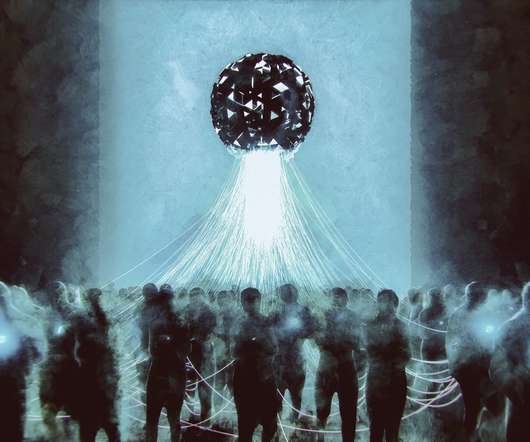
4 ways attackers target humans to gain network access
CSO Magazine
MARCH 30, 2022
Every day, I see the failure in our technology. I remember the infamous email-based computer worm , the “ILOVEYOU virus,” that infected fellow IT friends back in 2000. We hope that our antivirus or endpoint protection software alerts us to problems. I’m sure you see it as well. In reality, it often does not.




















Let's personalize your content