Agent Tesla includes new password-stealing capabilities from browsers and VPNs
Security Affairs
AUGUST 12, 2020
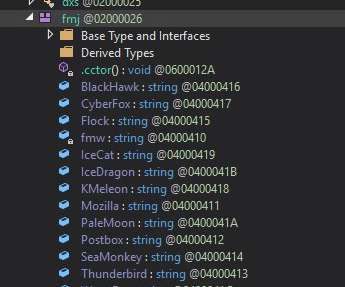
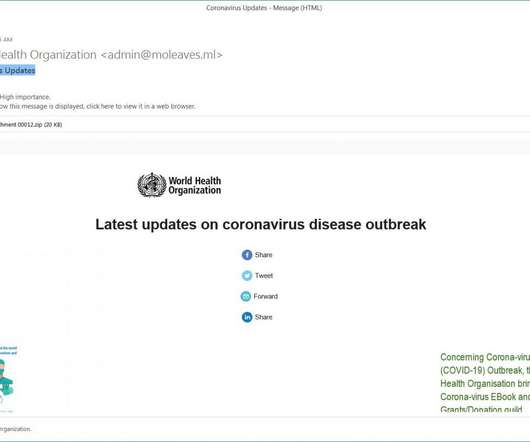
Agent Tesla is a spyware that is used to spy on the victims by collecting keystrokes, system clipboard, screenshots, and credentials from the infected system. To do this, the spyware creates different threads and timer functions in the main function. ” concludes the report that also includes indicators of compromise (IoCs).










































Let's personalize your content