Facebook Trains Its AI on Your Data. Opting Out May Be Futile
WIRED Threat Level
SEPTEMBER 7, 2023
Here's how to request that your personal information not be used to train Meta's AI model. ";Request" is the operative word here.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 quote-request
quote-request 
WIRED Threat Level
SEPTEMBER 7, 2023
Here's how to request that your personal information not be used to train Meta's AI model. ";Request" is the operative word here.

Thales Cloud Protection & Licensing
APRIL 22, 2024
This is significant because advanced bot traffic poses a substantial risk even at low volumes, as advanced bad bots can achieve their goals with fewer requests than simpler bad bots and are much more persistent in staying on their designated target. of the sector's bad bot traffic comes from advanced bots, compared to gaming's 45.9%.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
AUGUST 30, 2023
A request for proposal is a common method for soliciting vendor quotes and answers about potential product or service offerings. They specifically intend to gather details involving implementation, operations and maintenance.
Krebs on Security
MARCH 20, 2024
Gaskell has been quoted in multiple “articles” about random subjects, such as this article at HRDailyAdvisor about the pros and cons of joining a company-led fantasy football team. Also quoted in this article is Sally Stevens , who is cited as HR Manager at FastPeopleSearch[.]io. Requests for comment were sent to H.I.G.

Krebs on Security
MAY 22, 2023
“This was three hours non-stop, 200,000 to 400,000 requests per second,” Chaput said of the DDoS. ” Chaput said a review of their logs indicates many of the newly registered Mastodon spam accounts were registered using the same 0auth credentials, and that a domain common to those credentials was quot[.]pw.

Hot for Security
FEBRUARY 24, 2021
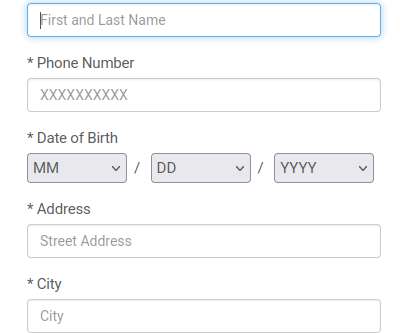
The New York Department of Financial Services (NYDFS) has issued an alert to instant-quote websites, particularly car insurers, warning of a growing campaign to steal nonpublic information (NPI). On the Auto Quote Websites, the criminals entered valid name, any date of birth and any address information into the required fields.

Krebs on Security
FEBRUARY 9, 2024
” The company has not yet responded to requests for information about exactly when those overly permissive user rights were introduced. ET: An earlier version of this story quoted George as saying he was able to see support information for the U.S. Update, 11:01 a.m. Department of Defense.

Security Boulevard
DECEMBER 9, 2022
As part of processing a response ping has to reconstruct the IP header, the ICMP header and if present a "quoted packet," which represents the packet that generated an ICMP error. The quoted packet again has an IP header and an ICMP header. Ping reads raw IP packets from the network to process responses in the pr_pack() function.

Security Affairs
OCTOBER 17, 2022
. “”Here, not only the website of the presidency is under attack, the object of the attack is the entire Bulgarian state as part of the European family,” said Ivan Geshev, quoted by BTA. They would request his extradition, but the Russian government will never provide support to the request of the Bulgarian authorities.
Security Affairs
AUGUST 11, 2020
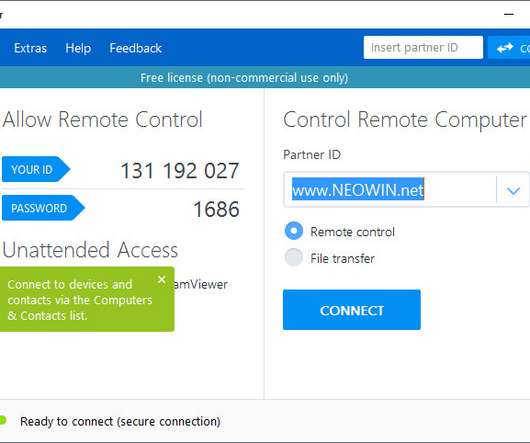
The vulnerability was discovered by the researcher Jeffrey Hofmann from Praetorian, it resides in the way TeamViewer quotes its custom URI handlers. The expert discovered that the issue could allow an attacker to force the software to relay an NTLM authentication request to the attacker’s system. for the Windows platform.

