 27, 2020
They fear that consumer-friendly AI ethics regulations could extend out of new, prescriptive data security and privacy protections laws, such as the EU’s General Data Protection Regulation, (GDPR) or the newly minted California Consumer Privacy Act (CPPA.) AI tools are designed to put people into categories, Shashanka says.

Privacy and Cybersecurity Law
JUNE 23, 2021
The EU, in particular, has long been attentive to cybersecurity, adopting the NIS Directive in 2016 and, subsequently, Regulation 2019/881 – the Cybersecurity Act. Receive our latest blog posts by email. Each type of incident is then assigned an identification code followed by a brief description. 4] Pursuant to Article 1, para.

Centraleyes
APRIL 15, 2024
Notably, the Maryland Online Data Privacy Act incorporates essential data minimization concepts and robust civil rights safeguards from that model. These thresholds make MODPA one of the country’s most comprehensive consumer data privacy laws, aligning closely with the New Hampshire Privacy Act.

Centraleyes
FEBRUARY 5, 2024
IT security compliance acts as a shield, preventing damage to an organization’s reputation. Different categories of personal information may be subject to additional controls under various regulations. Building Trust: Maintaining clients’ or customers’ trust is paramount.

Centraleyes
FEBRUARY 15, 2024
The European Union (EU) has taken a bold step forward by introducing the EU AI Act to govern the development and use of AI technologies within its borders. Let’s explore the multifaceted impact of the EU AI Act on compliance.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content