The UK’s GPS Tagging of Migrants Has Been Ruled Illegal
WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag regulation
tag regulation 
WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.

The Last Watchdog
JANUARY 13, 2022
Commodity Futures Trading Commission (CFTC) fine against JPMorgan sent shockwaves through financial and other regulated customer-facing industries. While the price tag of these violations was shocking, the compliance failure was not. Related: Why third-party risks are on the rise. These views were echoed in a CFTC release as well.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JUNE 23, 2023
With Dasera, organizations can unlock the full potential of their data while maintaining compliance with industry regulations. With “Ski Lift,” Snowflake customers can gain a panoramic view of their Snowflake environment while scaling their data security and governance controls.
CyberSecurity Insiders
FEBRUARY 9, 2021
These categories of sensitive information are protected by regulations such as the GDPR, CCPA, HIPAA, and PCI DSS. It should cover both structured and unstructured data, tagging it based on its level of sensitivity and making it easier to find, track, and safeguard. Identify & assess compliance obligations.
Thales Cloud Protection & Licensing
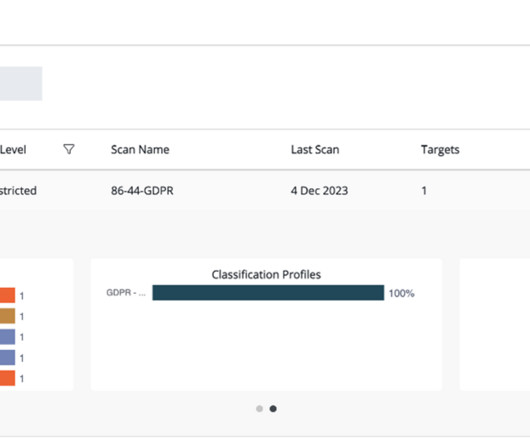
DECEMBER 11, 2023
Traditional approaches to data classification use manual tagging which is labor-intensive, error-prone, and not easily scalable. Navigating Diverse Data Repositories for Visibility Data discovery is the first step for organizations looking to comply with data protection regulations worldwide.

BH Consulting
OCTOBER 11, 2022
This makes them subject to the EU General Data Protection Regulation (GDPR). Recital 30 of the GDPR outlines how a person may be associated with online identifiers their devices and apps provide, such as IP addresses, cookie identifiers and identification tags. This legislation is separate to, but complements, the GDPR.

Malwarebytes
FEBRUARY 21, 2022
The suit contains arguments that Facebook’s now-defunct photo-tagging feature illegally collected data about Texan people’s faces, including those who are non-Facebook users but were tagged by someone who is, without asking for consent. Paxton filed the lawsuit on Monday in the state’s Harrison County District Court.

Malwarebytes
SEPTEMBER 28, 2022
We will carefully consider any representations from TikTok before taking a final decision” In other words: all of these claims and statements come with a rather large “allegedly” tag applied, and TikTok will make a response to these concerns before anything else happens of a legal nature.

The Last Watchdog
OCTOBER 24, 2022
Data discovery technologies can scan data stores and label sensitive and regulated data by purpose and type. Make sure to use common, understandable labels and data value tags for your data. Inventorying sensitive data is a crucial process in protecting your business from data breaches. Use a corporate VPN.

Security Boulevard
MAY 24, 2021
tag=Data Security'>Data Security</a> <a href='/blog?tag=Data tag=Data Breach'>Data Breach</a> <a href='/blog?tag=Information More Regulation, More Data Breaches. The good news is that there is more regulation to govern data, requiring organizations to protect it from unauthorized access.