Kali Linux
DECEMBER 4, 2023
It is responsible for redirecting every request to its nearest mirror, based on a few factors such as geographic location, mirror speed, and mirror “freshness” Since Kali was launched back in March 2013, until November 2023 we had been using MirrorBrain. "; VERSION_ID="2023.4"
Krebs on Security
NOVEMBER 4, 2021
com — from a desktop web browser redirects the visitor to a harmless page with ads for car insurance quotes. Clicking “Schedule new delivery” brings up a page that requests your name, address, phone number and date of birth. .” Attempting to visit the domain in the phishing link — o001cfedeex[.]com

Kali Linux
NOVEMBER 27, 2022
bin/sh set -e PREREQ="" prereqs() { echo "${PREREQ}" } case "${1}" in prereqs) prereqs exit 0 ;; esac. bin/sh set -e PREREQ="" prereqs() { echo "${PREREQ}" } case "${1}" in prereqs) prereqs exit 0 ;; esac.
Troy Hunt
MARCH 10, 2021
Because it's free, works well and does something genuinely useful, it's become quite popular: Now up to 909M requests to @haveibeenpwned 's Pwned Passwords in the last month. Equally, Home Assistant sends outbound requests all the time, it's how you know when there's update! How long until it hits the big "1B"? ??

Malwarebytes
MARCH 5, 2022
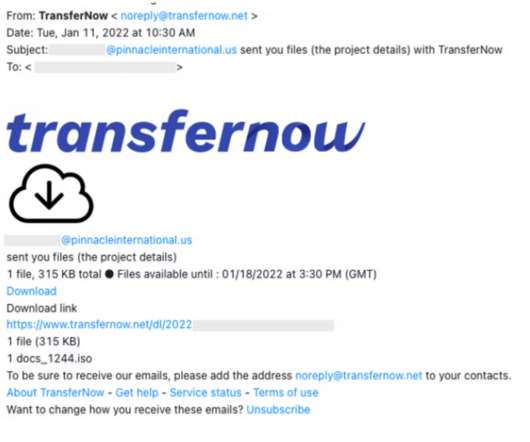
We request you to furnish your best, complete, exclusive and competitive techno-commercial offer to our esteemed company for the supply of below mentioned item(s) on or before 10-March-2022. Estimated Weight / Volume or Dimensions of the quoted item(s) / Final Package. It read: Dear Sir, Warm Greetings From Saudi Aramco.

SecureWorld News
DECEMBER 27, 2022
Cyber is the risk to watch, according to a Financial Times article in which insurer Zurich's top executive is quoted. In September, Lloyd’s of London defended a move to limit systemic risk from cyber attacks by requesting that insurance policies written in the market have an exemption for state-backed attacks.". 26 article.

Krebs on Security
MARCH 16, 2021
An expert on SIM-swapping attacks who’s been quoted quite a bit on this blog , Nixon said she also had Lucky225 test his interception tricks on her mobile phone, only to watch her incoming SMS messages show up on his burner phone. Allison Nixon is chief research officer at Unit221B , a New York City-based cyber investigations firm.
Security Affairs
OCTOBER 1, 2022
The first flaw, tracked as CVE-2022-41040, is a Server-Side Request Forgery (SSRF) issue. GTSC recommends adding a rule to block requests with indicators of attacks through the URL Rewrite Rule module on IIS server. Select Request Blocking and click OK. Powershell.*” (excluding quotes) and click OK. Select Autodiscover.
eSecurity Planet
APRIL 14, 2023
Pricing Radware doesn’t display its pricing; you can request a quote through their contact page. Pricing Cloudflare doesn’t display its pricing; you can request a quote based on what you need through their pricing page. Limited customization options for smaller businesses.

Security Affairs
MARCH 12, 2024
After the first contact via instant messaging channels, further documents are then requested and a quote is provided.
Security Affairs
MARCH 12, 2022
In these initial contact form submissions, the attacker posed as an employee at a Canadian luxury construction company looking for a quote for a product provided by the target.” . “Rather than directly sending a phishing email, the attacker in these cases initiated a conversation through an organization’s website contact form.

Security Affairs
OCTOBER 4, 2022
The first flaw, tracked as CVE-2022-41040, is a Server-Side Request Forgery (SSRF) issue. Select Request Blocking and click OK. Powershell.*” (excluding quotes) and click OK. The second vulnerability, tracked as CVE-2022-41082, allows remote code execution (RCE) when PowerShell is accessible to the attacker. Select Autodiscover.

