Experts spotted a variant of the Agenda Ransomware written in Rust
Security Affairs
DECEMBER 19, 2022
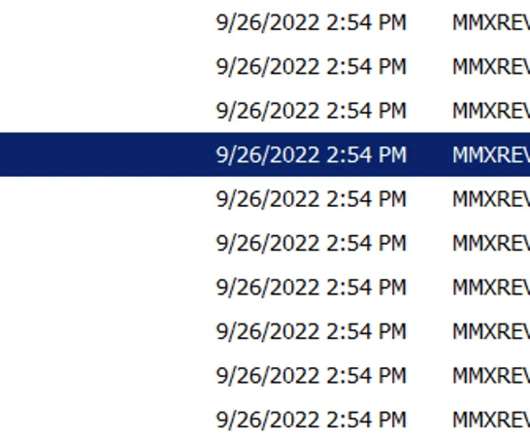
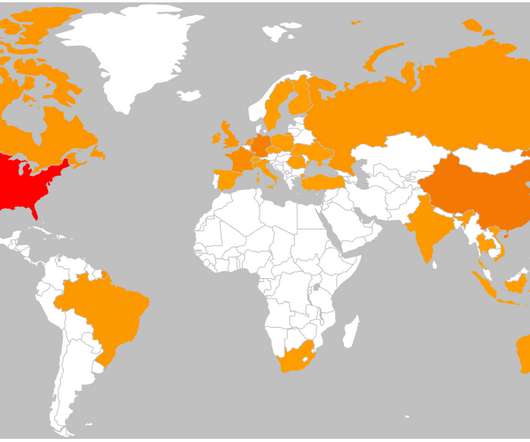
The main reasons to rewrite malware in Rust is to have lower AV detection rates, compared to malware written in most common languages, and to target multiple architectures. The Qilin ransomware-as-a-service (RaaS) group uses a double-extortion model, with most of the victims in the manufacturing and IT industries. AGENDA.THIAFBB.”








































Let's personalize your content