The Last Watchdog
NOVEMBER 19, 2018
Many of these photos are tagged with the identity of the people in them. Because the technical winds are strongly behind this trend, the only way to limit it will be through legislation and regulation. This kind of Orwellian scenario is already developing in China. This kind of technology would have many applications.
Malwarebytes
JUNE 29, 2022
Google’s Threat Analysis Group (TAG) has revealed a sophisticated spyware activity involving ISPs (internet service providers) aiding in downloading powerful commercial spyware onto users’ mobile devices. The spyware, dubbed Hermit, is reported to have government clients much like Pegasus. Italian vendor RCS Labs developed Hermit.
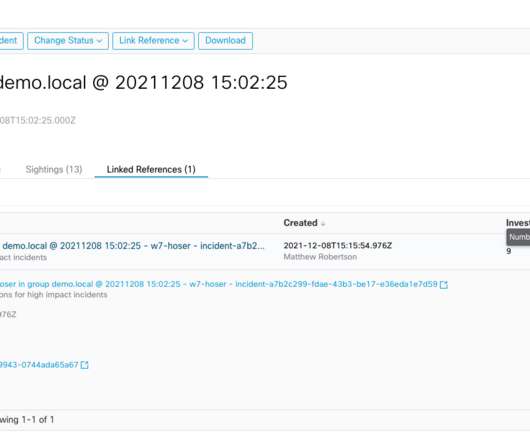
Cisco Security
DECEMBER 15, 2021
Applications can be forbidden for numerous reasons, from internal policy to government regulations, but those custom detections can be the most informing and actionable to a security operations team. High – generic malicious behaviors and generic malware, not attributed to a particular family.
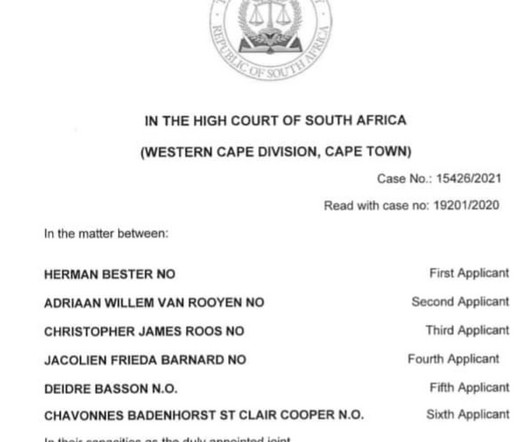
Security Affairs
AUGUST 1, 2022
Encevo registered a complaint with the Police of the Grand Duchy and of course notified the CNPD (National Commission for Data Protection), the ILR (Luxembourg Institute of Regulation) and the competent ministries. It seems that some of the stolen files are still under indexing, but majority is already available for quick navigation.

eSecurity Planet
NOVEMBER 2, 2023
Enter the tagged VLAN and the largest debate surrounding VLANs: Is it better to work with a tagged or an untagged VLAN setup? Tagged VLANs are best for larger organizations that need stricter traffic and security controls over more complex, higher volume, and different types of network traffic. Also read: What is a VLAN?

Webroot
JULY 8, 2021
These are some of those affects inflating the price tag of an attack, which we call The Hidden Costs of Ransomware. They extend to fines for breaches of compliance regulation, the rising costs of cybersecurity insurance and a host of other unforeseen consequences. Lost productivity. The list goes on….

eSecurity Planet
AUGUST 22, 2023
Some data protection regulations, including HIPAA and CCPA , require organizations to inform customers when their personal information has been compromised. Eventually, you will have to go hunting for it, at an inconvenient time, and data may get lost if it’s not properly tagged or otherwise categorized.

Security Boulevard
SEPTEMBER 28, 2022
Optus, the second-largest telecommunications company in Australia, has experienced an API security incident – and it might come with a $1 million price tag. That’s the amount being demanded by the attacker who has breached Optus and claims to hold more than 11 million user records.

eSecurity Planet
OCTOBER 28, 2021
Not only do these systems garner heavy price tags, it can be challenging to find and retain highly trained specialists that know how to work with them. For highly regulated industries such as finance or healthcare, they can be the extra measure of protection needed to adequately secure your organization.

Security Boulevard
OCTOBER 6, 2021
My team and I are responsible for building and improving Delphix’s compliance product, which allows our enterprise customers to meet global and regional data privacy regulations while protecting their data against cyber attacks. . I’m an Engineering Development Manager based in the Delphix India office. Employee Spotlight.
Centraleyes
APRIL 16, 2024
Automated classification tags enable the institution to enforce stringent access controls and encryption measures, ensuring the utmost protection for sensitive financial data. Organizations can precisely tailor protective measures by understanding the landscape of sensitive information.

