Google TAG warns of Russia-linked APT groups targeting Ukraine
Security Affairs
APRIL 20, 2023
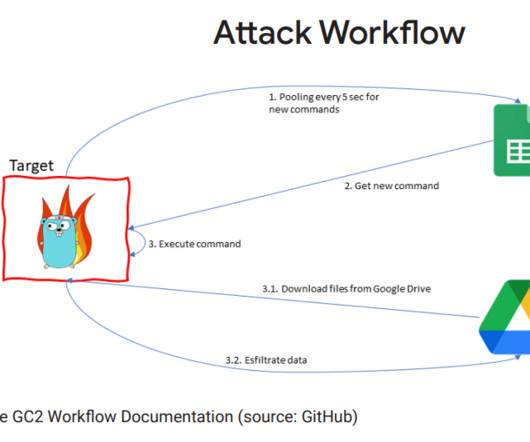
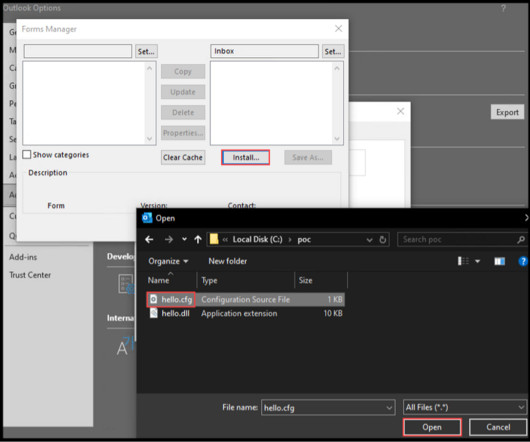
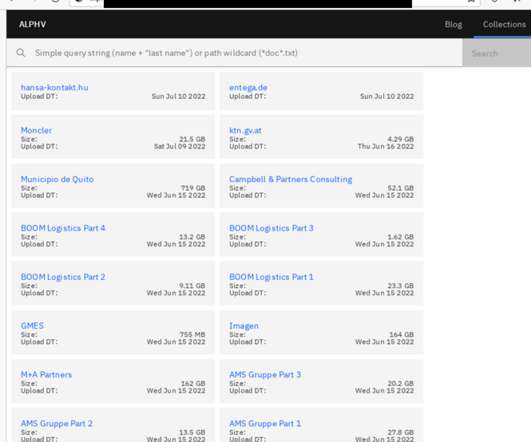
The researchers from Google TAG are warning of Russia-linked threat actors targeting Ukraine with phishing campaigns. Russia-linked threat actors launched large-volume phishing campaigns against hundreds of users in Ukraine to gather intelligence and aimed at spreading disinformation, states Google’s Threat Analysis Group (TAG).






































Let's personalize your content