Security Affairs
JANUARY 19, 2019
A bug in Microsoft partner portal ‘exposes ‘ support requests to all partners, fortunately, no customer data was exposed. The Register in exclusive reported that Microsoft partner portal ‘exposed ‘every’ support request filed worldwide.’ Stuart Crane of IT biz Everon told The Register.

SecureWorld News
MAY 28, 2020
Compulife and NAAIP are direct competitors in a niche industry: they both generate life insurance quotes for brokers who sell insurance. The concept is simple; a hacker requests information from a server using ordinary HTTP commands similar to those that a legitimate client program of the server might employ in the ordinary course.

eSecurity Planet
OCTOBER 1, 2022
A day after GTSC published its blog post, Microsoft released customer guidance on how to mitigate the vulnerabilities, which affect Microsoft Exchange Server 2013, 2016 and 2019, and are identified as the Server-Side Request Forgery (SSRF) vulnerability CVE-2022-41040 and the RCE flaw CVE-2022-41082. autodiscover.json.*@.*Powershell.*

eSecurity Planet
FEBRUARY 21, 2024
Your teams should also know who’s responsible for the request and upkeep of each rule. Additionally, confirm whether the owners of that process have shared any relevant documentation with new team members, and ensure that everyone knows how to submit a change request or access the documentation.
Malwarebytes
JANUARY 11, 2023
On Monday, the US Supreme Court denied the NSO Group's petition for a writ of certiorari , a request to the high court to review its case, signaling that Meta's WhatsApp can go ahead with its case against the Israeli-based company behind the Pegasus spyware. The court didn't explain why it refused to hear the NSO's appeal.

Krebs on Security
FEBRUARY 14, 2020
The IRS official who contacted me was not authorized to be quoted in the media (and indeed did not initially realize he was speaking to a member of the press when he called). Requests for this information from the Justice Department office that prosecuted the case — the U.S.

eSecurity Planet
FEBRUARY 26, 2021
This information is then analyzed to determine if the client request is from a human user or a bot. . Kasada uses a unique mitigative method that scales the difficulty of accessing web applications based on a growing number of requests. You can request a demo or contact the company for a quote. Kasada plans.

Malwarebytes
APRIL 19, 2022
Quoting your way to donation fraud. Unfortunately, we’re seeing scammers try to capitalise on these activities. A similar tactic is being used here.

Krebs on Security
JUNE 18, 2020
A follow-up story that same month examined the work of a cybercrime gang that was hacking into HR departments at healthcare organizations across the country and filing fraudulent tax refund requests with the IRS on employees of those victim firms.

Malwarebytes
JULY 4, 2023
Schneier quotes a Bloomberg article which highlights a few cases where serious crimes and accidents were the reason for law enforcement to request camera recordings from self-driving fleets such as Waymo and Cruise. You could be one of those objects without realizing it.

eSecurity Planet
FEBRUARY 26, 2021
This information is then analyzed to determine if the client request is from a human user or a bot. . Kasada uses a unique mitigative method that scales the difficulty of accessing web applications based on a growing number of requests. You can request a demo or contact the company for a quote. Kasada plans.
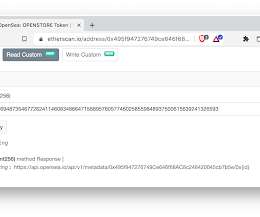
Security Boulevard
DECEMBER 7, 2021
The URL points to OpenSea, which is known to remove artwork from its site (such as in response to DMCA takedown requests). Instead of standing outside the story, simply quoting sources, they insert themselves into the story, becoming advocates rather than reporters. Instead of selling an NFT of the artwork, it's just an NFT of a URL.

Krebs on Security
MAY 3, 2019
Bessemer further alleges Fiserv’s systems had no checks in place to prevent automated attacks that might let thieves rapidly guess the last four digits of the customer’s SSN — such as limiting the number of times a user can submit a login request, or imposing a waiting period after a certain number of failed login attempts.
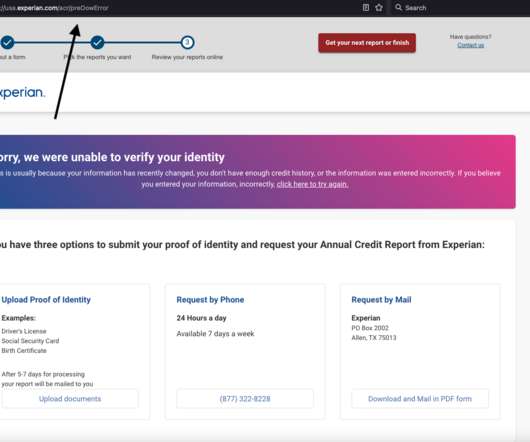
Krebs on Security
JANUARY 9, 2023
Experian said I had three options for a free credit report at this point: Mail a request along with identity documents, call a phone number for Experian, or upload proof of identity via the website. 23 notification, but the company has so far ignored multiple requests for comment or clarification. ” Sen.