Malwarebytes
MAY 18, 2021
Naturally, the price tag for analyzing malware (free) is appealing to SMBs on a limited budget. This is why many SMBs with compliance regulations, or those with advanced safety protocols, prohibit the use of VirusTotal, and it’s why the service’s home page says clearly: “Please do not submit any personal information.”

CyberSecurity Insiders
JANUARY 6, 2022
Fugue is a cloud security SaaS company enabling regulated companies such as AT&T, Red Ventures, and SAP NS2 to ensure continuous cloud security and earn the confidence and trust of customers, business leaders, and regulators. Connect with Josh on LinkedIn and via Fugue at www.fugue.co. About Fugue.

Centraleyes
FEBRUARY 13, 2024
What happens when several risks carry the same “medium” tag, leaving decision-makers pondering where to focus their attention and allocate precious resources? There were ten in the bed And the little one said, “Roll over! Roll over!” So they all rolled over, and one fell out.

Security Boulevard
SEPTEMBER 1, 2021
tag=Cybersecurity'>Cybersecurity</a> <a href='/blog?tag=Ransomware'>Ransomware</a> tag=Ransomware'>Ransomware</a> <a href='/blog?tag=Cyber-attacks'>Cyber-attacks</a> <a href='/blog?tag=Cybersecurity'>Cybersecurity</a> Additional Resources. Featured: .

CyberSecurity Insiders
FEBRUARY 4, 2022
Fugue is a cloud security and compliance SaaS company enabling regulated companies such as AT&T, Red Ventures, and SAP NS2 to ensure continuous cloud security and earn the confidence and trust of customers, business leaders, and regulators. Connect with Josh on LinkedIn and via Fugue at www.fugue.co. About Fugue.

Security Affairs
OCTOBER 13, 2020
It’s a recipe for manufacturing IoT devices that are too easy to compromise, which is something only governments can solve with strict laws and regulations. To put in simple terms, it refers to the process of providing a web application with JavaScript tags on input. Another issue with input is the cross-site scripting (XSS).
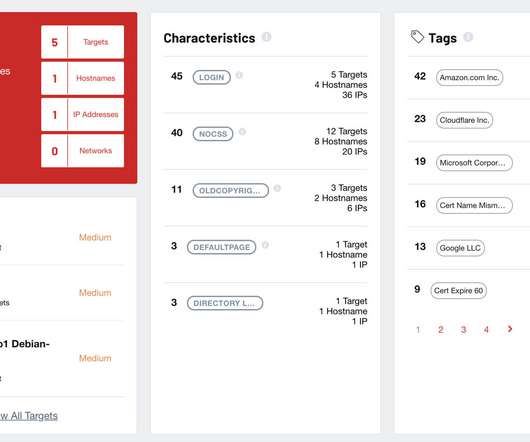
SC Magazine
APRIL 22, 2021
This is especially the case in regulated industries required to remediate all vulnerabilities with a certain score or higher. Many ASM products do this work for you, automatically tagging assets as Linode or AWS if they are owned by these public cloud providers. Is it something we have hosted somewhere? Does it belong to a third party?

Security Boulevard
MARCH 13, 2021
She decides to customize the default analyze command used by ShiftLeft by adding some custom tags. Claire’s command sl analyze --js --app passport-fe --tag app.group=alice-team --tag stage=poc --tag threat_model_id=page-100 --tag classification=sensitive --tag branch=${GITHUB_REF}. stage=poc ?

McAfee
DECEMBER 9, 2020
With the use of native tagging and network flow log analysis, customers can visualize cloud infrastructure interactions including across compute, network, and storage components. Additionally, the platform scans cloud native object and file stores to assess presence of any sensitive data or malware.

Security Boulevard
OCTOBER 6, 2022
The information compromised most often is the highest regulated in today’s business ecosystem – and most concerning is the popularity of sales, financial data, and PII. Identified issues are tagged with severity, business impact, and steps to remediate. Protecting the integrity of that data is a must. .

Thales Cloud Protection & Licensing
APRIL 17, 2024
In another Imperva blog, Hacking Microsoft and Wix with Keyboard Shortcuts , researchers focused on the anchor tag and its behavior with varying target attributes and protocols. Changing regulations Regulations are also changing to accommodate the threats posed by AI.

