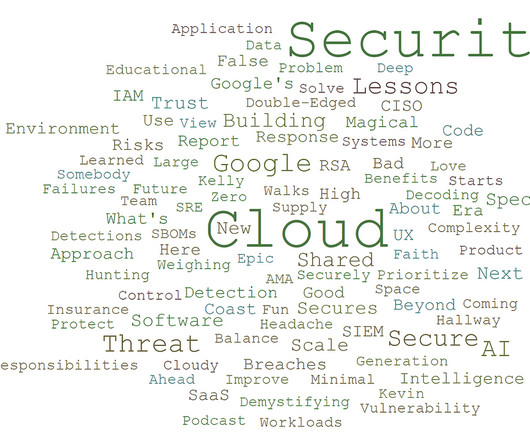
We Are Almost 3! Cloud Security Podcast by Google 2023 Reflections
Anton on Security
JANUARY 10, 2024
So, we ( Tim and Anton , the crew behind the podcast ) wanted to post another reflections blog based on our Cloud Security Podcast by Google being almost 3 (we will be 3 years old on Feb 11, 2024, to be precise), kind of similar to this one. EP109 How Google Does Vulnerability Management: The Not So Secret Secrets!”








































Let's personalize your content