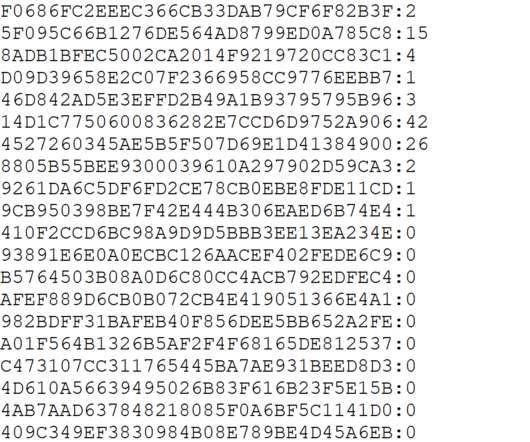
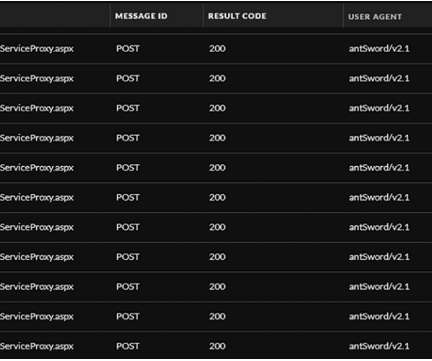
SecureList
JUNE 30, 2022
Developed in C++, SessionManager is a malicious native-code IIS module whose aim is to be loaded by some IIS applications, to process legitimate HTTP requests that are continuously sent to the server. Malicious IIS module processing requests.

Krebs on Security
OCTOBER 28, 2020
Larsson quotes Gunnebo CEO Stefan Syrén saying the company never considered paying the ransom the attackers demanded in exchange for not publishing its internal documents. What’s more, Syrén seemed to downplay the severity of the exposure. ” It remains unclear whether the stolen RDP credentials were a factor in this incident.
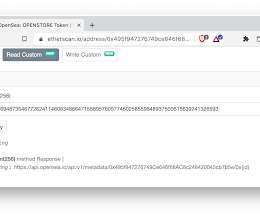
Errata Security
DECEMBER 7, 2021
The URL points to OpenSea, which is known to remove artwork from its site (such as in response to DMCA takedown requests). Instead of standing outside the story, simply quoting sources, they insert themselves into the story, becoming advocates rather than reporters. Instead of selling an NFT of the artwork, it's just an NFT of a URL.

ForAllSecure
APRIL 20, 2021
Across ForAllSecure’s community engagements, a consistent request we’ve received is for more educational material and general resources around fuzz testing. Quotes and advice from product security veterans. The goal was to help the product security industry feel connected during a time of social distancing.

ForAllSecure
APRIL 20, 2021
Across ForAllSecure’s community engagements, a consistent request we’ve received is for more educational material and general resources around fuzz testing. Quotes and advice from product security veterans. The goal was to help the product security industry feel connected during a time of social distancing.

Krebs on Security
NOVEMBER 20, 2019
That 2014 story declined to quote Rasbora by name because he was a minor then, but his father seemed alarmed enough about my inquiry that he insisted his son speak with me about the matter. His dad hung up on me when I called Wednesday evening requesting comment. 13, 2014. “I I also have [a] major concern what my 15 yo son [is] doing.
Kali Linux
MAY 25, 2015
For the latest information, please see our documentation on Docker Last week we received an email from a fellow penetration tester, requesting official Kali Linux Docker images that he could use for his work. "; Have fun with your Kali Docker images! We bootstrapped a minimal Kali Linux 1.1.0a kali-root [link]./kali-debootstrap

SiteLock
AUGUST 27, 2021
In a DDoS attack, cybercriminals use hacked networks to flood internet servers with traffic, sending more requests than the server can handle. This includes overwhelming a website with “fake” requests in an attempt to make the site unavailable. Get a quote for automatic mitigation for sophisticated DDoS attacks today.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content