Security Boulevard
APRIL 17, 2024
In another Imperva blog, Hacking Microsoft and Wix with Keyboard Shortcuts , researchers focused on the anchor tag and its behavior with varying target attributes and protocols. Changing regulations Regulations are also changing to accommodate the threats posed by AI.

Spinone
NOVEMBER 26, 2018
Often the first step is to classify all corporate data and regulate its access, use, and acceptable methods of sharing based on your classification. Each item of data in the organization is tagged with a meaningful description. and the amount of data in any organization is growing all the time.

ForAllSecure
MARCH 29, 2023
An attacker can craft a malicious query that includes a script tag with JavaScript code that steals the user's session token, allowing the attacker to impersonate the user and perform actions on their behalf. Additionally, using API security testing tools can help ensure compliance with security regulations and standards.
Security Boulevard
MAY 2, 2023
using our tag "CryptoScam" (as of this writing we have 3600+ sites on the list -- hosting companies and registrars, please take action!) Daily trading returns using top regulated trading brokers determine the quantum of rewards, which can vary and if there is a negative trading day, there are no rewards.

Daniel Miessler
MARCH 20, 2022
Regulation. Regulation. Regulators will be everywhere. Some teams will tag activity with various labels (OFFSEC, CHAOSOPS, UNKNOWN, ATTACKER22301 etc.) Careers will be more cleanly broken into functions like: Installing things according to regulation and standard. Introduction. Org Structure. Technology.

eSecurity Planet
JUNE 22, 2023
A VLAN number is a label or tag that is applied to certain packets in order to determine their VLAN classification. Network administrators can regulate the flow of traffic within the network by establishing VLAN membership for particular ports. The switch then permits data to be transmitted across ports that are part of the same VLAN.

SC Magazine
MARCH 5, 2021
Today’s columnist, Steve Dickson of Netwrix, says that staying compliant with data privacy regulations like CCPA and GDPR requires storing sensitive data in secure locations. Classify and tag all data. If possible, automatically search through tags, it will help the team find all the data customers require faster.

CyberSecurity Insiders
NOVEMBER 9, 2022
Zscaler data protection can classify and tag sensitive data that contains: Financial statements (accounts payable, stock, liabilities and others). Other regulated data types for your industry. Credit card information. Intellectual property (source code and more). Personal identification numbers (SSN, NIN, tax IDs and others).
SecureWorld News
OCTOBER 12, 2022
Now we're looking at loss prevention in a different way with these RFID tags and readers," Miller said. "So You can just stick one of those RFID tags and if it leaves through this port, which is the only way to get in or out of the place where it is being held, then you're going to know where it is.".

Spinone
DECEMBER 26, 2018
Teams can share files as cloud saved attachments and use the @mentions tags for important conversations. Microsoft Office 365 Security and Compliance In today’s security conscious world with ever increasing compliance regulations such as GDPR, organizations must give their full attention to security and compliance.

eSecurity Planet
JANUARY 30, 2024
Failure to enforce security regulations and implement appropriate encryption may result in accidental data exposure. Compliance & Legal Issues Regulations and compliance requirements for data storage and processing vary by industry and area. Regular reviews, enhanced analytics, and incident response methods improve security.
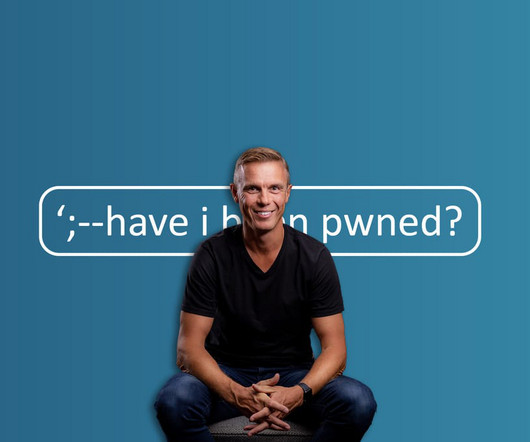
Troy Hunt
DECEMBER 3, 2023
And that's precisely what this 185th blog post tagging HIBP is - the noteworthy things of the years past, including a few things I've never discussed publicly before. And now, a 10th birthday blog post about what really sticks out a decade later. You know why it's called "Have I Been Pwned"?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content