Apple Guidance on Intimate Partner Surveillance
Adam Shostack
MAY 6, 2021
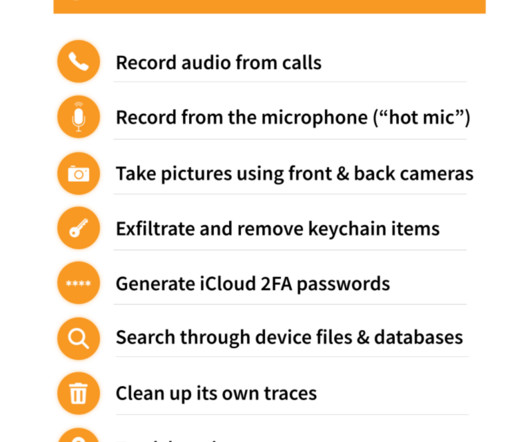
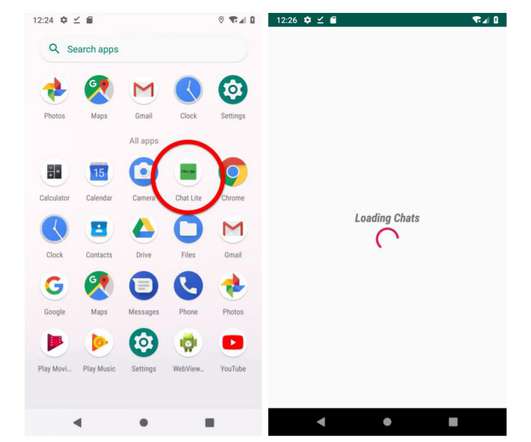
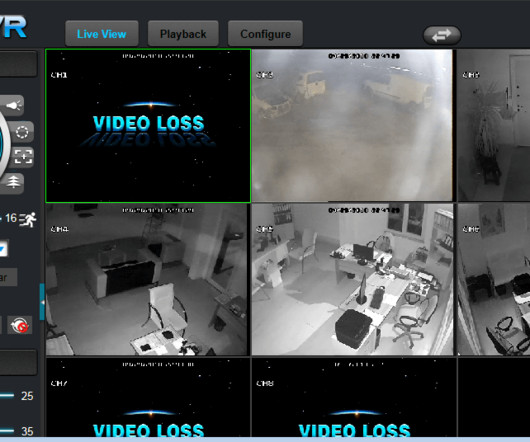
The document includes checklists, which are available separately: If you want to see if anyone else has access to your device or accounts. Defending against attackers who are both authorized and “interface-bound” is a weird problem for information security, as traditionally defined.




































Let's personalize your content