BrandPost: What is a Reflection/Amplification DDoS Attack?
CSO Magazine
AUGUST 16, 2021
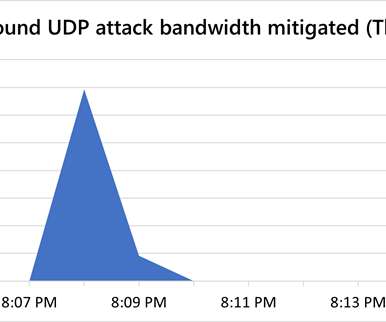
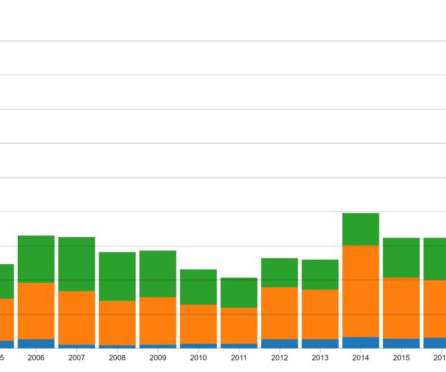
The COVID-19 pandemic has caused many organizations to accelerate digital transformation efforts in response to an exploding need for remote connectivity. In particular, distributed denial-of-service (DDoS) attack s have risen dramatically.















































Let's personalize your content