Smooth Cybercriminals: Google Warns of Iran-Backed APT Hackers
SecureWorld News
OCTOBER 19, 2021
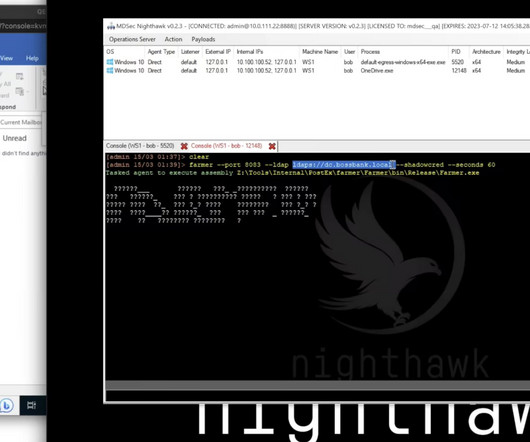
One notorious hacking group from Iran uses particularly dirty schemes to fleece users, according to Google's Threat Analysis Group (TAG). According to Google’s TAG blog, APT35 have been active since at least 2017, including attacks on the 2020 U.S. Read Google's official TAG blog to learn more about the technical details.






















Let's personalize your content