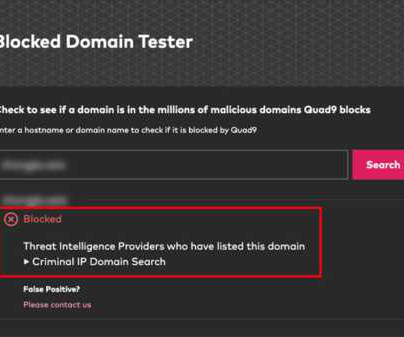
HOW DO PROVIDERS IMPLEMENT INTERNET BLOCKING IN BELARUS?
Security Affairs
SEPTEMBER 23, 2020
Researchers at Qurium Media Foundation analyzed the blocking implemented by four different operators in Belarus. The Internet was shutdown several days and more than 80 websites, most of them news and political sites, were blocked. Qurium forensics report: Internet blocking in Belarus. SecurityAffairs – hacking, Internet).








































Let's personalize your content