IoT Unravelled Part 3: Security
Troy Hunt
NOVEMBER 25, 2020
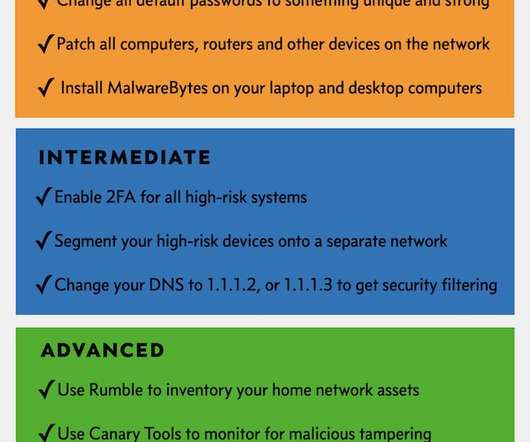
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. As with the rest of the IoT landscape, there's a lot of scope for improvement here and also just like the other IoT posts, it gets very complex for normal people very quickly.












































Let's personalize your content